.bin file extension virus (Free Instructions)
.bin virus Removal Guide
What is .bin file extension virus?
What dangers lie behind .bin file extension virus?
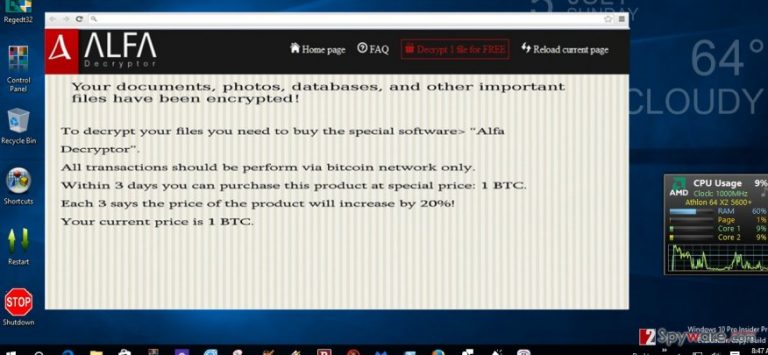
While recently Alfa ransomware has sprung to life, its so-called “sibling” – .bin file extension virus struck the virtual community as well. Unfortunately, both viruses belong to the category of file-encrypting viruses. Obviously, to retrieve the information, victimized users are expected to pay a ransom. This new alternative of Alfa virus has not evolved into a greedy threat yet – it only demands one Bitcoin, which equals to 642,86 USD. Thus, before it becomes one, do not waste time and find out about .bin file extension removal options.
If you are interested in what’s happening in the cyber world, you may have heard of Cerber virus which currently keeps terrorizing the cyber world with more astounding and treacherous virus updates. When a few days ago, Alfa virus hit the spotlight, some researchers have revealed their suspicions that this current .bin virus might be related with the ransomware bearing the name of the mythical three-headed dog. Their encryption techniques happen to be similar. Speaking about this particular ransomware, the name was given due to this ability to append a .bin extension to all encrypted files. According to victims’ reports, the names of corrupted files are modified into a numeric name ending with the .bin extension.
After the threat infiltrates a computer, it will cause some modifications in the registry system, so that the virus can “recover” after the reboot. For you interest, you can find the following registry entries in the OS:
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionWinlogon=%System%ntos.exe
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionRunBestSaveForrYeou
HKCUSoftwareMicrosoftInternet ExplorerToolbar,LinksFolderName = C:WINDOWSNetwork Diagnostic
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun “SD2014” = “%AppData%\.exe”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\
Thus, the threat leaves readme how to decrypt your files.txt, and readme how to decrypt your files.html. Once these files are disclosed, the new tab opens in a browser leading you to the web page of .bin virus. It indicates that in order to unlock the files, you need to buy Alfa Decryptor. Its current value is one bitcoin. Like Cerber, .bin file virus does not indicate any email address. The developers prefer confidentiality as they use bitcoin server to communicate with the victims. Certainly, we discourage you from both, paying the money and downloading the software. Even if the program decodes the highly important information, you never know whether the decryptor will not spy on you and, when the right time comes, will not launch the ransomware again. Instead, concentrate on .bin file extension removal process.
The distribution of the ransomware
It was observed that the malware is dispersed in similar ways like other infamous threats of the same kind. .bin file extension malware usually attacks users via spam emails. Not only cyber security specialists have warned users to pay extra attention but such official institutions as the FBI as well. Due to increased amount of spam and scam frauds, the FBI warned the virtual community not to open emails, especially the attachments of emails, which are seemingly sent from official tax institutions, customs and transportation agencies. Then, you might ask yourself – “how I am supposed to tell a difference between legitimate and a fake email”? Usually, the frauds contain typing and grammar mistakes. If you carefully take a look at the ransom note of .bin file extension ransomware, you might also notice a few mistakes. Alternatively, there is another method to escape the virus. Install an anti-spyware program, for example, FortectIntego. The program is able not only to detect and eliminate the threat, but it can also decrease the number of received spam emails. It can significantly lower the risk to receive an email which contains the ransomware within.
.bin file extension removal guidelines
Since this virus is ransomware and is suspected to be related to other greatly destructive threats, it would be wise to move on to automatic elimination. As previously mentioned, the program will locate the virus and remove .bin file extension virus entirely. The program also safeguards your OS from the viruses of diverse complexity. However, some variations of this malware may shut down the anti-virus program or stop the operation of important system functions. If that happens and you cannot access the required programs, take a look at the recovery instructions delivered below. Lastly, remember to stay vigilant and avoid opening the emails even if they contain the names of official institutions.
Getting rid of .bin virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove .bin using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of .bin. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from .bin and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.







