M4N1F3STO virus (Free Guide) - Decryption Methods Included
M4N1F3STO virus Removal Guide
What is M4N1F3STO virus?
M4N1F3STO fakes ransomware attack and tries to steal your money
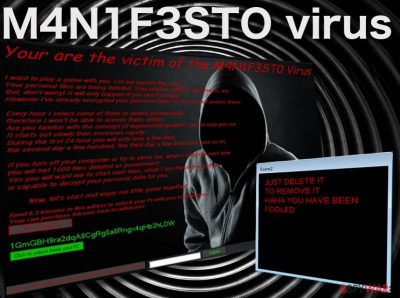
M4N1F3STO virus is one of those nasty screenlocker-type [1] computer infections designed to imitate ransomware attacks and swindle users out of their money by selling them fake data decryption keys. For those unfamiliar with leet speak [2], the virus title decodes as MANIFESTO. The bogus ransomware usually lacks a lot of the malicious functionalities that the real ones possess.
In other words, everything that is written in the ransom note should be ignored as all the made claims are false. Your files are not actually encrypted, and they won't be deleted either, so to not pay the demanded 0.3 BTC for the alleged decryptor. Instead, you can enter a password that can be found in a Tweet made by a security researcher and then remove malware from your system.
| Name | M4N1F3STO ransomware |
| Type | Screenlocker |
| Ransom size | 0.3 BTC |
| Operation | Blocks access to normal computer functions with a lock screen and demands ransom to be paid. Does not encrypt files and does not provide a working decryptor; claims about data being deleted from the computer are also fabricated |
| Removal | Get rid of ransomware by performing a full system scan with SpyHunter 5Combo Cleaner or another |
| System fix | Malware can damage Windows files, resulting in system crashes or errors. To fix these problems, we recommend using FortectIntego repair software |
There is plenty of deception when it comes to this ransomware, as it does not actually encrypt the infected computer files but merely drops a threatening lock screen whenever the victim attempts to launch the system. This lock screen obstructs the victim from booting the system properly and accessing the data stored on the device.
Consequently, the victims remain unaware of the fact that, in reality, no encryption process ever took place and that the extortionists are only playing tricks to get them to pay for the non-existent decryption tools. You can see the content of the lock screen message below:
I want to play a game with you. Let me explain the rules:
Your personal files are being deleted. Your photos, videos, documents, etc…
But, don't worry! It will only happen if you don't comply.
However I've already encrypted your personal files, so you cannot access therm.
Every hour I select some of them to delete permanently,
therefore I won't be able to access them, either.
Are you familiar with the concept of exponential growth? Let me help you out.
It starts out slowly then increases rapidly.
During the first 24 hour you will only lose a few files,
the second day a few hundred, the third day a few thousand, and so on,
If you turn off your computer or try to close me, when i start the next time
you will het 1000 files deleted as punishment.
Yes you will want me to start next time, since I am the only one that
is capable to decrypt your personal data for you.
Now, let's start and enjoy our little game together!”
1GmGBH9ra2dqA8CgRg8a8Rngx4qHb2hLDW
Send 0,3 bitcoins to this adress to unlock your Pc with your email adress.
Your can purchase bitcoins from localbitcoins
Luckily, the threats in this note remain in their written form, and no actual data destruction occurs, even if the user refuses to follow the extortionists’ rules. In fact, this is exactly what you should do if you ever in such a situation – remove the virus from your device as soon as possible. We suggest doing that with the help of sophisticated malware-fighting tools, such as FortectIntego.
At this point, you might be wondering what you should do about the lock screen. How do you scan your PC with an antivirus utility when you cannot access your desktop or any programs installed on the computer? The virus analysts have found a way to bypass this obstacle already.
They have examined the program’s source code and found that the M4N1F3STO lockscreen removal code can be extracted from the virus executable. Thus, you don’t have to pay the demanded 0.3 Bitcoin [3] for the supposed data decryption. Instead, you can access your desktop and take care of the malware removal.
Malware spreading tactics and avoidance tips
There is currently no information about how the virus attacks computers. But we can presume that it either spreads via malicious spam email attachments [4], corrupt ads, or gets downloaded on the computer disguised as software updates or legitimate applications.
Nevertheless, the files found on the computer after the attack leads us to believe that the virus arrives on the computer mostly through spam. The malicious WindowsApplication1.exe and Receipt.exe files feature titles inconspicuous enough to be downloaded by regular users without suspecting about their malicious nature [5].
This only proves how easily malware can enter a computer. Hence, any content that may potentially reach our computers should be carefully investigated and examined with software specialized for malware detection.
The best M4N1F3STO removal approach
In case your device has been affected by this fraudulent ransomware-imitating infection, don’t hesitate for a second and remove the M4N1F3STO virus from your computer. To do that, you will first have to terminate the lock screen, and only then will you be able to access the antivirus tool required for the virus extermination.
If our previously indicated lock screen termination code does not work, check out a couple of alternative lockscreen removal instructions below. Finally, when every obstacle is eliminated, you can proceed with a malware elimination.
Getting rid of M4N1F3STO virus. Follow these steps
Manual removal using Safe Mode
Enter the unlock code provided in a Twitter post to the box next to the “Submit” button on the lock screen. Then, run the system scan immediately and clear the Windows Registry.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove M4N1F3STO using System Restore
If you manage to enter your browser through the links provided on the lock screen:
- Type in “C:/windows/explorer.exe” instead of the current URL (file///C:/windows/explorer.exe on Mozilla Firefox)
- Click Enter and agree with the download that is initiated
- When the file downloads, you may be able to access your Computer catalog
- From this point, you have to go to your C: disk, click Windows and locate Explorer.exe
- The Windows task bar will appear in which you can search for Command Prompt or Windows Task Manager
- If you are allowed to enter Windows Task Manager, you can terminate the suspicious processes by selecting them and clicking End Task.
- In case the virus blocks you from accessing this program, you may as well disable the malicious process (WindowsApplication1.exe or Receipt.exe) by enter “tasklist” command into the Command Prompt and press Enter. Then, find suspicious processes and enter “taskkill/ im [suspicious process title]” in the command line below. Click Enter to confirm.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of M4N1F3STO. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove M4N1F3STO from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by M4N1F3STO, you can use several methods to restore them:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from M4N1F3STO and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Jake Doe. ScreenLocker virus. How to Remove?. 2-spyware latest virus news.
- ^ Tina Hampton. Know the Term: Leetspeak. Networking exchange blog.
- ^ Christina Rexrode. Bitcoin basics: What you need to know. Market watch news site.
- ^ Chris Hoffman. How To Spot A Dangerous Email Attachment. Make use of. Technology simplified.
- ^ Antivirus scan for Receipt.exe. Virustotal: antivirus scan reports.





















