AES-Matrix ransomware / virus (Removal Guide) - May 2018 update
AES-Matrix virus Removal Guide
What is AES-Matrix ransomware virus?
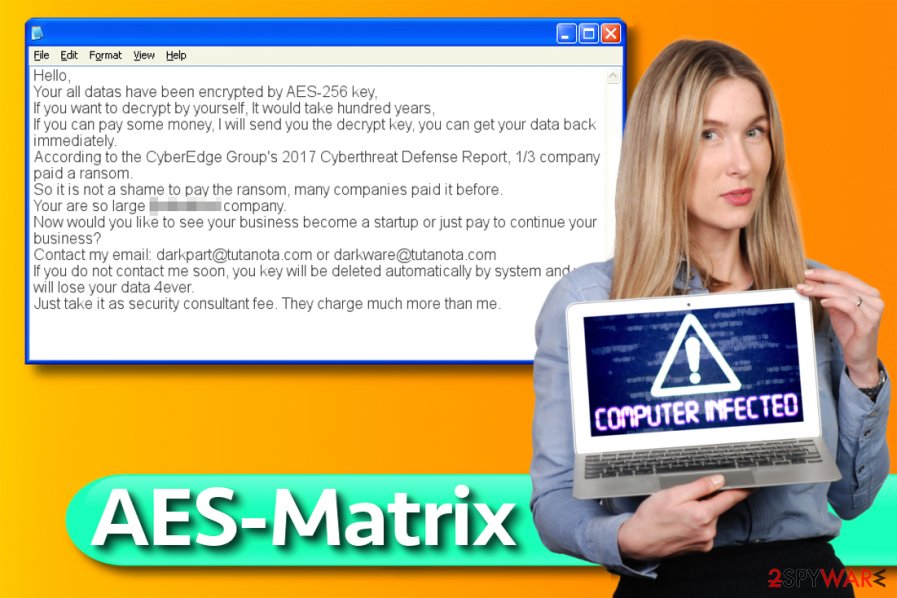
AES-Matrix ransomware is a file encrypting malware that urges users to pay ransom as “it is not a shame”
AES-Matrix is a file-locking virus that was first discovered in July 2017. It mainly targets mid-to-small businesses, although attacks against regular users were observed by security researchers as well. The virus primarily abuses unprotected Remote Desktop Protocol,[1] weak passwords or generally poor security measures to infiltrate machines or networks. The malware seems to be variant of HiddenTear – the open source ransomware platform. However, unlike the mentioned virus, it does not add extensions to encrypted files (it does encrypt files[2] using AES-256[3] cryptography). Consequently, the malicious program composes a ransom note and saves it in folders with encrypted data. The ransom note suggests contacting criminals via darkpart@tutanota.com or darkware@tutanota.com to get help regarding data recovery.
| SUMMARY | |
| Name | AES-Matrix |
| Type | Ransowmare |
| Cipher used | AES-256 |
| Variants | ACCUDATA |
| Contact emails | darkpart@tutanota.com; darkware@tutanota.com; ACCUDATA1@tutanota.com; ACCUDATA2@tutanota.com |
| Decryptable? | No |
| Distribution | Weak passwords, poor security measures, unprotected RDP configuration, etc. |
| Elimination | Download and install FortectIntego or SpyHunter 5Combo Cleaner |
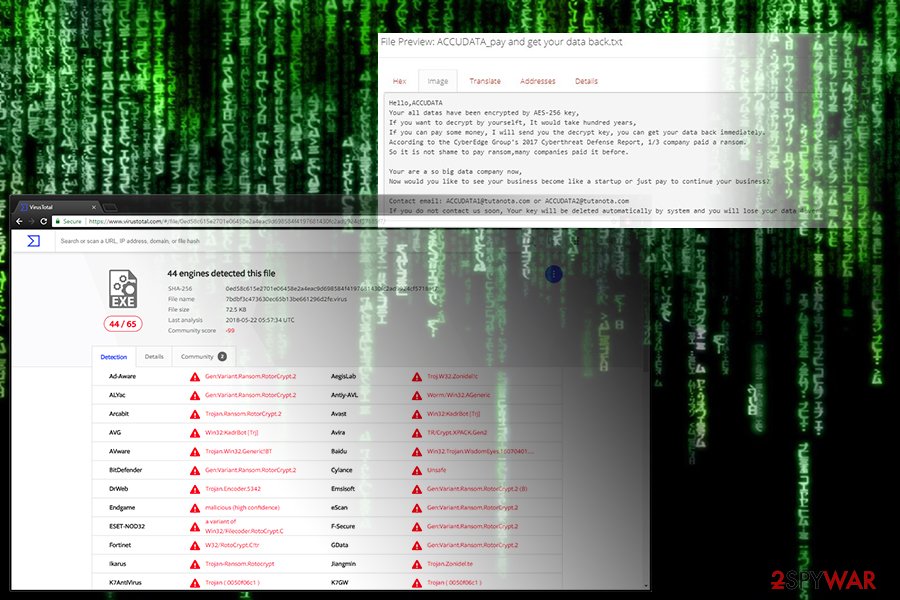
In late May 2018, a new version of AES-Matrix ransomware emerged, dubbed ACCUDATA. It uses same cipher to encrypt files and drops ransom note called ACCUDATA_pay and get your data back.txt. The message is identical to the original, apart that it asks users to contact cybercriminals using ACCUDATA1@tutanota.com; ACCUDATA2@tutanota.com.
AES-Matrix virus renders documents, images, videos and other valuable files useless by changing their structure. The encryption process can be reversed, but only with the help of a decryption key, which is securely stored in criminals’ servers. There is no way to get it from there. The full message of the ransom note is provided below.
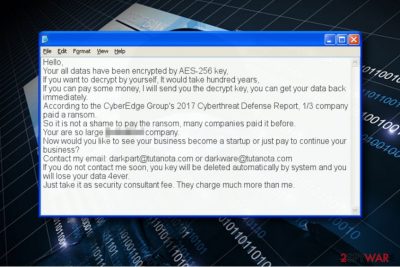
Hello,
Your all datas have been encrypted by AES-256 key,
If you want to decrypt by yourself, It would take hundred years,
If you can pay some money, I will send you the decrypt key, you can get your data back immediately.
According to the CyberEdge Group's 2017 Cyberthreat Defense Report, 1/3 company paid a ransom.
So it is not a shame to pay the ransom, many companies paid it before.
Your are so large […] company.
Now would you like to see your business become a startup or just pay to continue your business?
Contact my email: darkpart@tutanota.com or darkware@tutanota.com
If you do not contact me soon, you key will be deleted automatically by system and you will lose your data 4ever.
Just take it as security consultant fee. They charge much more than me.
It is interesting how hackers taunt users and company owners to pay the ransom, as allegedly to some report, one-third of companies fulfilled crooks' demands and got their data back. It is all a lie, and they are using bogus statistics. Therefore, do not trust people who deceptively infect your machine with malware and then try to convince you that the only way to get files back is by paying the ransom. Do not contact thieves, as you can get your data back using a backup. If you have no backup, we offer some third-party tools that might help with file recovery.
Considering that the virus uses AES encryption only, there is a reason to believe that malware analysts might find a way to decrypt files, especially if the ransomware authors left some mistakes in their code. However, this can still take ages. In the meanwhile, we recommend you to remove AES-Matrix malware.
It is important to eliminate the virus from your computer before trying to use any data recovery methods. You can obliterate the malware from the system using AES-Matrix removal guidances we provided; however, you will still need a decent anti-malware in order to complete the system cleanup. Please remember that ransomware is no regular software and it can’t be uninstalled that easily. In addition, DieViren.de experts[4] point out that this ransomware ISN'T related to Matrix ransomware.
Ransomware distribution peculiarities explained
AESMatrix virus reportedly infiltrates the computer system or network via Remote Desktop Connection (RDP) attacks. RDP allows users to log into a particular Windows computer remotely via RDP client and use the system as if it was local.
- To protect your company from such attacks, use strong passwords (including at least eight characters, upper/lower case letters and digits or symbols) for all accounts but especially for those with Admin’s rights;
- Set your system to block a specific user for a certain period after repetitious unsuccessful attempts to log in. This way, you could interfere the brute-force attack and prevent the attacker from guessing the password that quickly and easily.
- Require two-factor authentication.
Finally, ransomware uses a lot of other techniques to infiltrate systems, for instance, deceptive emails or malvertising. For this reason, we recommend you to enable automatic software updates, stay away from suspicious emails (even if the sender tries to convince you to open an attached resume or an invoice) and protect the entire computer system/network with a decent anti-malware software.
Remove AES-Matrix virus and unlock your files
There is a certain order of tasks you need to complete to remove AES-Matrix virus from your computer or the whole computer network. Firstly, you need to reboot your computer and start it in Safe Mode with Networking regime. This will prevent the malicious processes from starting and allow you to remove the malware without running into unpredicted obstacles.
AES-Matrix removal is required to make the computer appropriate for further use. The automatic spyware/malware tool is recommended because it will delete all of the malicious or potentially unwanted files and programs from the system with ease.
Getting rid of AES-Matrix virus. Follow these steps
Manual removal using Safe Mode
AESMatrix removal should be completed using instructions provided by cyber security experts. You can find their tips below.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove AES-Matrix using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of AES-Matrix. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove AES-Matrix from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Use a data backup to restore files that were corrupted by the AES-Matrix malware. In case you forgot to create a data backup in the past, at the moment all you can do is to try the alternative data recovery options we listed below.
If your files are encrypted by AES-Matrix, you can use several methods to restore them:
Run Data Recovery Pro
Run Data Recovery Pro software to find the compromised files and attempt to restore them. Remember that the software might not be able to recover them – the virus uses a highly sophisticated algorithm to prevent you from using them again.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by AES-Matrix ransomware;
- Restore them.
Examine your computer with ShadowExplorer
We suggest that you check your system with a special tool known as ShadowExplorer. It will help to find and recover files using Volume Shadow Copies. The problem is, many ransomware viruses delete these copies after encrypting the original files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
AES-Matrix decryptor
AES-256.exe is reportedly the decrypter sold by the cyber criminals. However, so far it seems that it doesn't work quite well. That is yet another reason not to pay the ransom!
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from AES-Matrix and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Remote Desktop Protocol. Wikipedia. The Free Encyclopedia.
- ^ Danny Palmer. Locky ransomware is back from the dead again - with new 'Diablo' and 'Lukitus' variants. ZDNet. Technology News, Analysis, Comments and Product Reviews.
- ^ Advanced Encryption Standard. Wikipedia. The Free Encyclopedia.
- ^ DieViren. DieViren. Malware Removal Tutorials.





















