How to remove flooders
Flooders are malicious programs used to overload the normal communication of the Internet/Network and decrease the overall performance of the infected PC system. If a target computer is a server, such malware can cause Denial of Service (DoS) attacks, Ping of Death, ICMP, HTTP overload and similar issues. Each of these problems is typically initiated by sending multiple information packets to the system and blocking the connection to it.
Beware that not all versions of flooders are equal. Some of them are designed very similarly to Trojan horses that act as hacking tools. Such versions of flooders can be used for getting remote access to the target computer system and steal data from it. Once the attacker gets an ability to connect to the target computer, it can steal sensitive information from the victim (passwords, bank logins, credit card information, etc.), modify needed system’s components and even install additional malware on it.
The sooner you remove the Flooder virus from the system, the better. Security experts recommend using reliable security software for removing such malware and similar potentially unwanted software to decrease all possible risks related to computer’s security. Flooders, just like the most of computer threats, do not provide “Uninstall” option and try to hide their files deep inside the computer to prevent their removal. That is why the automatic removal option os highly recommended. Beware that some versions of flooders may block legitimate security software and may even prevent its installation on the system. However, advanced malware removers can hardly be disabled.
Symptoms showing that your computer may be infected with Flooder
- Problems related to PC’s performance. When infected with a Flooder, you can notice slowdowns, system or browser crashes, sudden shutdowns and similar issues. Blue Screen of Death can also interrupt the victim because of the flooder.
- Problems when executing programs. Such viruses can easily disable legitimate applications, such as security software, web browsers and similar apps. Also, they can also delete legitimate files and useful system components.
- The appearance of unwanted pop-ups and alerts. Disrupting notifications can also be caused by flooders. They can additionally lead the victim to such problems as redirects to unfamiliar/dangerous websites seeking to increase their visitors’ traffic and sales. Such sites should be avoided and never trusted.
Methods that are used by Flooders to enter the system:
- Illegal software and software bundles. The most of flooders infect computers via other programs. They can be downloaded with illegal games, unlicensed security programs and even legitimate software.
- Infected websites. Illegal websites have been actively used for spreading malware, including flooders. Typically, viruses are hiding in pornographic sites, gambling websites and similar domains that are filled with promotional content.
- Peer-to-Peer (P2P) software. All programs that use a shared network can lead the user to the risk of malware, including Flooders, trojans, adware, browser hijackers and similar viruses.
- Other malware. Flooders can be installed on the system by Trojan horses, worms and similar threats that are typically used for distributing malware.
The most famous Flooders:
ICQBomber. ICQ.Bomber is a seriously dangerous Flooder, which has mostly been used as a hacking tool. Once inside the system, it starts collecting sensitive information, such as banking data, logins to important websites, passwords and similar data. The loss of such information can lead the victim to identity theft and similar problems. ICQ.Bomber can also install other malware on the system and disable legitimate system components for trying to prevent its removal. The most of its versions have to be installed on the system manually. That is why the developers of this virus have been using various methods for convincing their victims to download it to the system. The most popular method used for the distribution of this Flooder is Illegal software and software bundles.
KillZone. This Flooder is mostly used for launching Denial of Service, ICMP, HTTP and similar attacks against the remote computer. This can prevent the PC user from reaching needed services and launching needed software. KillZone has been actively spread in a bundle with rogue anti-spyware, ransomware and similar malware that tries to hide from the victim as long as possible. Besides, this malware can help for its developers to block legitimate security websites and reputable anti-spyware programs that are usually used for the elimination of such malware. Peer-to-peer (P2P) file sharing networks are considered the most popular way to spread this virus, so you should be very careful when downloading torrent files and similar content to your computer.
CriminalMSN. This threat has mostly been working as a hacking tool used to steal sensitive information from PC users. Similarly to trojan horses, it can cause the loss of logins, passwords, banking data and similar information for thousands of PC users. However, after infiltrating the computer, it can also try to overload a connection, install or download needed software and cause other unwanted activity on the system. CriminalMSN is considered an old virus because it was presented in 2003. Nevertheless, you can never know what the developers of this program can use this virus for in the future.
Removing a flooder from the system:
Flooders are considered very aggressive cyber threats capable of hiding from their victims as long as possible. They can work behind your back and perform tasks that they need to perform for months.
To make sure that all suspicious files that are related to the flooder are eliminated, security experts recommend opting for automatic removal option. In this case, we recommend using one of these reputable anti-spyware programs that have been showing great results while detecting malicious files on the system: FortectIntego, SpyHunter 5Combo Cleaner. Please, make sure that you are using the latest versions of each of these programs to avoid leaving malicious leftovers on your computer.
If you can’t get rid of the Flooder with the help of these tools, you can always contact 2spyware security experts and let them know about that. You can do that via Ask Us page. These computer experts will do a research on your flooder and will provide you with the best removal guide available.
Latest flooders added to the database
Removing Foritatoginia.com ads
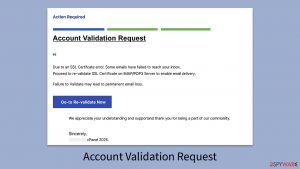
Eliminate Account Validation Request email scam
Remove Dopotics.com ads
Information updated: 2017-05-11