Liansatrickth.info (Free Instructions) - Chrome, Firefox, IE, Edge
Liansatrickth.info Removal Guide
What is Liansatrickth.info?
Liansatrickth.info is a rogue website that is used for increasing the number of Puch Notifications
Liansatrickth.info is a website that uses misleading strategies to make people subscribe to Push Notifications[1]. These notifications are getting popular among online business owners, advertisers, and website runners as they allow dynamically change the way they engage with the retain users. Unfortunately, untrustworthy parties keep misusing this legitimate service, thus making it less effective.
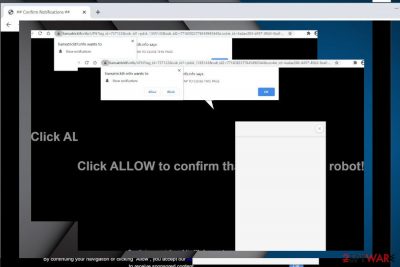
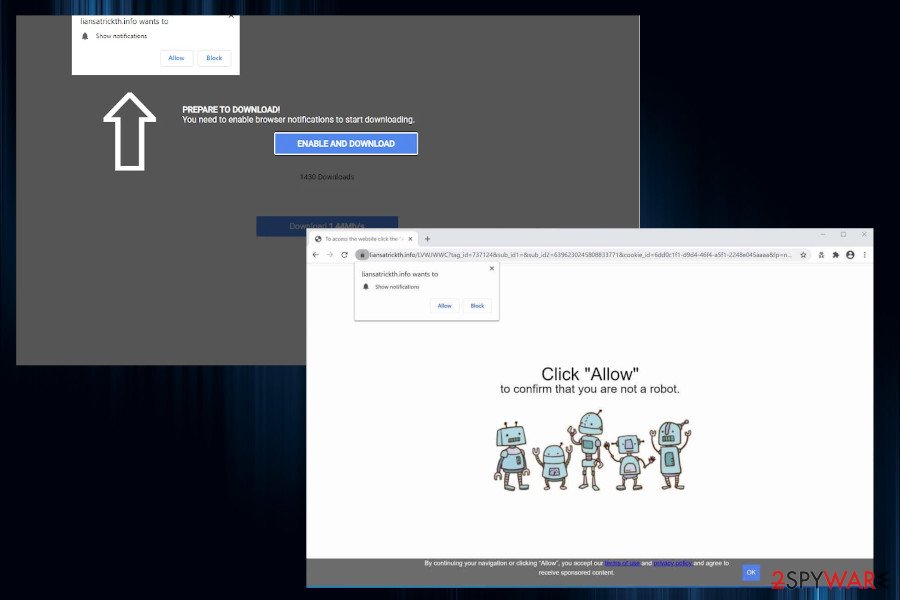
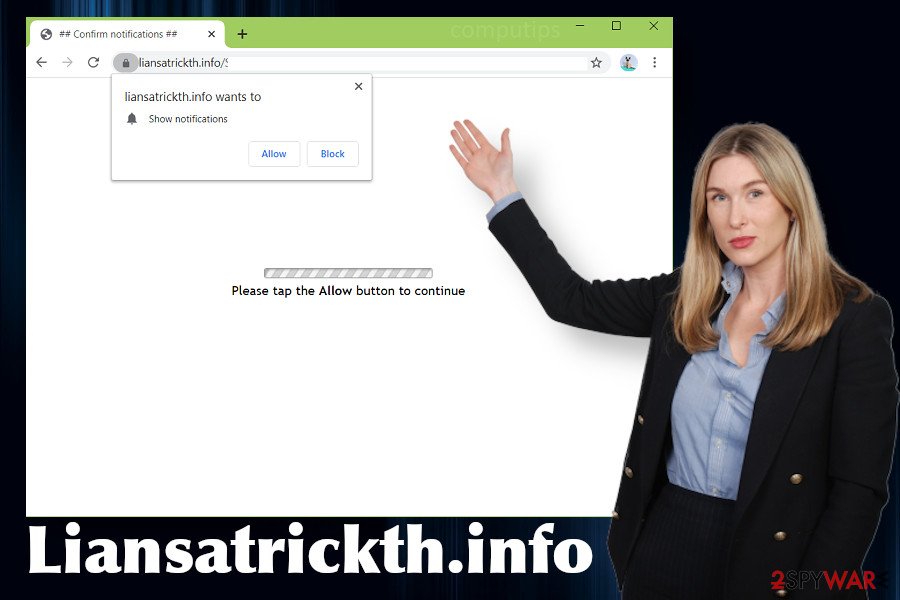
Liansatrickth.info is one of the phishing sites used by scammers to make people unintentionally subscribe to third party Push Notifications. Typically, people start being exposed to this domain by adware programs that initiate regular redirects to this and similar domains (Pushtoday.icu, Pushlommy.com, Enewssubspush.info, and many others). The site does not show any content except a pop-up box saying “Liansatrickth.info wants to show notifications” and a false claim, such as click Allow to start downloading or click Allow to confirm that you are not a robot.
It is not difficult to disable Liansatrickth.info popups by resetting the affected web browser or removing the URL from the Notifications section. However, if this site is triggered by adware or another potentially unwanted program (PUP), redirects might continue. In such a case, you should delete the unwanted application in the first place and then restore the browser's settings.
| Name | Liansatrickth.info |
| Type | Phishing website |
| Classification | Adware/Potentially unwanted program (PUP) |
| Symptoms | Web browser keeps redirecting to this website (or similar), generates commercial content |
| Main danger | Can expose to malicious websites or display fictitious ads that download malware |
| Removal | The notifications can be stopped by resetting the web browser. However, the Liansatrickth.info redirects are usually associated with adware program. Thus, complete elimination of intrusive ads and redirects requires PUP removal. This can be done manually or with the help of anti-malware software |
| Repair | The system gets filled with PUP files once it gets installed. Unfortunately, some of those files remain even after PUP removal. Thus, we recommend regularly scanning the machine with FortectIntego |
The Liansatrickth.info redirects typically expose people to a misleading website that always contains a pop-up alert on the top left side of the window saying that “Liansatrickth.info wants to show notifications.” That's a rule. The rest of the content and background may vary.
Cybersecurity experts from Dieviren.de[2] found a tendency of Liansatrickth.info virus to mimic a legitimate Adf.ly background. Since Adf.ly[3] is a legitimate service that many active Internet users know, this trick may work and arouse the sense of trustworthiness. Besides, to make people click the Allow button and enable Push Notifications, crooks take advantage of such and similar claims:
Click ALLOW to confirm that you are not a robot
Please tab the Allow button to continue
You need to enable browser notifications to start downloading
Do not fall for the trick, as it's a scam. The Liansatrickth.info notifications are not generated by legitimate sites and businesses. They are used for promoting random services and products that third parties seek to promote, so you should not expect any relevant content.
The Liansatrickth.info ads may appear to be very intrusive, as clicking on the causes redirects to suspicious sites that promote infamous system optimization tools, PUPs, and other useless software. Besides, you should also be cautious about scam sites that offer you to claim a prize, participate in a short online survey, or warn about a cyberattack targeting your machine. These phishing sites are widely used by scammers who seek to harvest people's credentials or spreading malware.
You should immediately remove Liansatrickth.info virus as soon as it starts exhibiting the presence. Apart from the visible symptoms, the adware can run in the background and leak your browsing history regularly. It may allow third parties to access your search queries, mostly visited websites, IP addresses, clicks, and similar.
Liansatrickth.info removal should be initiated with professional anti-malware tools. Besides, a scan with FortectIntego is highly recommended afterward due to possible alterations to the startup and registry entries. As a consequence, the system may run in a slower manner, some system programs may launch for a long time, and other side effects can manifest. Therefore, optimization is highly recommended.
Liansatrickth.info Push Notification removal from Chrome and other browsers
If after a full system scan the AV tool did not found malware, it means that you must have accidentally subscribed to Liansatrickth.info Push Notifications. Consequently, Chrome or another web browser keeps displaying sponsored content during your web browsing. To disable those pop-ups on the web browser, you should perform these steps:
- Open the web browser's settings. Usually, they can be accessed by clicking on the three vertical dots positioned on the top-right of the window and selecting Settings.
- Then opt for Advanced and look for Content settings or Site settings.
- Select Notifications.
- Look for the Liansatrickth.info domain name and select the Block button or Remove from the list.
- We recommend doing the same with other suspicious/unknown domains to prevent suspicious ads.
Third parties misuse legitimate distribution technique to spread malware
It's a known practice that untrustworthy third parties are trying to promote their content using controversial distribution methods. One of the most widely used PUP dissemination technique is known as Bundling. This method is a legitimate way to spread several applications contracted in one pack. Originally this method has been used to allow people to test new applications for free. Unfortunately, bundling has soon been revealed by criminals who started spreading adware and browser hijackers this way.
Furthermore, cybersecurity experts warn that adware and other PUPs can also be disseminated via unprotected networks and third-party sources that can easily be exploited by criminals. Scripted websites can work like click-to-download, so once landing on an infected site, you can agree with the installation of malware.
To prevent such happening, you should be very cautious when web browsing the Internet. Keep a professional AV program activated all the time and make sure that it has features like real-time protection, sandboxing, and FireWall. In addition, carefully select the content that you are downloading. Perform the installation process by running the Advanced/Custom setup to spot additional components and reject them.
Liansatrickth.info removal: Mac and Windows tutorial provided
When your machine gets infected with adware, one of the side effects may be the Liansatrickth.info redirects. In addition, you can notice intrusive ads, promotional content, system slowdowns, web browser's sluggishness, and similar. To fix that, you should scan the machine with a reputable anti-malware and eliminate PUPs one-by-one.
However, sometimes Liansatrickth.info removal might not be necessary if it turns out that you have accidentally agreed to receive third-party notifications during a visit on a misleading site. In this case, you should disable those notifications (as explained above) or reset the web browser's settings.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Liansatrickth.info. Follow these steps
Uninstall from Windows
Liansatrickth.info pop-ups can occupy all web browsers installed on Windows machines. If they are triggered by an adware-type application, then you should follow this guide to get rid of all PUPs.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
If your Mac keeps redirecting to Liansatrickth.info phishing site, you should first check the system for malware.
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Based on people's reports, the Liansatrickth.info virus notifications tend to harass Google Chrome users in particular. To restore the web browser to the state before the subscription of intrusive ads, do the following:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Liansatrickth.info registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Push Notifications Read more at: https://vwo.com/push-notifications/?utm_campaign=tof_ugc. WVO. Automated marketing campaigns.
- ^ SICHERHEIT- UND SPYWARE-NEUIGKEITEN. Dieviren. Virus and spyware news.
- ^ Make Money with Short URL Service adf.ly. Carnaghan. A blog of Ian Carnaghan.























