Ransoc ransomware / virus (Free Guide)
Ransoc virus Removal Guide
What is Ransoc ransomware virus?
Ransoc ransomware threatens to sue you
Ransoc virus is peculiar for file-encrypting and browser-locking capabilities. Psychological pressure and false accusations always work as the best people manipulation tools. In this regard, this malware presents an elaborate message accusing victims of child abuse, the violation of intellectual property rights, and other illegal activities. In order to add more flavor, the amount of ransom and the duration of each trial sentence is added. On the left side, you see the fake webcam which supposedly has recorded all the suspicious activity. Though such notice is surely horrifying for some users, it is useful to keep in mind some tips which help you identify the fraud from the real notification. While you are reading this article, do not waste time and start Ransoc removal. FortectIntego quickens up the procedure.
There have been similar ransomware viruses before. The majority of them happens to be tech support scams which either fake windows notifications or alarm users with their computers being infected with serious threats. However, in this case, the cyber criminals did quite a marvelous job. They forged the penalty notice and enhanced it with elaborate details to make the notice more convincing. What is more, it even includes the articles from the law regulating sentences for specific rights infringement or child abuse. It would be not surprising that a high number of victims would fall into this trap as cyber criminals distribute Ransoc malware in pornographic domains. As a result, users enjoying themselves by looking adult content might really feel a sense of guilt for such activity. Therefore, it fosters the assumptions that the message is real.
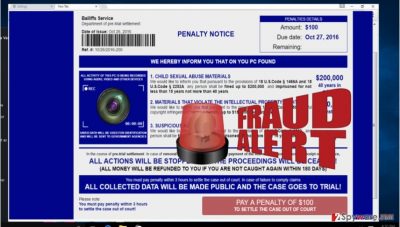
Furthermore, the ransomware in contrast to other standard file-encrypting malware, does not encode the files but rather collects personal details about its victims. Later on, the data is used as the penalty notice material. It generates the profile of “law offender” with full name, address, geographical location. It urges to pay $100 or more within 3 years. Otherwise, the lawsuit will be issued. Surprisingly, the crooks claim that the paid money will be refunded within 180 days if the suspect is not caught again for such activity. The ransomware is so intrusive that it even attempts to locate the webcam files and therefore, make a real photo of a victim. Luckily, the cyber criminals ask to pay by providing the details of a credit card. Therefore, specialists believe that crooks’ whereabouts might be more easily located rather than if they were using Tor network or bitcoin web pages. Ransoc ransomware also starts the processes which enable it to shut down Task manager, Registry Editor, and Command Prompt if the victim launches them.
The transmission ways of the ransomware
Most likely, users who enjoy spending their free time in pornographic or other adult-oriented web pages risk becoming the victims of this virtual infection. It has been discovered that it is associated with JavaErrorHandler.lnk file, so you should be especially vigilant. The virus is really persistent as it also injects HKCU\Software\Microsoft\Windows\CurrentVersion\Run\JavaErrorHandler registry entry. You will not be able to terminate Ransoc hijack by removing this entry in the usual mode as the virus will immediately disable your attempts. You can do it in Safe mode. However, taking into account how elaborate this virus is you should employ a reliable security application for proper termination. This utility is efficient in handling other types of viruses, for example, trojans and browser lockers. Ransoc is detected in the form of Penalty Notice browser virus, so flexible security program is a necessity.
How quickly can I get rid of the malware?
Automatic Ransoc removal might be a better solution. FortectIntego or Malwarebytes effectively locate all elements of the virus and eliminate them. Check whether it is updated and start the scam process. Such program is also practical in escaping other types of malware. If you run into some problems and cannot properly remove Ransoc virus, follow the below-indicated guidelines to regain full control of your device. In addition, you may find the suggestions of data recovery useful. Luckily, this virus does not encode personal data but keeping such tools up the sleeve always comes in handy. Lastly, if you are targetted by the crooks, pay an attentive look to the very style and grammar of the message. Usually, it contains obvious mistakes which suggest that the email or message is fake. In case of real law violation, the penalty notice is not presented as the browser lock-screen and does not offer to pay the “bribe” in order to shake off the responsibility.
Getting rid of Ransoc virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Ransoc using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Ransoc. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Ransoc from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Ransoc, you can use several methods to restore them:
The effectiveness of Data Recovery Pro
This software was mainly created for locating damaged and missing files and documents after a system crash. Nonetheless, it might come in handy as the program decrypting the data after the file-encrypting malware attack.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Ransoc ransomware;
- Restore them.
ShadowExplorer – as an alternative
It is another program worth having on the PC in case of a ransomware assault.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Ransoc and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.





















