Crypto-Blocker ransomware / virus (Easy Removal Guide) - Decryption Methods Included
Crypto-Blocker virus Removal Guide
What is Crypto-Blocker ransomware virus?
Crypto-Blocker ransomware is blackmailing people and threatening to damage their computers
Crypto-Blocker is a new file-encrypting virus that uses AES[1] ciphers to make files on the targeted computer inaccessible. Malware appends .corrupted file extension to encrypted files and delivers a ransom note on the lock screen. The ransom-demanding message informs about necessity to pay 10 euros, dollars or pounds within 5 hours. Otherwise, affected computer might crash. However, if you see this threatening message, you should not panic and focus on Crypto-Blocker removal. Cyber criminals often use psychological terror to make people pay the ransom. Though, they usually are unable to damage the device or delete encrypted files. However, you should not waste your time and employ professional malware removal program. We suggest scanning your device with FortectIntego and remove Crypto-Blocker with the help of it.
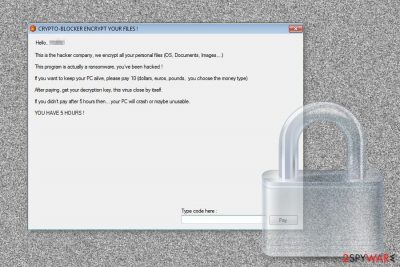
In the ransom note, developers of the Crypto-Blocker ransomware presents themselves as the “hacker company.” These shady people use a vivid language to scare victims. The threatening message informs that if users want to keep their computers “alive” they need to pay 10 euros, dollars or pounds. However, hackers are understanding and allow victims to choose other currency if they need to pay the ransom. Indeed, it’s unusual behavior because crooks often are strict about ransoms. However, they give a short amount of time to make the payment – only 5 hours. Once victims transfer the money, they receive a code that they need to enter into the box at the bottom of the lock screen. Then, all their files should be decrypted, and Crypto-Blocker deleted from the system. Otherwise, people might face even more problems. According to the crooks, if they will not receive a ransom on time, the affected computer might crash or become “unusable.” Undoubtedly, the payment is small, and you might feel that it’s worth to take the risk. However, we do not recommend spending such money and sponsoring further cyber crimes. Even one dollar is a motivation for cyber criminals to work harder and create bigger illegal projects, and your files might be still left encrypted.
Ransomware distribution and infiltration strategies
It’s unknown what specific technique is used for the circulation of Crypto-Blocker virus. Probably, cyber criminals use traditional ways to spread it, for instance, malicious spam emails, malvertising,[2] fake updates, and exploit kits. Thus, if you want to avoid ransomware, you should take precautions, make data backups and be careful when browsing the Web. First of all, do not rush opening attachments or clicking links (or buttons) provided in the unknown email. Crooks might send emails where they pretend to be from banks, online shops and other reputable companies or organizations, and easily trick you into opening an infected content. Crypto-Blocker might be installed on the device as soon as you click on obfuscated word or pdf document, amazing shopping offer or any online ad. Bear in mind that this content might look legitimate and safe, so you should be critical and do not take any harsh actions. Finally, you should keep your software updated and strengthen your computer’s security with professional security program.
Deleting Crypto-Blocker ransomware virus from the computer
We recommend victims to remove Crypto-Blocker as soon as they receive a ransom demanding message. Virus elimination is completed using a powerful malware removal programs, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. However, you might not be able to install such programs easily. Malware might prevent you from simply downloading it. Thus, you may need to disable the ransomware first by rebooting computer to the Safe Mode with Networking as explained in the instructions below. Then, you should be able to install your chosen software, update it and run a full system scan. Automatic Crypto-Blocker removal assures that all ransomware-related entries are deleted from the computer entirely, and cyber criminals cannot cause any other damage to you.
Getting rid of Crypto-Blocker virus. Follow these steps
Manual removal using Safe Mode
If Crypto-Blocker prevents from installing or accessing malware removal program, reboot your device to the Safe Mode with Networking and then try again.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Crypto-Blocker using System Restore
System Restore is another method to disable the virus. Bear in mind that disabling is not the same as removing malware. Thus, you need to scan the device with security program as well.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Crypto-Blocker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Crypto-Blocker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Currently, the only safe and effective way to restore files is to use data backups. If you do not have them, please try alternative methods presented below. Hopefully, they will help you!
If your files are encrypted by Crypto-Blocker, you can use several methods to restore them:
Data Recovery Pro tool might help to restore files encrypted by Crypto-Blocker
This professional software is designed to restore accidentally deleted, corrupted and some of the encrypted files. Thus, it might help to rescue your files as well.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Crypto-Blocker ransomware;
- Restore them.
Windows Previous Versions feature might also be useful in data recovery
Windows Previous Versions feature allows traveling back in computer's time and accessing previously saved versions of the encrypted files. However, this method only works if System Restore function has been enabled before ransomware attack, and you need to restore only a few files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might help to restore files encrypted by Crypto-Blocker ransomware
It's unknown whether malware can delete Shadow Volume Copies of the encrypted files or not. If these files are left on the system, you could use the help of the ShadowExplorer.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Crypto-Blocker Decryptor is not available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Crypto-Blocker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Advanced Encryption Standard. Wikipedia. The free encyclopedia.
- ^ Vangie Beal. Malvertising. Webopedia. Online Tech Dictionary for IT Professionals.





















