ChromeLoader malware (virus) - spam
ChromeLoader malware Removal Guide
What is ChromeLoader malware?
ChromeLoader malware is the virus that spreads using rogue ISO archive files
ChromeLoader malware is designed to install malicious browser extensions onto browsers, and it targets machines running Windows and macOS. The threat has been spread on Twitter with the QR codes promoting pirated software like video games or movies, and TV shows. The infection made headlines recently[1] due to the fact that campaigns appeared to be extremely active these days, and many samples of different variants with particular distribution methods have been discovered.
This browser hijacker modifies the web browser settings to show search results filled with promotional material that push unwanted software, fake giveaways, and surveys and redirects people to adult games, online dating sites, and other commercial platforms. ChromeLoader malware creators get financial gains due to the marketing affiliation from these ad-supported pages and redirect traffic to these commercial sites.
There are many potentially unwanted programs[2] like this browser hijacker. However, the infection caused a major buzz due to the persistent and different methods involved. There are huge volumes of malware spreading around, and the infection route involving aggressive use of PowerShell is not common for browser-based apps. This is a persistent threat to this ChromeLoader hijacker.
| Name | ChromeLoader malware |
|---|---|
| Type | Browser hijacker, unwanted application, potentially unwanted program |
| Issues | The app causes advertisements out of nowhere, triggers issues with the performance and speed of the machine, manipulates browser settings and affects online traffic |
| Distribution | Deceptive posts on social media, advertising campaigns, pirating platforms, torrents |
| Damage | Affects the speed and performance, leads to privacy issues, exposes users to possible malware content |
| Removal | Threats can be removed with anti-malware tools |
| Repair | Infections cause issues with the machine, so run FortectIntego to repair those issues with the machine |
The infection also targets macOS devices and tries to manipulate Chrome and Safari web browsers. The infection is similar to the Windows versions, but it uses DMG files instead of ISO files used for Windows machines. The threat still can ensure persistence with user logs and continuous processes running on the machine.
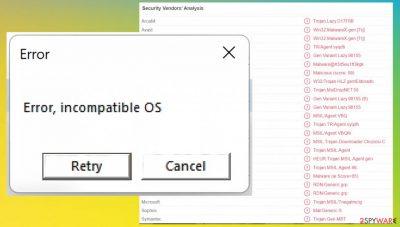
Once the malicious executable with the malware is launched, you might see some error messages or other indications that inform you about issues with the machine. These are the method used by the malware to mask the background processes and avoid detection. Suspicious users might start to check machines when symptoms like this occur.
Damage of the browser hijacker
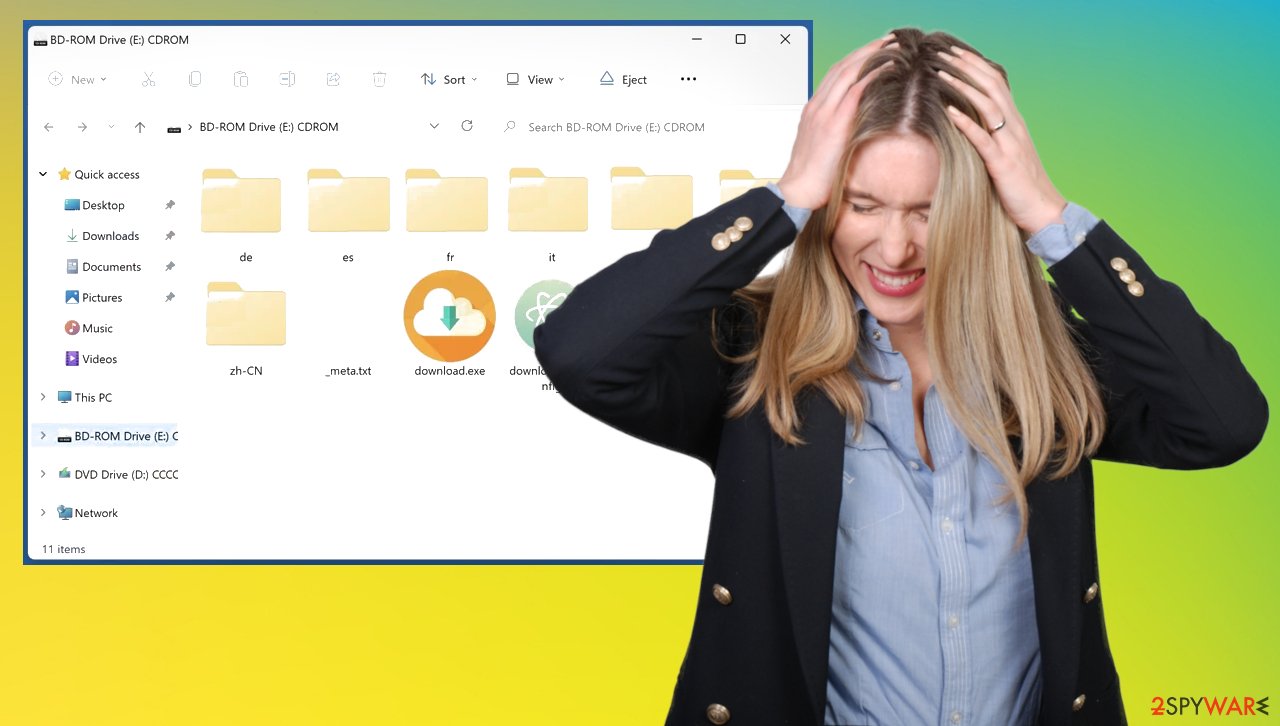
ChromeLoader malware infection can start with malicious advertising material online and downloading the ISO file. Experts[3] reported that these campaigns mainly start with Twitter posts. Malware creators claim to offer pirated or cracked versions of games or software, so the ISO is installed without the users' knowledge.
The malware is launched when the ISO file is double-clicked, so the executable that pretends to be a game or keygen installs the malware. once it is executed, the PowerShell command is executed to fetch browser-based programs from remote resources. Then all the issues begin with the background processes.
Sadly people do not know that common social media campaigns, video sites, game crack portals, and torrent services can deliver these downloaders filled with ChromeLoader browser hijackers or different intruders. The PowerShell creates the task name ChromeTask that is triggering the launch every ten minutes.
This PowerShell script also adds the malicious Google Chrome extensions to the machine. Sometimes these processes cause the crash of the web browser, which indicates the infection. More tech-savvy people can run the anti-malware tools then and let these tools detect the ChromeLoader browser hijacker.
Removing the infection
Even though this is a browser-based program and it manipulates browser settings to control the online traffic, you need t remove the infection properly. ChromeLoader malware can be removed using anti-malware tools that are capable of detecting this infection. Tools like Malwarebytes or SpyHunter 5Combo Cleaner can run the system scan and properly find these infections.
You can remove the virus and other related programs or cyber intruders this way, but some of the files and applications can still run on the machine and cause issues for the user. For that purpose, you should manually go through the particular settings and remove the PUP.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.
![Uninstall from Windows 7/XP Uninstall from Windows 7/XP]()
- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Do not forget that this infection affects various machines including macOS, iOS, and Android or Windows devices. You might want to clear the virus quickly, but these PUPs can be hidden in various places on the machine, so you need to remove the ChromeLoader malware properly.
There are particular instructions for the browser resetting, so the issues and changes made by the browser hijacker can be solved, but these issues with the system and performance when redirecting annoy users can still occur due to the existence of the malware in the background. You should take care of that yourself. You can remove the ChromeLoader malware from macOS devices manually too.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of ChromeLoader malware. Follow these steps
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Google Chrome
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of ChromeLoader malware registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.








