Jest ransomware (Virus Removal Instructions) - Bonus: Decryption Steps
Jest virus Removal Guide
What is Jest ransomware?
Jest ransomware takes advantage of unprotected RDP servers to attack host PCs and demand Bitcoins in exchange for a decryption key
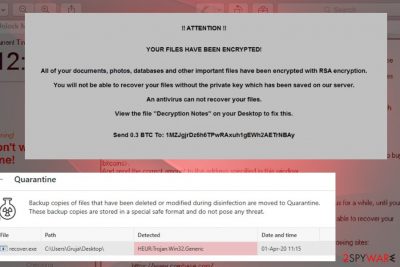
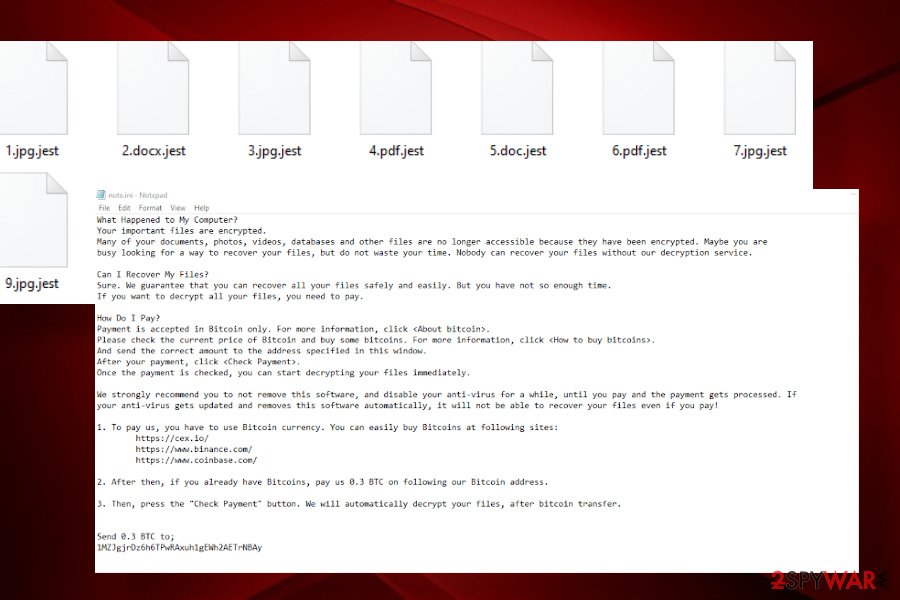
Jest ransomware is yet another deadly dangerous cyber infection, which once installed attacks files on a host machine and locks them with a .jest file extension. Although detected on April 1st, 2020, the news about multiple victims all around the world appears not to be an April Fool's joke. Stemming from FunFact ransomware, the Jest virus actively spreads as a .zip and .exe spam attachment, malicious downloads of pirated software, and unprotected RDP servers. Upon infiltration, it compromises the system's boot files, registry entries, and activates RSA cipher to encrypt files, such as pictures, videos, documents, databases, stored on a host machine. Subsequently, each locked file gets an appendix .jest and cannot be renamed, opened, moved or otherwise used. The victim is informed about an attack via a ransom note called “Note.ini,” which instructs a victim to transfer 0.3 BTC (currently over $2,000).
The criminals behind Jest ransomware seek to earn 0.3 BTC, which is not a huge ransom if compared to crypto-malware like RagnarLocker. Anyway, paying more than $2,000 for criminals is a huge loss, especially for files and data that belongs to you. To “facilitate” the process of payment, criminals provide links to the Bitcoin purchase websites and explanation on how and where the transfer has to be done.
| Name | Jest |
| Family | FunFact ransomware |
| Encryption | Jest ransomware uses RSA encryption – an asymmetric cryptographic algorithm, which generates a Private Key to lock personal files on a host PC with a .jest file extension |
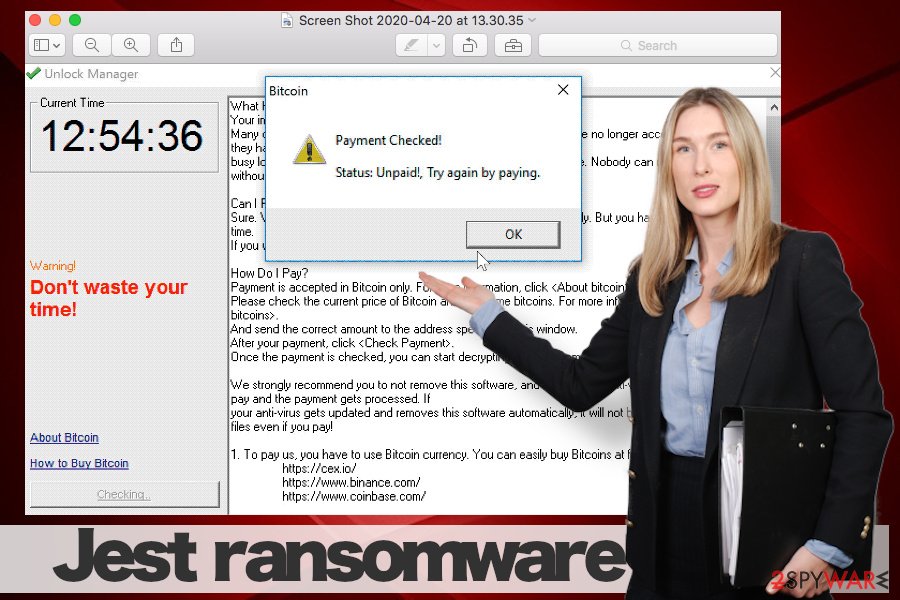
| Ransom note | The ransomware changes PC's background image, creates a note.ini file on the desktop and scheduled task to display a pop-up called “Unlock manager” |
| Payment | Criminals behind the ransomware are not too demanding: the ransom they require is equal to 0.3 BTC (more than $2.000) |
| Distribution |
Crooks leverage various techniques to distribute malware like Jest. Most of the infections start on Outlook or other e-mail accounts when people open malicious attachments. Furthermore, files may get locked after getting a dangerous infection via a hacked RDP, software cracks, infected hyperlinks, fake software updates, and similar |
| Elimination |
As soon as you notice ransomware virus on the system, take immediate action to remove it once and for all. One and only way to root out the malicious ransomware is to run a full system scan with a professional anti-malware tool while booted in Safe Mode with Networking |
| Fix virus damage | Ransomware initiates multiple compromisation activities against a host machine. Consequently, it may encounter errors, BSOD, load problems, and so on. To fix such and similar damage, use FortectIntegoutility |
Once Jest ransomware payload is launched, the virus drops an executable file, which starts an attack in the background, and later Windows Registry to activate malicious registry keys. Consequently, the virus ensures that it will be booted along with the PC's activation. The malicious executable file, at the same time, launches the encryption software and targets personal files stored on the machine. Finally, when the files are encrypted by .jest file extension and other background processes are done, the ransomware replaces desktop's background image “YOUR FILES HAVE BEEN ENCRYPTED” and generates a scheduled popup window Unlock Manager. The later, just like a txt form ransom note, provides instructions on how to pay the redeem for a personal decryption key. Besides, it displays a countdown clock, which gives the victim 24 hours to contact with the criminals.
What Happened to My Computer?
Your important files are encrypted.
Many of your documents, photos, videos, databases and other files are no longer accessible because they have been encrypted. Maybe you are
busy looking for a way to recover your files, but do not waste your time. Nobody can recover your files without our decryption service.Can I Recover My Files?
Sure. We guarantee that you can recover all your files safely and easily. But you have not so enough time.
If you want to decrypt all your files, you need to pay.How Do I Pay?
Payment is accepted in Bitcoin only. For more information, click .
Please check the current price of Bitcoin and buy some bitcoins. For more information, click .
And send the correct amount to the address specified in this window.
After your payment, click .
Once the payment is checked, you can start decrypting your files immediately.We strongly recommend you to not remove this software, and disable your anti-virus for a while, until you pay and the payment gets processed. If
your anti-virus gets updated and removes this software automatically, it will not be able to recover your files even if you pay!1. To pay us, you have to use Bitcoin currency. You can easily buy Bitcoins at following sites:
hxxps://cex.io/
hxxps://www.binance.com/
hxxps://www.coinbase.com/
2. After then, if you already have Bitcoins, pay us 0.3 BTC on following our Bitcoin address.3. Then, press the “Check Payment” button. We will automatically decrypt your files, after bitcoin transfer.
Send 0.3 BTC to;
If you are under attack at the moment, you have two options, i.e. to purchase Bitcoins and send them to criminals or remove Jest ransomware and try to recover your files using alternative solutions. Windows Volume Shadow Copies[1] won't help in this case, as the ransomware is programmed to remove all the copies. However, Data Recovery Pro and Previous Windows copies may do the trick. Even more, if you have the backups of the most valuable files, do not even consider paying the ransom at all.
One may think that ransomware removal is a task for tech-savvy ones. In fact, the success of the Jest removal depends much on the AV software that you are using. According to VirusTotal[2], 56 out of 71 AV engines are capable of detecting and removing this threat. Therefore, if you have a professional Antivirus program, launch its scanner and wait for it to report a successful removal of Win32: Malware-gen, Gen:NN.ZevbaF.34106.@pKfaOo2H3oO, Win32/Filecoder.OBM, Trojan.Win32.DelShad.cxv, Gen:Heur.Ransom.Imps.1, or similar malware.
Typical ways of ransomware propagation
IT experts from NoVirus.uk and other partners do not exaggerate admonishing how dangerous it is to open email messages from unrecognized senders. Email spam campaigns[3] are extremely common, so if your email address has been leaked many times, you may receive tens of dangerous messages imitating DHL, FedEx, Federal Income Tax Treatment, or other authorities. More elaborate scam campaigns can disguise under chief executive personas' from Red Cross, Facebook, and similar.
Usually, these messages are well-prepared. However, some grammar, typo mistakes or formatting are left suspicious. Therefore, do not open the attachments if you were not waiting for a specific document from a known person. If you have any doubts, reply to the sender and double-check if the attachment is safe to open. The bot will never answer your question.
Aside from spam, ransomware can be deployed via software cracks on peer-to-peer networks, hacked RDP servers, malicious ad campaigns, software updates, and similar media. Ransomware can hardly be injected into well-protected websites or reputable downloads, though there may be exclusions. Therefore, you must not visit dangerous websites, avoid downloading software recklessly and stay away from intriguing ads. Besides, protect your machine with a reliable AV engine that has an in-built real-time protection feature.
Comprehensive Jest ransomware removal instructions and data recovery tips
Do not wait long considering pay the ransom or not. The longer you hesitate, the more files you may lose. Once you detect your files encrypted, launch an antivirus scanner and remove Jest ransomware immediately.
In most of the cases, ransomware viruses block AV engines. That's a common practice, so don't fall for panic. Jest removal will definitely be successful if you boot Windows into Safe Mode with Networking. After that, launch SpyHunter 5Combo Cleaner or Malwarebytes and let the program do its job. After that, you should fix affected computer areas with the help of a professional repair tool, such as FortectIntego.
Finally, the corrupted files should still have the .jest extension. If you have backups, then remove the useless files and use the copies. If there are no backups, we will give you a couple of useful tips on how to recover files encrypted by .jest. If neither of them helps, you may need to contact a professional IT-expert to crack the encryption algorithm down.
Getting rid of Jest virus. Follow these steps
Manual removal using Safe Mode
Ransomware virus runs multiple malicious processes and can severely damage the Windows system. To protect your PC from a full crash, delete the package of the virus by running the system into Safe Mode and launching the AV scanner:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Jest using System Restore
All malicious aftereffects, except encrypted files, can be returned to the state before ransomware attack by restoring the system to the previous version:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Jest. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Jest from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Jest, you can use several methods to restore them:
Data Recovery Pro software can recover compromised files
Data Recovery Pro is a utility widely used by IT specialists who attempt to restore lost files after PC's crash and ransomware attacks. Since the program is easy to use, you can give it a try.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Jest ransomware;
- Restore them.
take advantage of Windows Previous Version feature to recover files locked by Jest ransomware
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
There is no Jest ransomware decryption software yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Jest and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Volume Shadow Copy Service. Microsoft. American multinational technology company.
- ^ Virus Total analysis. VirusTotal. Online service that analyzes files and URLs.
- ^ Jeff Brainard. State of Email Security in 2020: More Spam, Malware, Phishing & Ransomware Ahead. Fortinet. Network security solutions f.





















