All your data are encrypted! virus (Removal Guide) - 2021 update
All your data are encrypted! virus Removal Guide
What is All your data are encrypted! virus?
All your data are encrypted! is a ransomware that locks all important files on an infected computer
All your data are encrypted! (also known as CryptoApp) is a serious ransomware infection that acts more or less in the same manner as Cryptolocker, CryptoDefense, CoinVault, and other data encrypting programs. Ransomware simply locks the files and demands a ransom if the victim wants to get the decryption key.
Typically All your data are encrypted! ransomware infiltrates computers via spam email attachments that are supposedly brought by Western Union. Although it enters target computers sneakily, there is no doubt that you will soon comprehend its presence. Right after infiltration, it takes time to encrypt sensitive data that is stored on your computer.
After the files are encrypted, the victim can no longer open them. Even after a successful All your data are encrypted! ransomware removal, the data remains locked. But important files can be recovered using backups or other methods listed below.
This ransomware uses the RSA 2048 encryption method and typically adds .encrypted suffix to the files. Successful encryption is always followed by a desktops message.
All your data are encrypted! virus is an extremely dangerous infection because, like other ransomware, it can lock many different files. Down below you can see the list of files that it can affect:
.3fr .3gp .7z .accdb .ai .arc .arw .avi .bad .bay .bmp .cam .cdr .cer .cineon .cr2 .crt .crw .csv .ctl .dat .db .dbf .dcr .der .des .dicom .dng .doc .docm .docx .dsc .dwg .dxf .dxg .eps .erf .fla .flv .fmb .fmt .fmx .gif .hdr .html .iif .img .indd .jpe .jpeg .jpg .kdc .log .lst .m4v .mdb .mdf .mef .mov .mpeg .mrw .nd .nef .nrw .odb .odm .odp .ods .odt .openexr .ora .orf .p12 .p7b .p7c .pbm .pck .pdd .pdf .pef .pem .pfx .pgm .pic .pkb .pks .plb .pls .png .pot .ppm .pps .ppt .pptm .pptx .prn .psb .psd .pst .ptx .qba.tlg .qbm .qbr .qbw .qbw.tlg .qbx .qby .qfx .r3d .raf .rar .raw .rdf .rdo .rep .rex .rtf .rw2 .rwl .sql .srf .srw .sti .sxi .tiff .txt .vdi .wb2 .wpd .wps .xbm .xlk .xls .xlsb .xlsm .xlsx .xml .yaml .zip .php .css .asp .cpp .c .js .pl .perl .swf .aspx .potx .potm .ppam .ppsx .ppsm .sldx .sldm .thmx .xlam .xltm .dotm .dotx.
Hackers demand to pay 2 Bitcoin for the decryption. 2 Bitcoin ransom or approximately 468$ is a considerable amount of money for a supposed decryption key; however, your personal data, including pictures and videos may be much more valuable than that. That's why you should always have backups on other devices or servers.
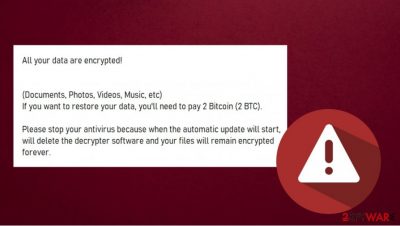
Some victims do not have backups and therefore begin to think that a ransom should be paid. But no matter how intimidating the All your data are encrypted! ransomware message looks, it is better to delete the virus and try to recover at least some of the files in other ways. If you are wondering how a notification looks like, there is the example:
All your data are encrypted!
(Documents, Photos, Videos, Music, etc)
If you want to restore your data, you'll need to pay 2 Bitcoin (2 BTC).Please stop your antivirus because when the automatic update will start, will delete the decrypter software and your files will remain encrypted forever.
If, however, you still think that perhaps you should pay a ransom, think again. You should consider the risk as well. By paying the ransom to scammers, you will have to disclose your credit card details and other sensitive information, as a result, your bank account may be soon cleaned out.
The only solution for this would be a full system check with a reputable anti-spyware that will remove CryptoApp ransomware. We recommend using SpyHunter 5Combo Cleaner or Malwarebytes. After that, try restoring files using backups or other methods. Your system may also need to be repaired, so FortectIntego or any other fixing tool will come in handy.
Ransomware can lock all important files, so try to avoid infection in the future
Ransomware may show up on your desktop unexpectedly. You may find yourself in a serious deadlock if you have no backups of your data and no money. However, even if you pay the ransom, there is no guarantee that you will receive a decryption key.
Speaking about ransomware infections, it noteworthy that there is no hundred percent security protection from such infections. Nevertheless, there are some precautionary measures that you can take.
First of all, never visit illegal, corrupted, and pornographic websites because they may be full of Trojans and other ransomware transmitters. Moreover, be extra careful with email messages because spam is by far the most frequently used medium for ransomware distribution. DO NOT open attachments of the messages from unknown senders, that contain various mistakes, and simply seems suspicious.
Remove All your data are encrypted! virus and only then try to recover your files
For All your data are encrypted! removal, you can use the guide below. Nevertheless, right after cleaning your machine, try to think about the immunity of the data that you store on your PC. The best way to keep important data safe is to make backups regularly and for that, the best storage is one or several of these:
- USB external hard drives,
- CDs,
- DVDs,
- cloud storage, such as Google Drive, Dropbox, Flickr, etc.
We hope that after you successfully remove All your data are encrypted! ransomware, you will no longer encounter similar infections. Remember not only to be careful on the internet but also to always have a powerful antivirus program turned on. We recommend using SpyHunter 5Combo Cleaner or Malwarebytes.
Also, if you feel that your computer is running slower than before or that it is experiencing various errors, you may need to repair system files. You can easily perform such a task with this FortectIntego or similar tool.
Getting rid of All your data are encrypted! virus. Follow these steps
Manual removal using Safe Mode
If you want to eliminate CryptoApp ransomware, you may need to enter Safe Mode with Networking
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove All your data are encrypted! using System Restore
System Restore can be useful for threat deletion
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of All your data are encrypted!. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove All your data are encrypted! from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by All your data are encrypted!, you can use several methods to restore them:
Using Data Recovery Pro might be helpful too
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by All your data are encrypted! ransomware;
- Restore them.
Try to recover locked files with Windows Previous Version
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Recover data by using Shadow Explorer
If Shadow Volume Copies are still intact, meaning they weren't deleted or encrypted by the ransomware, then Shadow Explorer might be a helpful data recovery tool.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from All your data are encrypted! and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.





















