RubyMiner (Virus Removal Instructions) - Free Guide
RubyMiner Removal Guide
What is RubyMiner?
RubyMiner malware secretly mines cryptocurrency in the background
RubyMiner malware aims to exploit users' computer resources to mine cryptocurrency. Currently, it particularly targets to generate Monero. Unfortunately, such stealth actions might lead to a significant deterioration of your computer's performance. In fact, you can notice slowdowns and reduced latency[1].
Ruby Miner usually travels as supposedly legitimate software or its crack on file-sharing websites. Once this malware infiltrates the system, it starts to exploit approximately 90% of your computer's CPU and GPU to mine digital currency intensively. Later, the generated crypto tokens are transmitted to the hacker's wallet.
Be aware that criminals are able to get more profits if they connect computers with RubyMiner together. It means that they can increase the necessary computing power to mine cryptocurrency faster. Thus, making more crypto tokens by exploiting other computers without their owners' knowledge.
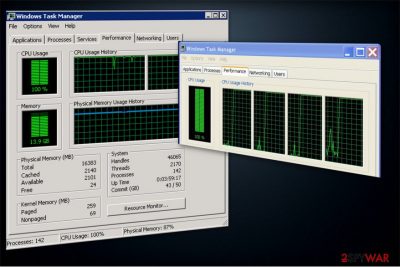
Likewise, the hackers aim to protect the malware from elimination and make sure that it stays on the computer for an extended period of time. Unfortunately, it might be disguised as legitimate system processes in the Task Manager to hide its presence. Therefore, if you notice that a task is overusing CPU[2], have in mind that your computer might be infected with RubyMiner virus.

Furthermore, mining cryptocurrency is not the only malicious activity this malware might perform. If your system is infected with RubyMiner malware, it can also do the following:
- Steal sensitive data, including usernames and passwords;
- Track your keystrokes and log them;
- Download add-ons to update its malicious activity;
- Infiltrate other dangerous computer hazards.
Thus, if you have any doubts about your computer's security, immediately run a full system scan using a professional anti-malware software. You can get FortectIntego to help you check your PC for various infections, including cryptocurrency miners. It will also remove RubyMiner automatically if detected.
However, we kindly ask you not to try to complete RubyMiner removal manually. BedyNet.ru[3] experts say that it might replicate itself to different directories and trick you into terminating legitimate computer processes. Always rely on robust antivirus if you deal with cryptocurrency miners.
Peer-to-peer (P2P) networks are the primary source of malware
Since P2P networks allow users to directly search and download files from the computers of others, criminals use them to distribute malware or even more dangerous infections. However, the malicious programs are re-named to look innocent and useful to trick inexperienced computer users infecting their systems.
Hackers design the malware to resemble software or file which is highly demanded online to reach the maximum number of infected computers. Thus, most of the times malware disguise as legitimate programs, like Photoshop, etc. Additionally, they can design the malware to look like a software crack as well.
Therefore, if you want to protect your system against cryptocurrency miners and other high-risk computer infections, avoid downloading programs, video and audio files or music illegally. Instead, use only official websites to get the software you need. Otherwise, you risk your computer's security.
Learn how to detect and uninstall RubyMiner malware
As we have already mentioned, RubyMiner virus has various capabilities which allow it to hide and protect itself from elimination. Therefore, if you have noticed that your computer's performance has significantly decreased, you should first check the Task Manager for excessive CPU utilization.
In case you have detected a suspicious process which is overusing your computing power, immediately end it. Later, you should employ a robust antivirus to remove RubyMiner from your system. It will scan your computer files thoroughly to identify all malware-related components and uninstall them all.
Our IT experts have carried a research to find the best malware removal tools to help people who are not experienced enough. Their top picks would be FortectIntego, SpyHunter 5Combo Cleaner, and Malwarebytes. However, you might try using an antivirus of your choice as well.
Unfortunately, this is the only way to safely complete RubyMiner removal. We do not advise you to try to locate malware files since you might confuse them with legitimate processes and harm your computer. Additionally, if you are unable to download a security software, check the guide below to reboot your system into Safe Mode and disable the virus.
Getting rid of RubyMiner. Follow these steps
Manual removal using Safe Mode
The easiest way to disable RubyMiner is to boot your system into Safe Mode with Networking. You should be able to get a malware removal tool afterward.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove RubyMiner using System Restore
In case the first method doesn't help, try this one:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of RubyMiner. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from RubyMiner and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.





















