West Yorkshire Police Ukash (Free Instructions)
West Yorkshire Police Ukash Removal Guide
What is West Yorkshire Police Ukash?
West Yorkshire Police Ukash – scammers pretending to be police officers
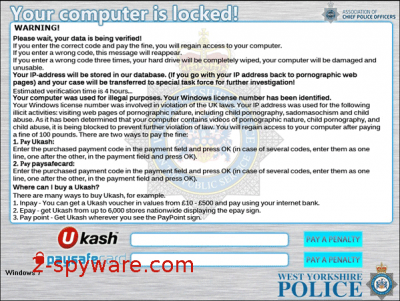
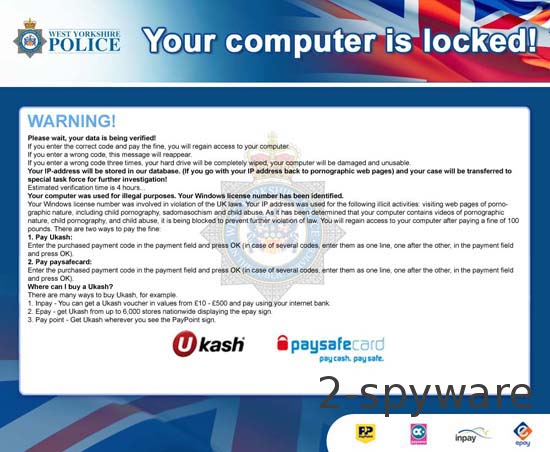
West Yorkshire Police virus is classified as a ransomware scam. There are many similar scams actively spreading around that all lock computers down with officially-looking alerts and notifications. They all mention local police offices or governmental organizations in these warnings and list some laws that a user has supposedly violated.
Typically, the victim is accused of doing some criminal activity, like watching pornography, spreading copyrighted content, or even distributing malware. To make this even more real and make you pay 100 pounds as a fine, West Yorkshire Police virus also displays your IP and hostname.
| name | West Yorkshire Police Ukash |
|---|---|
| type | Ransomware, scam |
| Risks | Money loss, privacy issues |
| Distribution | Spam emails, file-sharing platforms, fake Flash Player updates, software bundling, etc. |
| Elimination | Remove this cyber threat by scanning your device with a reliable anti-malware tool |
| System fix | To recover from the damage that this ransomware caused to your system files and settings, please use the FortectIntego system diagnostics tool |
Before you start believing this alert, you need to know that all this story is a huge scam. Police do not send this kind of letter, and they do not ask you to pay a fine by locking your computer. Remove this infection from your device with our comprehensive guides below.
Like other Ukash threats, West Yorkshire Police virus is distributed through fake video codecs, software bundling, deceptive ads, fake Flash Player updates, and methods alike. Besides, some people mentioned that torrent files and officially-looking spam letters could also easily lead you to the infiltration of this virus.
So, if you receive an email from your local police or other institution, be very careful when opening it because you may get infected. When it gets inside the system, this ransomware virus blocks the whole system and replaces the desktop with its fake notification.
Please, never fall for this threat because you will simply give your hard-earned money away to cybercriminals. You can easily remove this cyber infection with a trustworthy anti-malware tool such as Malwarebytes or SpyHunter 5Combo Cleaner. Download, install, update, and perform a full system scan with either of these tools to safely remove any infections.
If West Yorkshire Police ransomware prevents you from visiting security-related pages (downloading proper AV software) or launching security software, please use our free instructions below to do that in Safe Mode with Networking. In some cases, ransomware is capable of doing that by altering various system files and settings.
After infection removal, the modifications done by the virus could result in various abnormal behavior exhibitions by your device, including BSoDs, severe lag, and other system failures. You can resolve all system irregularities by running system diagnostics with the FortectIntego PC repair software.
Getting rid of West Yorkshire Police Ukash. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from West Yorkshire Police Ukash and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.














