Ivonch.click ads (Free Guide)
Ivonch.click ads Removal Guide
What is Ivonch.click ads?
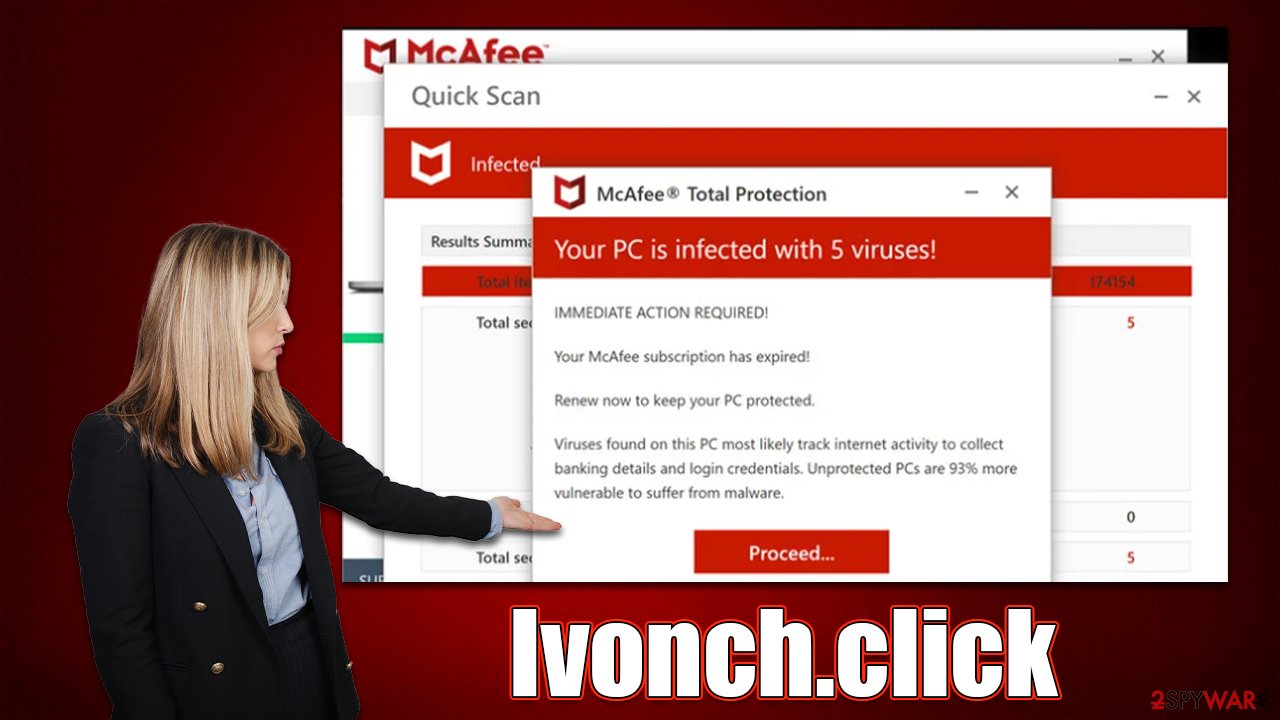
Ivonch.click shows fake security checks to frighten users and make them purchase software

It is becoming increasingly common for people to encounter malicious web pages like Ivonch.click that attempts to imitate known security vendors in order to make people click on affiliated links and purchase the software. This problem occurs whenever someone is browsing the web on Chrome, Safari, Edge, Firefox, or another web browser. More often than not, the redirect happens when a malicious link somewhere else is clicked – torrents, illegal video streaming sites, and similar are likely to cause these types of issues.
In more serious cases, users who have adware[1] can be constantly redirected to phishing sites. If there is an increased number of advertisements as well, it becomes even more difficult to remove unwanted software from their system. To avoid being redirected to these harmful sites, it's important to take measures to remove the virus immediately. To stop the Ivonch.click ads, you would have to access browser settings and block the site's URL – we explain how to do that below.
| Name | Ivonch.click |
| Type | Scam, phishing, redirect, adware |
| Operation | Claims that viruses have been found on the system and that the security software has expired. Asks to purchase a license and enable push notifications |
| Distribution | Compromised websites, pop-up ads, potentially unwanted applications |
| Risks | Installation of PUPs or malware, sensitive information disclosure, financial losses |
| Removal | Make sure you scan your system with SpyHunter 5Combo Cleaner – especially if you downloaded and installed software from a scam site |
| Other tips | Third parties can use cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover files with FortectIntego |
How users get scammed
Upon entering the Ivonch.click site, users are immediately shown a fake virus scan allegedly performed by a reputable security vendor known as McAfee. While this may surprise visitors, the usage of the anti-malware maker's name and its logos may make some believe that the scan is actually legitimate. During this time, people are shown several pop-up messages which look like triggers for various detections allegedly found on the computer.
Just a short while later, after a few seconds, users are shown a pop-up that comes up with the following verdict:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your McAfee Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
This result is pre-generated, which means it is being shown to every person that visits the Ivonch.click scam site. Likewise, some users may also be shown a blue screen that closely reminds the Blue Screen of Death,[2] commonly used by Windows to display stop errors. This is deliberately done in order to frighten users – it's just another social engineering[3] technique, as familiar elements tend to resonate with users more, making it seem that what they see is legitimate.
In reality, McAfee has nothing to do with this elaborate scheme, and every component on the page is fabricated. In order to perform proper checks, you need reputable anti-malware installed on your device – no website can tell whether you have viruses installed on your system.
Remove adware from the system
An adware scan is the first step in the recovery process after coming across the Ivonch.click scam website. By running a comprehensive system check with SpyHunter 5Combo Cleaner or Malwarebytes security software, which would quickly and effectively remove all unwanted components at once, you may ensure that your system is free of adware.
While you can attempt to remove undesirable apps manually, automated removal is quick and easy. In addition, deleting helpful programs could have the opposite effect. However, you should immediately clear your browsers of cookies and other trackers once you are certain that your device is free of malware and adware. You have two options for completing this task: either hire FortectIntego or do it yourself using the guidelines below:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Also, if you were redirected to another malicious website and were tricked into providing your personal information (such as any passwords, account details, or other details), you should be aware that your contact data could be passed on to cybercriminals. This means that you may receive more phishing emails or phone calls in the future, so be wary.
Remove intrusive push notifications
Websites that tend to provide false information about users' computers frequently make an effort to monetize in as many different ways as possible. As soon as visitors enter the website, they are asked to accept push notifications in addition to misleadingly trying to sell them software.
While the majority of users would ignore the request, some would unintentionally click the “Allow” button, which would cause annoying pop-ups to appear on users' desktops and show unsuitable, deceptive content and possibly even contain harmful links. It is not advised to respond to these notifications because doing so could endanger your security and safety. Instead, adhere to the advice below to cease the intrusive ads:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the URL's drop-down menu.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
- Click on More actions and select Block.
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Adware. Wikipedia. The free encyclopedia.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. How-to Geek. Site that explains technology.
- ^ Social Engineering. Imperva. Application and data security.








