ContraVirus (Easy Removal Guide) - Free Instructions
ContraVirus Removal Guide
What is ContraVirus?
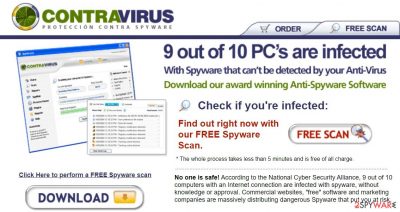
ContraVirus – a corrupt, poor performance spyware remover
ContraVirus is a rogue antispyware that could bring only harm to you and your Windows computer. It is a clone of the illegally distributed VirusBlast rogue and other notorious products. We have carefully tested this fake security tool on several different computers, including immaculate machines and PCs infected with spyware and adware parasites.
Test results revealed that although the program does not produce false positives and actually identifies some malicious parasites, it cannot detect the most widely spread cyber threats and is definitely unable to protect user privacy and system security. Please don't use this product, or if you have it – remove it.
| name | ContraVirus |
|---|---|
| Type | Rogue antispyware application |
| Purpose | Scare users into buying the licensed version by showing non-existing threat notifications, error reports, and similar fake notifications |
| Risks | While the defense of your PC is weakened by the rogue tool, hazardous malware could infect it. If you pay for the fake security software, you also lose your money |
| removal | You should completely remove this application with the help of a reliable anti-malware tool |
| System health check | Restore any damage that the fake security tool caused to your system files and settings by running system diagnostics with the FortectIntego application |
A full system scan performed on a regular modern computer storing hundreds of gigabytes of various data does not take more than 5 minutes. ContraVirus does not check all the files but searches only for known malware, which signatures are in its virus definitions database.
Quick Scan requires even less – only 10 seconds! As you know, currently, there is no such spyware remover capable of thoroughly checking the system so quickly. This means that ContraVirus cannot be trusted. Furthermore, the application refuses to remove any parasites it finds and asks to register and purchase the full version.
Some of its components like SpyWall, Pop-Up Blocker, AntiSpam Filter, and additional plug-ins are also disabled until payment is received. The program's spyware definitions database is outdated, and it doesn't seem to renew as the years go by.
The article's culprit is a clone of VirusBlast. It has a similar interface and consists of analogous components. The official website of the article's culprit is www.contra-virus.com, not that you should visit it or download the rogue antispyware. In fact, please don't do it.
If you enter that site, it immediately offers to scan your device for free to check if there are any cyber infections on it. That's how trojan viruses are spread. Please note that no website is able to determine whether your Windows PC is infected with any kind of malware.
This parasite launches excessive amounts of various fabricated security pop-ups. It also generates many dubious error reports, security warnings, and similar messages designed to trick users into buying the full version of the fake security tool.
Please don't purchase ContraVirus! It is a fraud created by cybercriminals to gain money. This application is not a security tool. Moreover, it could install or let through other malware parasites on the infected system, thus further compromising its security and your privacy and safety.
You have to remove it ASAP. To do that safely, you need to reboot your PC in Safe Mode with Networking and perform a full system scan with proper anti-malware tools such as Malwarebytes or SpyHunter 5Combo Cleaner. If you don't know how to access that mode, please feel free to use our free instructions displayed below.
When the removal is done, it would be wise to take care of the overall system health because ContraVirus might have altered system files to establish persistence, leading to various system failures. Repair the damage your device's system sustained by performing a system tune-up with the FortectIntego software.
Getting rid of ContraVirus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from ContraVirus and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting rogue antispyware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.














