XP Internet Security (scam) - Removal Guide
XP Internet Security Removal Guide
What is XP Internet Security?
XP Internet Security – a fake antivirus program that tries to imitate Windows anti-malware suite
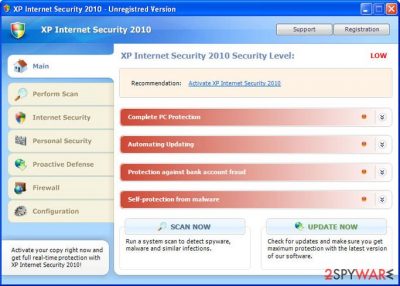
XP Internet Security is bogus security software that, at first glance, might look like a legitimate anti-spyware program. In reality, this program is nothing but a scam that is designed to compromise your Windows machine and trick you into believing that its infection level is dangerously high.
If you have found that this program has shown up on your system seemingly out of nowhere, do not pay attention to anything it displays as it is all fake. Also, do not purchase its “full version” as it will not protect you from real threats – you will only waste your money.
| Name | XP Internet Security |
| Type | Rogue antivirus, scam |
| Related | XP Internet Security 2010 |
| Distribution | Fake online scanners or software vulnerabilities/drive-by downloads |
| Dangers | Financial losses, installation of other malware, personal data disclosure to cybercriminals |
| Elimination | Perform a full system scan with a legitimate antivirus program such as SpyHunter 5Combo Cleaner. If you are unable to launch, access Safe Mode as explained below |
| System fix | Malware modifies Windows OS in order to perform its malicious tasks. In order to fix damage done to the system files, you can either start a Windows reinstall or employ FortectIntego to do it for you automatically |
It is important to note that this malware will change its name based on the operating system it is running on. Thus, an alternative name you could see would be Vista Internet Security if you are running Windows Vista. Dynamic names are yet another social engineering trick to make users believe that the program is used for their OS and that the protection is sufficient.
Once installed and active, it will be automatically configured to scan your computer for malware every time Windows starts. Of course, this fake program only imitates a system scan and, after all, reports false computer threats that cannot be removed with a trial version of the program, so you will be prompted to pay for a full version of the bogus software.
While XP Internet Security is running, you will notice that your computer will begin to run slower. This is because the program is always running in the background while using your computer's resources.
The virus will also display many fake security alerts and impersonate Windows Security Center to make the whole scam look more realistic and to finally convince you into believing that your computer is badly infected. Here is an example of a bogus message:
Threat Detected!
Security Alert! Your computer was found to be infected with privacy-threatening software. Private data may get stolen and system damage may be severe. Recover your PC from the infection right now, perform a security scan.
Furthermore, the rogue program will block anti-virus and anti-spyware software and hijack Internet Explorer. This hijacking consists of a randomly displayed message in a pop-up stating that the page you are visiting has been blocked due to malware activity or other security threats.
If you want to delete this parasite properly, access Safe Mode as explained below and perform a full system scan with SpyHunter 5Combo Cleaner or another reliable antivirus. Also, you should clean your web browsers or reset them altogether. If your system is acting slow or is unstable, use FortectIntego to fix virus damage automatically.
Distribution techniques
As evident, users rarely install this rogue on their Windows systems intentionally. Of course, since it can be found on some shady third-party websites, some people might initially believe that it is legitimate computer security software. In all other cases, users can get infected in one of the following ways:
- downloaded and installed after being tricked by a fake online scanner which claims numerous virus infections;
- automatically downloaded with the help of software vulnerabilities present on the computer after being redirected to a compromised website.
Thus, in order to protect yourself, make sure that your operating system, along with all the installed programs, is patched with the latest security updates. Also, use an anti-malware program with a web shield protection feature – it could warn you about phishing and scam sites.
Do not wait to remove rogue programs from your computer
Rogue security software is especially twisted considering that it pretends to be a program that should defend you from online threats but instead is the parasite itself. Developers of such software are nothing more, but cybercriminals and these creations should be treated for what they are – malware. Furthermore, not only do crooks infect your PC by using malicious distribution techniques, but they also ask for money for it.
XP Internet Security is a total scam, don't buy it and instead remove this infection from your computer upon detection. And by the way, if you have already purchased it, contact your credit card company immediately and dispute the charges if it's not too late.
Getting rid of XP Internet Security. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from XP Internet Security and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting rogue antispyware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.














