Racing Cars Tab browser hijacker (Chrome, Firefox, IE, Edge) - Free Guide
Racing Cars Tab browser hijacker Removal Guide
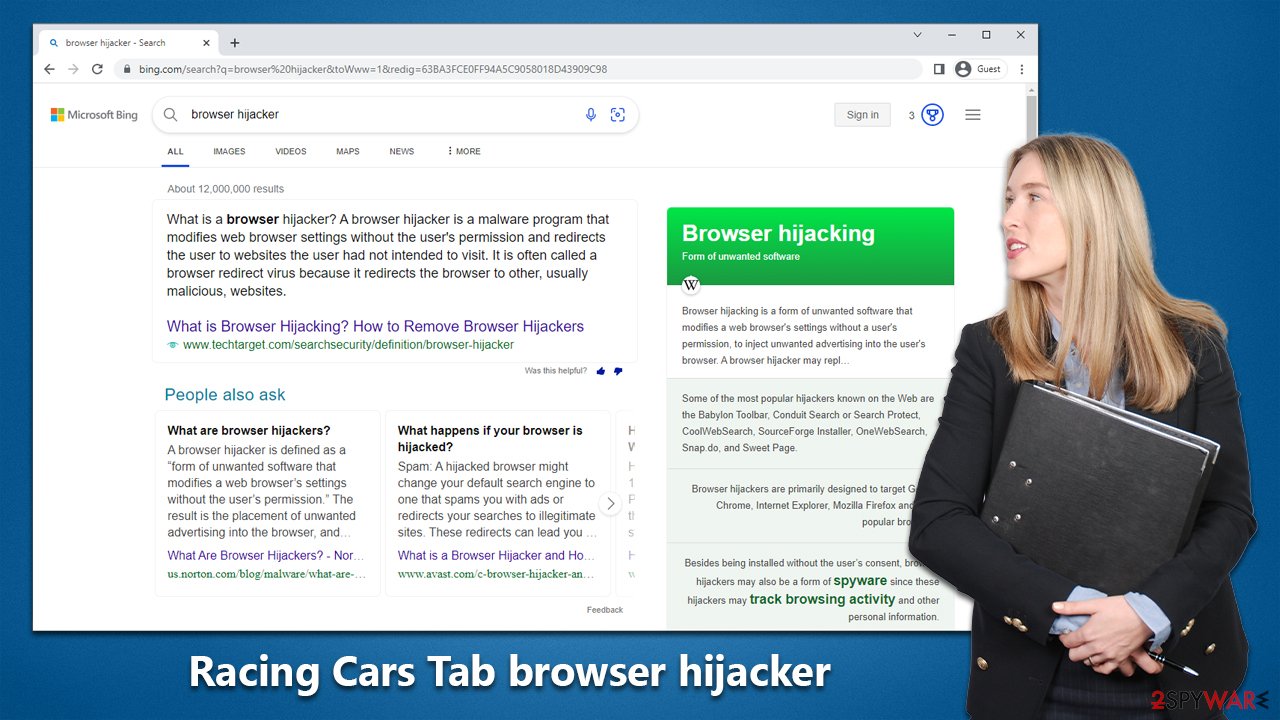
What is Racing Cars Tab browser hijacker?
Racing Cars Tab is a browser-hijacking application that might bring ads you never wanted

Racing Cars Tab is a browser hijacker that changes the default search engine and homepage of your web browser without your permission. It also displays unwanted advertisements and pop-ups on the affected browser. The purpose of the app is to generate revenue through online advertising. This type of software is often bundled with other free software downloads, so users often end up installing it unintentionally, only to notice it taking over Google Chrome or other used browsers later.
If you have noticed Racing Cars Tab is installed on your browser without permission, it is time to remove it at once. Otherwise, you might continue to be tracked by unknown third parties and suffer from persistent ads. We explain how to make sure that the hijacker is gone in the instructions below.
| Name | Racing Cars Tab |
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Software bundles, ads online, deceptive sites |
| Symptoms | The extension takes over your homepage and new tab address, placing promotional links as the top search results. It also displays intrusive ads on various websites you visit |
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | To remove the unwanted browser extension, you should access your browser's settings. Checking the system with SpyHunter 5Combo Cleaner security software can also ensure that there is no adware or malware running in the background |
| Other tips | It is suggested to perform a system scan with a PC repair and maintenance utility FortectIntego to delete any residual files and guarantee that the browser is free from any trackers |
How Racing Cars Tab hijacks your browser and what can it do
Browser hijacking can be a real nuisance for internet users. This is because it alters the default settings of your browser, such as the homepage and search engine, without your consent. The purpose behind this is typically to promote websites, usually illegitimate search engines, to generate revenue through online advertising.
One such example is Racing Cars Tab. When installed on a device, it changes the browser settings to racingcarstab.com and redirects any new tabs or web searches to this site. Unfortunately, browser hijackers like Racing Cars Tab often use persistence-ensuring techniques to make it difficult to remove and undo any user-made changes.
It's important to note that fake search engines like racingcarstab.com often redirect to legitimate ones, such as Bing, to provide search results. However, the redirects can change based on factors like user location. Additionally, browser hijackers may also spy on your online activity and collect data like URLs visited, personal information, and financial details. This information can then be sold or used for profit by third parties.
While having software like Racing Cars Tab on your device can hardly lead to serious privacy concerns, financial losses, or identity theft, programs or malware installed alongside it might do so. It is essential to be cautious during software installations and to take measures to remove any browser hijackers if they are present on your device.
Avoidance tips
Users may be taken aback when they discover that their browser settings, including the homepage and new tab, have been changed without their knowledge. This usually occurs when they install freeware from untrusted sources or agree to additional components without realizing it.
Many times, users overlook important installation steps in their haste to finish the process quickly. They tend to blindly click on “Next” without reading the terms, or they may choose “Recommended” or “Quick” settings, which automatically install the applications. To avoid such situations, it is always better to choose the “Advanced” option, as it gives users more control over what is being installed on their system.
Some users may fall for fake advertisements or updates that trick them into installing unwanted software. These advertisements often claim that something is missing from the computer and must be installed for various reasons, such as the supposed detection of viruses. To stay safe, users should always ignore such requests and only refer to the official websites of the software whenever they encounter a suspicious claim.
Remove Racing Cars Tab
Browser extensions often referred to as add-ons, are a popular form of potentially unwanted applications. They are easy to create, maintain and can effectively target users with advertisements. To avoid the adverse effects of these extensions, it is essential to access the browser settings and remove any browser hijacker present.
Before taking action, it is recommended to conduct a thorough scan of your system using reliable anti-malware software like SpyHunter 5Combo Cleaner, Malwarebytes, or any other trustworthy tool. This will ensure that no other potentially harmful programs are present and running in the background. It is worth mentioning that a strong security solution can also protect against serious threats like ransomware.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
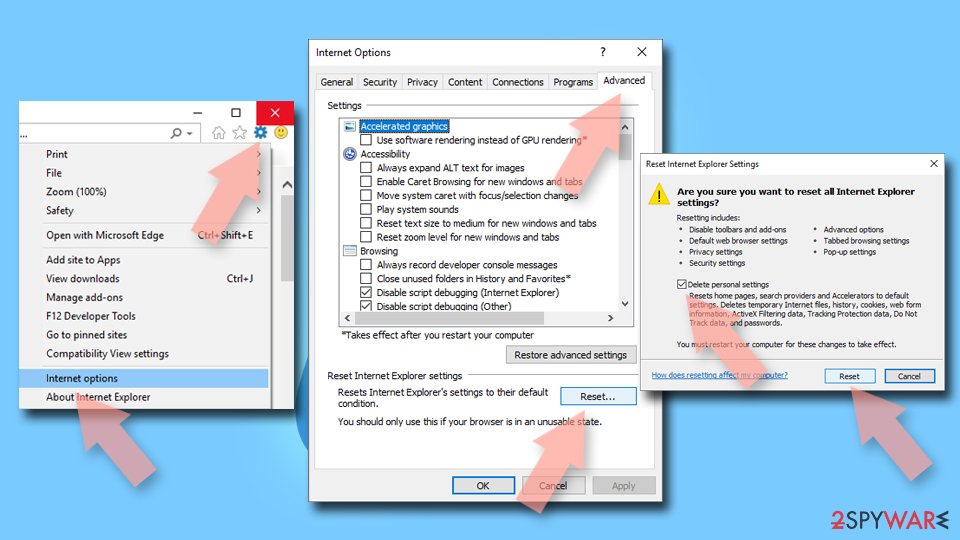
Internet Explorer
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.
![Remove add-ons from Internet Explorer Remove add-ons from Internet Explorer]()
Cleaning browsers from trackers
It is well established that browser hijackers are notorious for collecting user data and sharing it with third parties for financial gain. To accomplish this, the developers of these programs install multiple trackers on the user's device, which persist even after the extension is uninstalled. Therefore, it is important to clear all cookies and site data from your system to eliminate these trackers.
One option is to use an automated tool like FortectIntego to achieve this, or you can follow the manual process of clearing cookies and site data, following a set of steps.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Internet Explorer
- Click on the Gear icon > Internet options and select the Advanced tab.
- Select Reset.
- In the new window, check Delete personal settings and select Reset.
![Reset Internet Explorer Reset Internet Explorer]()
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.