Stampado ransomware / virus (Free Instructions) - Sep 2016 update
Stampado virus Removal Guide
What is Stampado ransomware virus?
The dangers of Stampado virus
Hackers have released another file-encrypting infection — the Stampado virus. Comparing it with other samples of the same virus group, this malware appears to be operating as a ransomware-as-a-service as well. Lately, virus researchers have detected this virus being sold on the darknet for only $39. It is likely that hackers intend to leave no vestige and disappear with the money. In any case, this ransomware should not be underestimated. It encrypts personal files with a popular AES-256 algorithm comprised of a complex mathematically interrelated set of codes. Surely, this ransomware is not a small fry and if your computer has been invaded as well, then, make a rush to remove Stampado before things get worse.
There have been some prior cases when hackers decided to drop their business and sell their creations. Encryptor RaaS and Tox viruses are perfect examples. In the case Stampado malware, cyber criminals do not intend to compete in the dark market and offer the ransomware for a ridiculously cheap price. What is more, after paying the money, there are no additional conditions. The new owners are said to obtain the virus for a lifetime. Furthermore, some suspect that the hackers sympathize with the previously rampaged Locky virus since Stampado attaches .locked extension to all encrypted files. This extension is well-known for being used with .locked. Additionally, according to the newest reports, the threat appends multiple different extensions, which are distinguishable traits of other ransomware, to the files. In the promoted website, the virus may be downloaded in an .exe, .bat, .dll, .scr or .cmd file. Currently, the virus presents a bunch of addresses for the address for the contact purposes including teste@email(.)com, successl@qip(.)ru, paytodecrypt@sigaint(.)org or getfiles@tutanota(.)com.
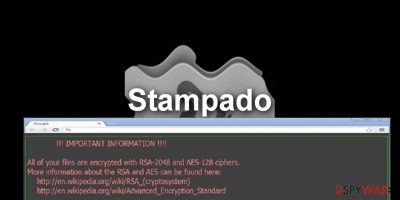
This ransomware might truly become a big player among the viruses for its qualities. Since it uses an elaborate algorithm, decrypting the files without the private key is a real challenge. Additionally, the virus developers employ psychological pressure to urge victims to pay the ransom. Until the transaction is made, random encrypted files are deleted every 6 hours. Due to this peculiarity, the threat received the title of the “Russian Roulette.” The victims are given a 96 hour deadline to pay the money. After the period expires, the encoded data will be lost completely. In any case, you should resist the hackers' pressure and not transfer the cash. There are no guarantees that the data will be returned anyway. Thus, we recommend concentrating on some more realistic and safer data recovery techniques like, of instance, the ones provided at the end of this article.
For a while, it seemed that Stampado moved in the shadows as the ransomware subsided. Unfortunately, it was only calm before the storm. Recently, the developer of this parasite hit the virtual community again, shattering hopes that hackers may have a little sense of decency left. Originally, if one ransomware encrypts your data, other file-encrypting malware automatically evades such files. Nonetheless, the current version of Stampado is able to encode the locked files once again. It means that if you are collecting a ransom for the affiliate virus distributor, you might consider transferring another share to the original owner of this threat as well.
Update September 2016: Emsisoft has released the Stampado decrypter
Finally, after months of the unknown, the Stampado ransomware victims can relax. The virus analysts have come up with a tool capable of bypassing the virus encryption and unlocking your files. The decrypter has been developed by Emsisoft company and is easy to use. To make it work, you will need to provide an email address that the hackers indicate in the ransom note as well as the identification number they give you. The decryption software developers ask the users to mind the capitalization when inserting these two variables into the decrypter because this information is case-sensitive. Otherwise, if you follow the instructions attentively, the data decryption should not cause additional difficulties. Just do not forget to remove the virus from your computer so it doesn't encrypt any more of your files! As for the decrypter itself, you will find its download link next to the data recovery instructions which you can also use in case some new virus version has taken over your PC and the decryptor does not work.
When does the ransomware occupy computers?
Currently, the ransomware is distributed mainly on the darknet. However, with such fair price for the ownership of the virus, it is only a matter of time when the major distribution campaign of Stampado ransomware will be launched. There are multiple theories of how the malware will be spread. Now spam emails are the most popular method. Keep in mind that hackers create highly persuasive and manipulative strategies. Do not rush to open emails sent from transportation agencies, customs, or tax institutions. Their attachments might hide one of the previously mentioned .exe or .dll file with the ransomware within.
The other theory suggests that some hackers might use exploit kits, in other words, trojans. The latter method is extremely dangerous since you cannot possibly detect this sort of malware without having a proper anti-spyware application, for example, FortectIntego. It is of crucial importance to block the trojan before it launches Stampado. Thirdly, other cyber criminals or ransomware sympathizers may opt for P2P file sharing domains or pornographic websites. Since the latter is quite popular among certain groups of users, the probability of getting infected increases all the time.
The elimination of Stampado
We suggest deleting the ransomware by using malware removal utility. This and the primary anti-virus application, are the combination which ensures that no file-encrypting threat sneaks into the computer. The anti-spyware application, for example, FortectIntego or Malwarebytes, is also capable of deleting the threat completely. However, if you encounter problems related to Stampado removal, check the instructions below. After all, users should stay vigilant while surfing the Web because their security of the operating systems is continuously being tested by more and more powerful malware. Lastly, check free Stampado Decrypter below on this page.
Getting rid of Stampado virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Stampado using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Stampado. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Stampado from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.For a long time Stampado ransomware was though to be virtually uncrackable. Not until recently, though, when the virus experts have finally come up with Stampado Decrypter and enabled all of the virus victims to decrypt their personal data. Scroll below to learn how to use this tool. You can also use PhotoRec, R-Studio or Kaspersky virus-fighting utilities or Data Recovery Pro to recover your data in case the decryption tool does not work.
If your files are encrypted by Stampado, you can use several methods to restore them:
Data Recovery Pro solution
This tool is a practical software for recovering and finding deleted or damaged files on your computer. Learn how to use it below:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Stampado ransomware;
- Restore them.
Download free Stampado Decrypter
Famous virus researcher Fabian Wosar developed this free tool for the victims of this ransomware. To use it, you will need to provide the malicious email address that belongs to virus developers and your ID. Then click the “detect” button to reveal your personal “salt”. Since the latest updates, the virus is able to encode the decrypted files again, so make a rush to download and recover your files before it causes more problems on your computer. Do not forget to remove the virus before starting the file recovery process with programs that are given below.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Stampado and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.





















