FBI Cybercrime Division virus (Free Instructions) - Aug 2017 update
FBI Cybercrime Division virus Removal Guide
What is FBI Cybercrime Division virus?
FBI Cybercrime Division crypto-malware is after your money
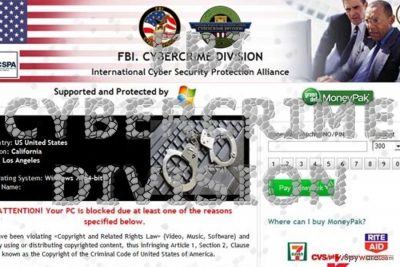
FBI Cybercrime Division virus[1] is perceived as ransomware threat, which similarly to FBI virus is used to deprive PC users of accessing their files and scare with fake alerts. In order to convince its victims that they the genuine FBI has locked their computers due to the violation of laws, this screen locker[2] displays alarming notifications:
FBI. CYBERCRIME DIVISION, International Cyber Protection Alliance.
Attention! Your PC is blocked due at least one of the reasons specified below
Typically, FBI Cybercrime Division virus claims that users were caught engaging in the distribution of pornographic or even child pornography content online similar several crimes. In order to avoid life imprisonment, they have to pay a fine of $300.
However, if you pay close attention to several aspects, you will realize it is purely a scam:
- FBI Cybercrime Division does not exist (Note. FBI Cyber Division or Criminal Investigative Division)
- in case of a violated law, an official subpoena is sent to the suspect via mail, email and other telecommunication means if necessary
- no ransom is required to escape the responsibility
- the suspect's computer' is not locked but rather taken as an evidence
Thus, considering these features, this virus is clearly a scam. Instead of complying with the demands proceed to FBI Cybercrime Division malware removal. In order to get rid of the infection completely, you might use FortectIntego or Malwarebytes. In order to exit the lock screen, Alt+F4 combination might be of assistance. 
Ransomware prevention ways
FBI Cybercrime Division hijack is carried out with the assistance trojan[3], which might disguise in fake software updates, website links, torrent files, keygens, and similar infected downloadable content. Besides, various illegal sites can also be included into its distribution, so stay away from gaming or gambling websites.
As soon as this trojan gets inside the device, it blocks the entire system down and claims that user has violated a law of United States of America. According to it, he was identified by IP and ISP and now must pay a fine of $300 using Greendot MoneyPak voucher:
FBI CYBERCRIME DIVISION
International Cyber Security Protection Alliance
ATTENTION!
Your PC is blocked due at least one of the reasons specified below.
You have been violating Copyright and Related Rights Law. (Video, Music, Software) and illegally using or distributing copyrighted content, thus infringing Article 1, Section 2, Clause 8, also known as the Copyright of the Criminal Code of United States of America.
Article 1, Section 2, Clause 8 of the Criminal Code provides for a fine of 200 to 500 minimal wages or a deprivation of liberty for 2 to 8 years.
You have been viewing or distributing prohibited Pornographic content (Child Porn/Zoophilia and etc). Thus violating Article 2, Section 1, Clause 2 of the Criminal Code of United States of America.
(…)
Fines may only be paid within 72 hours after the infringement. As soon as 72 hours elapse, the possibility to pay the fine expires, and a criminal case is initiated against you automatically within the next 72 hours! To unblock the computer you must pay the fine through MoneyPak of $300. When you pay the fine, your PC will get unlocked in 1 to 72 hours after the money is put into the State’s account.
Since your PC is unlocked, you will be given 7 days to correct all violations.In case all violations are not corrected after 7 working days, your PC will be blocked again, and a criminal case will be initiated against you automatically under one or more articles specified above.
Be sure that all this notification is a huge scam, which seeks to get you out of your money. Please, ignore it and remove FBI Cybercrime Division virus from the system. In order to lower the probability of the misfortunate encounter, run regular scans with your security tool. In addition, pay attention to the received spam emails. Avoid opening any attachments without verifying the sender.
Delete FBI Cybercrime Division screen locker
When trying to remove FBI Cybercrime Division virus, you have to unlock your computer first. Bear mind that the malware targets not only English speakers, such as British[4], Americans or New Zelandians, but it may have its counterparts in other languages as well. In order to get an ability to scan your compromised computer with a decent anti-malware, follow these options:
* Flash drive method:
- Download FortectIntego or Malwarebytes.
- Update the program and put into the USB drive or simple CD.
- In the meanwhile, reboot your infected machine to Safe Mode with Command prompt and stick USB drive in it.
- Reboot computer infected with FBI Cybercrime Division virus once more and run a full system scan.
* Users infected with FBI Cybercrime Division virus are allowed to access other accounts on their Windows systems. If one of such accounts has administrator rights, you should be capable to launch anti-malware program.
* Try to disable the Flash to make your ransomware stop function as intended. In order to disable the Flash, go to Macromedia support and select “Disable”: http://www.macromedia.com/support/documentation/en/flashplayer/help/help09.html. After doing that, run a full system scan with anti-malware program.
* Manual FBI Cybercrime Division virus removal:
- Reboot you infected PC to 'Safe mode with command prompt' to disable FBI Cybercrime Division virus (this should be working with all versions of this threat)
- Run Regedit
- Search for WinLogon Entries and write down all the files that are not explorer.exe or blank. Replace them with explorer.exe.
- Search the registry for these files you have written down and delete the registry keys referencing the files.
- Reboot and run a full system scan with updated FortectIntego to remove remaining FBI Cybercrime Division virus files. We also recommend using SpyHunter 5Combo Cleaneror Malwarebytes.
Getting rid of FBI Cybercrime Division virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove FBI Cybercrime Division using System Restore
In case Safe Mode is not convenient to you, you may attempt to perform System Restore to gain access and run the system scan.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of FBI Cybercrime Division. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove FBI Cybercrime Division from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by FBI Cybercrime Division, you can use several methods to restore them:
What is Data Recovery Pro?
In case you happen to encounter ransomware which encodes files, then this tool might be of assistance in restoring files. On the other hand, it is recommended to back up your files and store them in the Cloud and physical places.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by FBI Cybercrime Division ransomware;
- Restore them.
The usefulness of ShadowExplorer
This utility recovers damaged or encrypted data by using volume shadow copies. It might be your last resort to restore files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from FBI Cybercrime Division and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Carlos Osorio. FBI Warns the Public About Ransomware Internet Scam. San Juan. FBI news and notices.
- ^ Eric Geier. How to rescue your PC from ransomware. PCWorld. News, tips, and reviews from teh experts on PCs, Windows and more .
- ^ Ransomware, Trojans and Fraud, Oh My! Tracking Recent Cybercrime Trends and Patterns. SecurityIntelligence. Analysis and Insight on Information Security.
- ^ Eliminate malware. Novirus. News, reviews, and malware removal guides.





















