Antivirus Action (Removal Guide) - 2021 update
Antivirus Action Removal Guide
What is Antivirus Action?
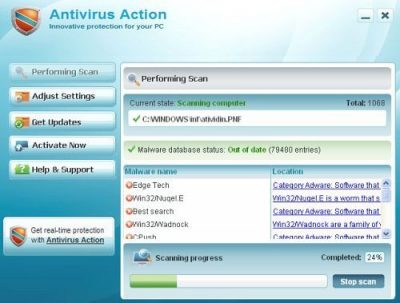
Antivirus Action – fake antivirus software that tries to scam you by showing bogus alerts on your screen
Antivirus Action is high-risk rogue spyware that appears to be created after its infamous forerunner Security Suite which is known to have infected thousands of PCs. The app is presented as a useful tool that would protect and detect various parasites, including Trojans, rootkits, viruses, ransomware, etc.
However, the program is considered to be scareware that infects a Windows computer and shows users fake notifications about malware infections. The goal of these alerts is to make victims purchase a fake license for this software, consequently resulting in financial losses, so make sure you never buy it. If you have found Antivirus Action performing scans on your device, you should immediately take care of its removal.
| Name | Antivirus Action |
| Type | Rogue antivirus, malware |
| Operation principle | Takes over Windows and shows fake notifications about malware infections, constantly threatening users in various ways. They are then prompted to buy the program's “license,” making victims spend money on this malicious program |
| Danger | Monetary losses, installation of other malware, redirects to malicious websites via the browser, personal data disclosure etc. |
| Removal | Rogue anti-spyware software can be difficult to eliminate, so accessing Safe Mode with Networking and using SpyHunter 5Combo Cleaner or another reputable anti-malware might be necessary |
| System fix | If you start experiencing crashes, errors, BSODs and similar issues after malware elimination, it is a sign that Windows files were corrupted during the infection – rely on FortectIntego to fix that for you |
The program is usually distributed through fake video codecs or misleading online scanners, which can be found on various malicious websites on the internet. Similar scareware and fake anti-spyware apps such as BlockDefense, WiniFixer, and PC Antivirus Pro use identical tactics for distribution.
Once installed, malware would change Windows completely – some system files might also be affected and damaged during this time. This might cause system instability and crashes later. If that is the case for you, perform a full system scan with FortectIntego to fix virus damage automatically after Antivirus Action removal.
The malware is equipped with not only typical capabilities, such as secret infiltration, annoying system scanners, or fake alerts. Here are a few examples of what can it do once the infection is complete:
- Completely prevent users from accessing most websites online
- Redirect to malicious websites as soon as the browser is opened
- Enable itself to be booted with every Windows launch
- Block all security and other beneficial software, detecting it as malicious, etc.
AntivirusAction starts its misinformation stage where infected system is completely bombarded by virus detection alerts. These notifications continuously interrupt when people browse the web, and every time they appear they declare about numerous viruses detected, for example:
Security Warning
Application cannot be executed. The file notepad.exe is infected. Do you want to activate your antivirus software now.
Windows Security Alert
Windows reports that computer is infected. Antivirus software helps to protect your computer against viruses and other security threats. Click here for the scan your computer. Your system might be at risk now.
Program creators' strategy is clear and obvious: being a commercial project, it asks paying the money for its so-called services and offers you to update to its Lite, Standard, or Ultimate “versions.” However, this scam has no spyware detection or removal engine, so it won’t be able to remove any computer virus.
In addition to the above-mentioned facts, this virus has a great impact on the computer’s performance, so you should eliminate it as soon as it gets on your computer. It’s highly recommended to use reliable anti-spyware (for example, SpyHunter 5Combo Cleaner) and remove Antivirus Action with all its additional files.
Do not believe fake online alerts
Online scams are particularly prevalent, and cybercriminals use social engineering to make them more believable. They often use familiar brand names, logos, formatting, and other attributes that can be easily interconnected with well-known companies, such as Microsoft or Google. Sadly, many people fail to recognize fakery and believe that these notifications are alerts are real. Consequently, they end up disclosing their personal information, purchase useless software or install malware on their systems.
Therefore, your first line of defense is a robust security program that has real-time security features and web protection enabled. Most of such apps would recognize deception and would show a warning if a malicious website is accessed. Besides, you should also stick to official websites when trying to download software or its updates – a suspicious URL is what can easily tell you that the site is not legitimate, even if it may look like one.
Restore your LAN settings and delete the infection in Safe Mode
When trying to eliminate this infection, you may find yourself disabled from the Internet. Here are some special notes to bring it back and remove Antivirus Action:
- Access Safe Mode with Networking as explained below
- Open Internet Explorer. Click on the Tools menu and then select Internet Options.
- In the the Internet Options window click on the Connections tab.
- Then click on the LAN settings button.
- Now you will see Local Area Network (LAN) settings window. Uncheck the checkbox labeled Use a proxy server for your LAN under the Proxy Server section and press OK.
Finally, perform a full system scan with SpyHunter 5Combo Cleaner and then fix virus damage automatically with FortectIntego repair software. Otherwise, you might have to reinstall Windows altogether.
Getting rid of Antivirus Action. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
How to prevent from getting rogue antispyware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.














