Danger ransomware (Free Guide) - Removal Instructions
Danger virus Removal Guide
What is Danger ransomware?
Danger ransomware — a virus that is related to Scarab crypto-virus family
Danger ransomware is a virus that locks your files and demands ransom[1]. The virus is related to Scarab ransomware which already has more than ten different variants discovered this year. This money-extortion virus family uses a combination of AES-256 and RSA-2048 encryption algorithm. During this procedure, the virus appends either .fastrecovery@xmpp.jp, .fastsupport@xmpp.jp or .onlinesupport@airmail.cc file extensions to make targeted images, documents, videos or archives useless for the victims unless they decide to pay authors of the ransomware for a specific data recovery tool.
| Name | Danger |
|---|---|
| Type | Ransomware |
| Family | Scarab |
| Extension | .fastrecovery@xmpp.jp, .fastsupport@xmpp.jp, .onlinesupport@airmail.cc |
| Ransom note | “HOW TO RECOVER ENCRYPTED FILES-fastrecovery@xmpp.jp.TXT“ or “HOW TO RECOVER ENCRYPTED FILES-fastsupport@xmpp.jp.TXT” |
| Distribution | Insecure spam email attachments |
| Danger level | High. Can lead to permanent data or money loss |
| Decryption | Not available yet |
| Elimination | Best tool for ransomware removal is FortectIntego |
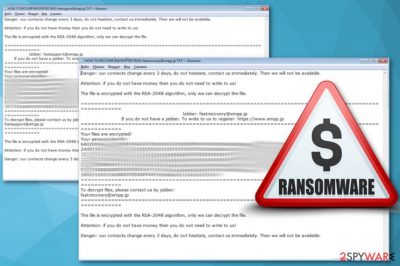
Immediately after files has been changed, you could spot “HOW TO RECOVER ENCRYPTED FILES-fastrecovery@xmpp.jp.TXT“ or “HOW TO RECOVER ENCRYPTED FILES-fastsupport@xmpp.jp.TXT” text files on your computer. Virus places copies of these in every existing folder. This is the ransom notes where authors of Scarab-Danger ransomware put the most important information:
Danger: Our contacts change every 3 days, do not hesitate, contact us immediately. Then we will not be available.
Attention: if you do not have money then you do not need to write to us!
The file is encrypted with the RSA-2048 algorithm, only we can decrypt the file .
=================================================
the Jabber : fastsupport@xmpp.jp
the If you do not have a jabber. The write us to the To register to: hxxps://www.xmpp.jp
As you can see in the ransom message quoted above, the Danger virus developers change their contact information every three days and this is why victims should not hesitate and contact these cybercriminals quickly. Currently known addresses used for the communication with victims are fastrecovery@xmpp.jp and fastsupport@xmpp.jp. However, in the near future, the list of contact email addresses should expand.
Contacting cybercriminals[2] is not recommended because they need only your money and file decryption might be only alleged and barely possible. Specialists at Virusai.lt[3] notes that often these people disappear and ignore their victims after the ransom payment is done. You'd better remove Scarab-Danger ransomware from your computer before it is too late.
Often ransomware developers display little information about the ransom but ask for the specific amount in cryptocurrencies. These criminals are not beating around the bush and stating that people without money do not need to contact them and that they want to get their payment to Jabber account. This only gives more evidence that authors of Danger ransomware virus do not care about victims and are not willing to help each of them.
Therefore, there's no need to trust people who created this malicious program. Even though the official decryptor is not available yet, malware researchers are working on it. Meanwhile, you should get rid of the virus and try alternative recovery methods. However, if you have data backups, you do not need to worry about anything. Though, before file recovery, you need to clean your PC.
Danger ransomware removal should be done with professional help and all the seriousness in mind. This is not just an intrusive program, this is a malicious virus that contains various harmful pieces. Anti-malware tools like FortectIntego can do a proper full system scan and get rid of ransomware related applications and tools. 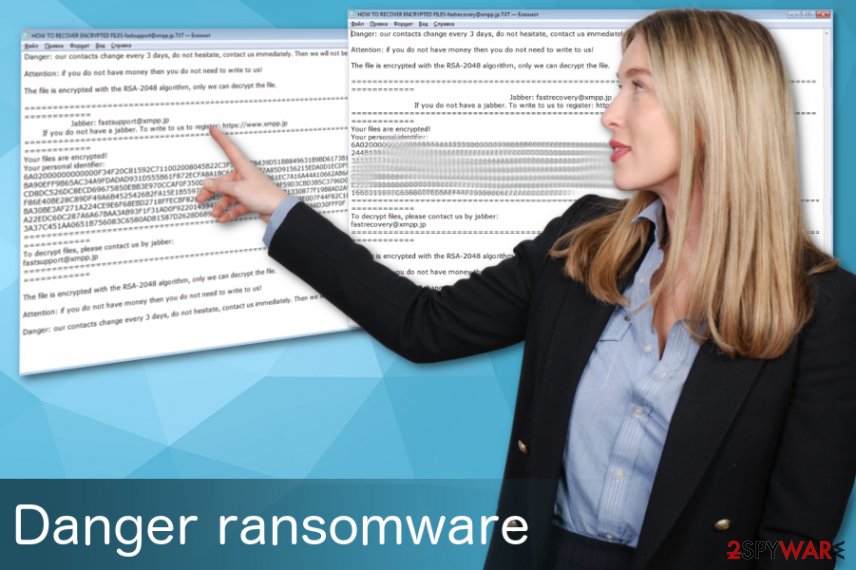
Multiple malware spreading ways include spam email attachments
Ransomware viruses can spread in various ways, such as:
- fake software or tool updates;
- malicious spam email attachments;
- breaking through RDP unprotected configuration;
- freeware bundles;
- trojan viruses;
- web injects;
- fraudulent downloads.
The most common is a spam email. They often contain attachments that could be filled with macro viruses and those little things spread ransomware onto your computer. Also, these letters may look safe and legitimate because of the known company names on the addresses or email itself. The same trick is used with the attachments. Even though they are compromised, they still look as safe Word or another popular document.
This is the main fact that you need to pay attention while browsing throughout your email boxes. Opening and possibly purchasing anything from those attachments can lead to cyber infections or even ransomware attacks. You need to be aware of these threats behind every suspicious site or email. Caution and knowledge are critical here.
Get rid of Scarab-Danger ransomware as soon as possible and avoid more significant harm
To remove Danger ransomware from your computer entirely you should use certified and trustworthy tools or programs like FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes. This option in virus elimination can ensure you are deleting all of the remains that might be with this virus. Ransomware is malicious and harmful, but also there is a possibility that they contain other tools or programs.
Those programs can do more damage to your system than the ransomware itself. The more time you give for, the more access they can gain. Scarab-Danger ransomware removal is vital to do quickly and correctly so you can avoid any repetition in the future. We have a step-by-step guide below for better explanation and virus removal.
However, we do not recommend to focus on file decryption until you double-checked your system is clean. Only then you can insert an external backup and recover your data. Because you plug in any device to the insecure system, your files could be corrupted again, and this means you lose your data permanently.
Getting rid of Danger virus. Follow these steps
Manual removal using Safe Mode
When dealing with Danger ransomware, the first thing you can do is reboot your system in Safe Mode with networking
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Danger using System Restore
System Restore feature is a good option too
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Danger. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Danger from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Danger, you can use several methods to restore them:
Data Recovery Pro is specifically designed for file restoration
If you accidentally deleted your files or ransomware encrypted them you can try to use Data Recovery Pro and restore your data
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Danger ransomware;
- Restore them.
If you want to recover the most important individual files, you can use Windows Previous Versions feature
However, this feature can be useful if System Restore was enabled beforehand
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer can help you to recover encrypted files
If Danger ransomware encrypted your data but did not delete Shadow Volume Copies, you can use ShadowExplorer for data recovery
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption tool is not available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Danger and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.





















