Yyto ransomware / virus (Removal Guide) - updated Sep 2018
Yyto virus Removal Guide
What is Yyto ransomware virus?
Yyto ransomware — a dangerous cryptovirus that has been active since July 2018
Yyto is a ransomware virus that encrypts files and demands ransom for the alleged decryption key. This virus encodes data with AES-256 cryptography[1] and marks it with .YYTO file extension[2]. This cryptovirus already has a few versions discovered and the last one appends the .davilarita@mail.com.yyy0 file extension to the encrypted data. This version is already the fifth one discovered in these two months of 2018. Yyy0 ransomware encrypts files using the same AES encryption method and delivers a ransom note in a file named as help.txt that contains an offer to test decryption of several encrypted files. You shouldn't do that. Unfortunately, any contact between you and these hackers cannot lead to positive results.
| Name | Yyto |
|---|---|
| Type | Ransomware |
| Danger level | High. Makes files useless, demands ransom. Can lead to permanent money and data loss. |
| Encryption | AES-256 |
| Extension | .codyprince92@mail.com.ovgm; .YYTO; .b007; .adapaterson@mail.com.mkmk; .davilarita@mail.com.yyy0 |
| Ransom file | help_to_decrypt.txt; read_to_txt_file.yyt ; help.txt; encrypt.txt; Readme.txt |
| Contact email |
|
| Distribution | Insecure spam email attachments |
| Removal | Best tool for removing ransomware is FortectIntego |
Since the release of the original version of the Yyto, developers have presented a bunch of new versions of the virus. The main difference is the appended file extension, used contact email address and titles of the ransom notes. Currently, it is known that this ransomware family provides identical data recovery instructions. The ransom note is supposed to be one of these files:
- help_to_decrypt.txt;
- read_to_txt_file.yyt;
- help.txt;
- encrypt.txt;
- Readme.txt.
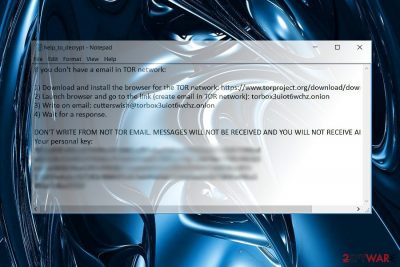
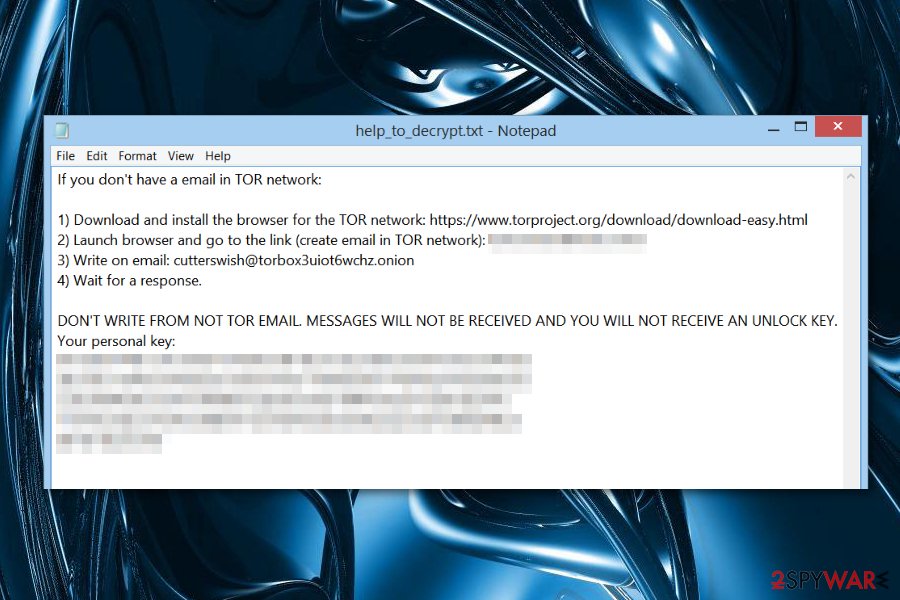
All of these documents begin with the following text:
Hello. Your files have been encrypted.
For help, write to this e-mail: codyprince92@mail.comAttach to the letter 1-2 files (no more than 3 MB) and your personal key.If within 24 hours you have not received a response, you need to follow the following instructions:
Unlike other crypto-malware, Yyto virus refers to an .onion link which leads to TorBox. According to the information provided on its homepage, it is a secret email domain designed for communication and separated from the public net. It should ensure the anonymous connection between a perpetrator and a victim.
It doesn’t matter which version of ransomware attacks the computer; the instructions remain the same. Victims should contact the cyber criminals via cutterswish@torbox3uiot6wchz.onion, isabell@torbox3uiot6wchz.onion, albertkerr94@mail.com or colecyrus@mail.com email address.
Usually, perpetrators provide Tor or Bitcoin wallet address for collecting ransoms. In this case, the authors behave differently. Instead, they opt for Torbox. However, neither of the ransom notes provide the actual sum of money that victims have to pay in order to get back their files. However, contacting criminals and following their further instructions is not recommended.[3] It may lead to the money loss, so it’s better to proceed to Yyto removal.
Users are advised to remove Yyto virus using powerful and reputable malware removal program, such as FortectIntego or Malwarebytes. However, if you cannot install or run security software, you should scroll down to the end of the article and learn how to disable the virus first.

Developers of Yyto ransomware constantly come up with new versions
.read_to_txt_file.juuj file extension virus. The first variant of the Yyto malware appeared at the beginning of July. The ransomware uses the same AES cryptography but appends a new file extension – .read_to_txt_file.juuj. It delivers a ransom note in the help.txt file and asks to contact via isabell@torbox3uiot6wchz.onion to get data recovery instructions.
.m5m5 file extension virus. The second version of the virus has been released in September. Since then crypto-malware adds .m5m5 file extension to corrupted audio, video, image and other targeted files. This time ransomware drops either help.txt or encrypt.txt files with recovery instructions. There’s nothing new in hackers' demands. Victims have to contact them via albertkerr94@mail.com to learn about recovery possibilities.
Colecyrus ransomware virus. The latest version of the Yyto malware appends .b007 file extensions to prevent users from opening their files. The virus uses an unbreakable AES-CBC cryptography. Even though criminals offer data recovery possibility in Readme.txt file, victims are not advised contacting crooks via colecyrus@mail.com address and paying demanded sum of Bitcoins.
.codyprince92@mail.com.ovgm file extension virus. In June 2018, a new version of Yyto ransomware was discovered and this time new “.codyprince92@mail.com.ovgm” extension is added for files after encryption. Ransom message delivered in “Readme.txt” file and contact email codyprince92@mail.com is now also on the list. Ransomware viruses are dangerous enough so you should not contact these people. But it is more harmful because Yyto is evolving and new version after version come to the public. These new ransomware variants are even more dangerous than the previous.
yyy0 ransomware is the newest variant of Yyto that emerged in September 2018. It has file extension .davilarita@mail.com.yyy0 which is added to encrypted files after the process is done to mark encoded files from other ones. In every folder with encrypted data virus places ransom file help.txt that contains instructions on creating the cryptocurrency wallet, so you can pay the ransom. We always advise you not to do so. Ransomware file is detected by 51/69 AVs[4], so you can remove this threat using your antivirus or anti-malware tools like FortectIntego and SpyHunter 5Combo Cleaner.
Ransomware comes with spam email attachments
Despite dozens of written articles about Yyto ransomware and their distribution ways, spam emails remain the most popular method of transmission. Ransomware executable is wrapped into .zip folder and presented as supposed invoice or package delivery information. Security experts from Finland[5] warn to be careful with received emails and stay away from letters that are sent from the unknown sender and includes attachments.[6]
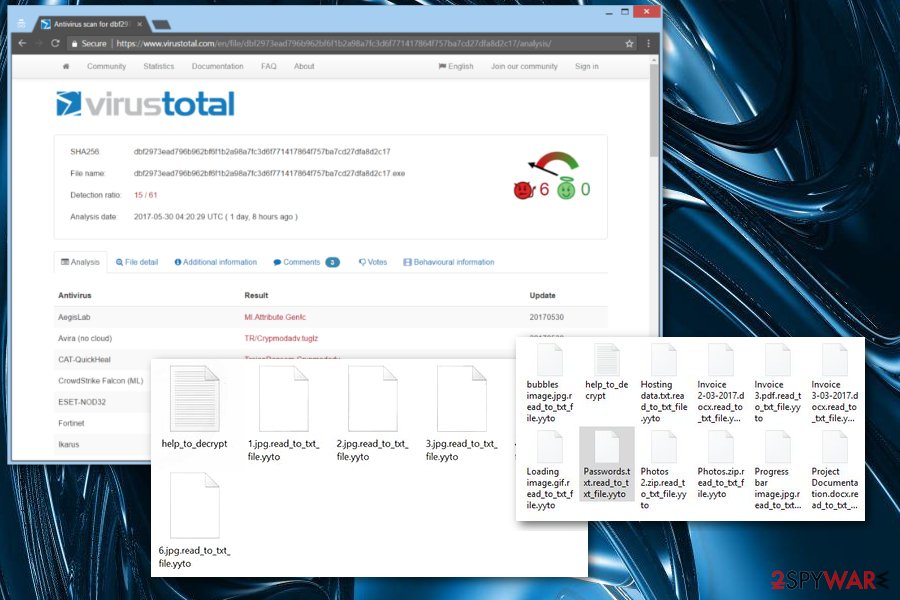
Speaking of which, the virus also disguises its executable in 2.exe or RS01bz.exe file. Note that the trojan which may be identified as TR/Crypmodadv.tuglz, Win32.Trojan.WisdomEyes.16070401.9500.9945, or Spyware (004c76c01) delivers Yyto hijack payload as well. Thus, mere vigilance is not sufficient in securing your computer and personal data from virtual threats. Install an anti-virus and anti-spyware tools to fortify the protection.
Removal of the Yyto ransomware virus is crucial for the PC
Data recovery always seems the most important task after the ransomware attack. However, it's not quite true. It's crucial to perform Yyto removal as soon as launches the attack. Malware might cause various system changes, alter Windows registry or install malicious programs. Therefore, you won't be able to use your computer normally and safely again.
In order to remove Yyto virus correctly, you have to obtain a reputable malware removal program, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. If your computer security tool is forcefully shutdown, you may benefit from below instructions. After restoring the access, you will be able to finish Yyto removal.
Getting rid of Yyto virus. Follow these steps
Manual removal using Safe Mode
It is very unlikely that the malware intervenes with the processes of a computer security application. If it does actually, proceed to the following instructions and restart the computer in Safe Mode.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Yyto using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Yyto. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Yyto from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Yyto, you can use several methods to restore them:
The effectiveness of Data Recovery Pro
You may try using this tool for data recovery in case you have run out of options.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Yyto ransomware;
- Restore them.
What is Windows Previous Versions?
This integrated function allows recovering the file by using its last autosaved copy. Note that the method only works when System Restore is enabled.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Opting for ShadowExplorer
The program employs shadow volume copies to restore the files. Since there is no information that the malware deletes them, you may benefit from this mode.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Yyto decryptor is not available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Yyto and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ AES. Webopedia. Online Tech Dictionary.
- ^ Karsten Hahn. YYTO ransomware. Twitter. Online source for news and sharing experiences.
- ^ Mathew Hughes. Economists have figured out how to extract the most profit from ransomware. TheNextWeb. News, reviews and comments for IT professionals.
- ^ Ransomware analysis. Virustotal. Cybersecurity community.
- ^ Spam and phishing emails – tips to identify them. NAB. The Official NAB News Page.
- ^ Virukset. Virukset. Finish security news.





















