Hnumkhotep@india.com ransomware / virus (Tutorial) - Removal Guide
Hnumkhotep@india.com virus Removal Guide
What is Hnumkhotep@india.com ransomware virus?
Hnumkhotep@india.com ransomware is ready to target your files
Hnumkhotep@india.com virus is the name of a newly emerged crypto-malware. IT specialists report it to be a new version of Globe ransomware. Since the first appearance in 2016, few might have suspected that it would develop into an enormous ransomware. Its creators have been continuously developing the virus as several modified versions have been launched. Some of them are .LoveWindows file extension virus, Kyra ransomware, banij2@india.com. Interestingly, that some viruses are similar to other ransomware in the market since they also bear @india.com email address. Along with other well-known file-encrypting viruses, these @india.com themed virtual threats also comprise a big share of all crypto-malware infections in the market [1]. Originally, it drew inspiration from the Purge movies. Hackers try to outrun virus researchers [2] and keep releasing several different viruses into the wild. This activity of this group of ransomware did not remain unnoticed and IT experts, particularly Emsisoft, have created free decryption software for this virus. Though the tool originally was devised for the third installment, users might try using it and for other versions. Before this procedure, you should permanently remove hnumkhotep@india.com from the computer.
While some threats remain “single-use,” others have received several sequels. Regarding Globe ransomware, its developers seem to launch new viruses on a whim as they name it them quite randomly. Usually, the title to a virus is given according to the file extension it appends. Likewise, you may notice quite ridiculous and hilarious titles among ransomware. However, usually, victims of Globe ransomware series are the last who find such viruses to be funny. Like other samples, hnumkhotep@india.com malware also employs AES-128 or AES-256 encryption algorithms. They are distinct for running several cycles of ciphers. As a result, a unique key is generated. Consequently, there is almost impossible to guess a matching decryption key. Since the basics of this technique are quite simple but it presents a sufficient encryption key, it has been popular among various ransomware creators [3].
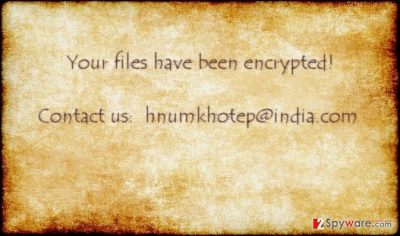
Furthermore, ransomware threats demand several hundreds of dollars. The most prevalent demanded amount varies from one to three bitcoins. The amount of rate fluctuates everyday, however, recently it overcame the border of 1000 dollars [4]. If you have been struck with hnumkhotep@india.com ransomware, and thinking about transferring the money in the hope of returning the money, we would like to discourage from doing so. Only few ransomware families are known to return the data after receiving the money. Moreover, we do not recommend you to risk wasting your money. Instead, concentrate on hnumkhotep@india.com removal.
What should you know about its distribution?
This family of ransomware is usually dispersed via spam emails. Nonetheless, despite constant warnings, users still fall for the bait of crooks. They target credulous users with fake tax email reports, customs declaration emails or the messages from well-known shopping companies. Especially if you are a regular customer of one of the companies or you frequently have business with the formerly mentioned institutions, there is a risk you might open a corrupted attachment. As a result, hnumkhotep@india.com hijack gets executed and then it becomes a difficult task to stop the activation of the virus. If you receive a spam email with similar content, do not rush to make reckless actions. Hackers usually make up fake stories and set a time limit not to leave enough time for users to realize the true origin of such email message. Look for grammar and typing mistakes. Frequently, credentials are also altered which might give out suspicion. In addition, you should beware of the exploit kits and trojans which dwell in corrupted gaming or file sharing websites [5]. Therefore, it is necessary to upgrade and update security applications in order to lower the risk of encountering such threats.
Eliminating Hnumkhotep
Even if your computer has been struck with hnumkhotep@india.com virus, there is no need to panic. You can terminate it using an anti-spyware application, such as FortectIntego or Malwarebytes. After hnumkhotep@india.com removal, you can proceed with the file recovery procedure. In the bonus recovery instructions, we will also place the link to a devised decryption file for one of Globe versions. Perhaps it might work in your case. If you encounter any system errors generated by the virus which bother you to remove hnumkhotep@india.com, use the instructions below.
Getting rid of Hnumkhotep@india.com virus. Follow these steps
Manual removal using Safe Mode
In case, your operating system is paralyzed, you can proceed to these steps to regain access and eliminate hnumkhotep virus eventually.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Hnumkhotep@india.com using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Hnumkhotep@india.com. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Hnumkhotep@india.com from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Hnumkhotep@india.com, you can use several methods to restore them:
Data Recovery Option
In case you had this program previously installed, you might try using it to recover the files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Hnumkhotep@india.com ransomware;
- Restore them.
ShadowExplorer method
The key benefit of this application is that it recreates the files using shadow volume copies. They are automatically generated by the operating system.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryptor for Globe3 version
While Hnumkhotpe virus is different from the mentioned edition, you might succeed in retrieving the files using this free decryption program.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Hnumkhotep@india.com and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Marshall Honorof . Globe Ransomware Channels Purge Movies, Ruins Files. Tom's Guide. Tech Product Reviews, Top Picks and How to.
- ^ Danny Palmer . Hit by Globe3 ransomware? This free tool could help you decrypt your files. ZDNet. Technology News, Analysis, Comments, and Product Reviews for IT professionals.
- ^ Lucian Constantin . Professionally designed ransomware Spora might be the next big thing . ComputerWorld. IT news, careers, business technology, reviews.
- ^ DarkSyde . The rise (and probable fall) of bitcoin. Daily KOS Blog.
- ^ Michael Mimoso. Two New Edge Exploits Integrated Into Sundown Exploit Kit. ThreadPost. The first stop for security news.





















