Light Tab browser hijacker (Free Guide)
Light Tab browser hijacker Removal Guide
What is Light Tab browser hijacker?
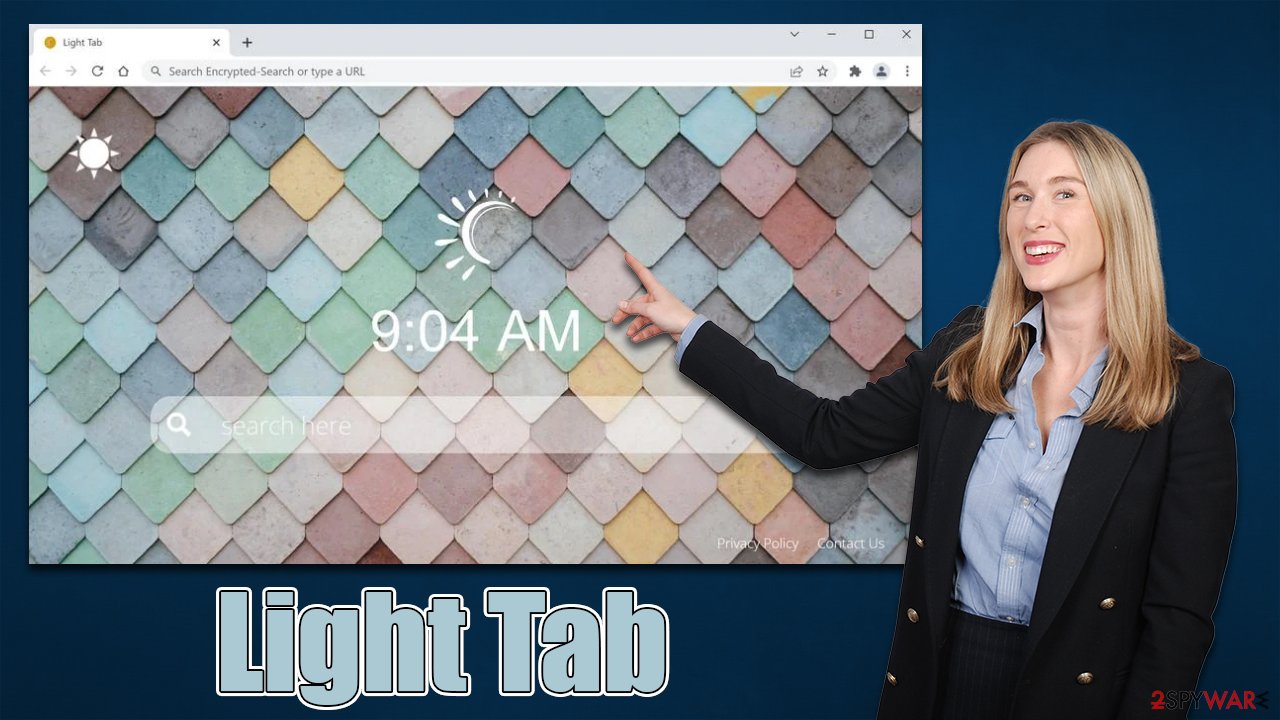
Light Tab is a browser hijacker that negatively impacts your browsing experience

Light Tab is a potentially unwanted application that spreads as an extension for Google Chrome, MS Edge, or another compatible web browser. While some people might install it themselves believing it can be useful, others find the app on their browsers unexpectedly – this happens due to deceptive distribution techniques used by the PUP authors, including software bundling[1] and misleading ads/phishing[2] messages.
Once installed, the hijacker changes the homepage and new tab address to search.lighttab.me, which allows it to take over users' browsing sessions entirely. Not only would might this switch the default search provider to an alternative one but also would insert various ads and sponsored links at the top of the search results.
Besides, just like any other app of this kind, Light Tab is programmed to collect various user data, which may result in privacy risks. If you have found this application running on your system, we recommend removing it as soon as possible using our comprehensive instructions below.
| Name | Light Tab |
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Bundled software, third-party websites, misleading ads |
| Symptoms | New extension installed on the browser; homepage and new tab set to hiddensearcher.com; redirects searches to another provider and inserts ads |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | You should access your browser's settings to remove the unwanted browser extension. Checking the system with SpyHunter 5Combo Cleaner security software can also ensure that there is no adware or malware running in the background |
| Other tips | We recommend scanning the system with PC repair and maintenance utility FortectIntego to remove leftover files and ensure that trackers are eliminated from the browser |
Browser hijackers: why you shouldn't use them
The most likely way of getting infected with potentially unwanted software is through software bundling. This technique is used by almost all third-party websites that spread freeware,[3] or shareware – it's their primary monetization method along with embedded ads. Therefore, whenever you go to such a site, keep in mind that you might end up installing additional programs if you don't pay close attention when installing new apps.
Here are a few tips that could help you to avoid PUPs and even malware in some cases:
- If possible, always download software from reputable sources and avoid torrents and similar sites;
- During the installation of freeware, never rush through the steps – always pick Advanced or Custome settings instead of Recommend ones if such option is provided;
- Watch out for pre-ticked checkboxes, misplaced “Accept offer” buttons, and similar tricks;
- Always read the fine print and information that's disclosed after choosing the “Advanced” installation option;
- Install reputable anti-malware software with the PUP detection feature.
Light Tab removal explained
Extensions have become one of the most popular types of browser hijackers – they are easy to make and rebrand to avoid a bad reputation or even detection by some security applications. The good thing about this is that the app's operation scope is usually smaller compared to programs installed on the system level.
Nonetheless, browser hijacker developers come up with new ideas on how to prevent users from uninstalling these apps, for example, they employ the “Managed by your organization” feature, which prevents users from removing apps in a regular way. Luckily, Light Tab does not employ this tactic, so its removal should cause any difficulties.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Additional measures to wrap things up
As we already explained, many browser hijackers and other potentially unwanted applications spread using bundling or other deceptive techniques, so if you have found the Light Tab app on your system without intentionally installing it, there is a high chance that additional PUPs are present as well.
Likewise, if you frequent high-risk websites, such as torrents or illegal video streaming sites, download software cracks, and engage in similar high-risk behavior, malware infections could be very likely. Please refrain from doing this in the future, as you could infect your device with something much more sinister – ransomware,[3] for example. As a result, you may lose all your personal files unless you pay a ransom to cybercriminals.
Thus, we recommend you scan your system with SpyHunter 5Combo Cleaner or Malwarebytes security software to ensure that your device is not infected with more dangerous, invisible malware. Besides, anti-malware is your first line of defense when it comes to incoming malware attacks.
Finally, you should clean your browsers from cookies and other trackers, as third parties may continue tracking you otherwise. The easiest way to get rid of leftover files is by using the FortectIntego repair and maintenance utility, although the manual method can be used as well – just follow these steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.
![Clear Edge browsing data Clear Edge browsing data]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting browser hijacker
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ What Is Freeware?. Lifewire. Tech News, Reviews, Help & How-Tos.










