News-wuweci.cc ads (fake) - Free Guide
News-wuweci.cc ads Removal Guide
What is News-wuweci.cc ads?
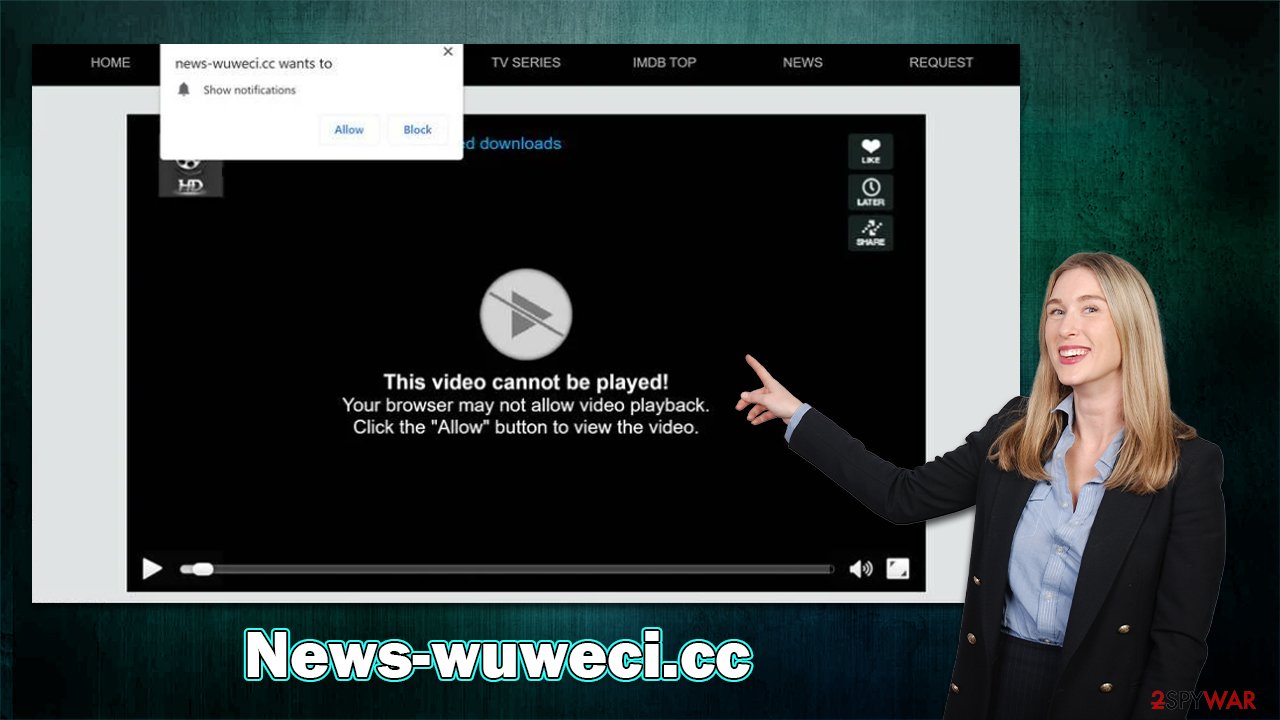
News-wuweci.cc is a fake website trying to convince people click the “Allow” button to show them malicious push notifications

Many computer users have recently reported receiving News-wuweci.cc ads showing up out of nowhere, and you may be wondering why you're seeing them too. These pop-ups cause because you permitted the site to send push notifications to your device at some point. If you don't recall giving permission, it's not surprising – phishing[1] messages are often used to trick people into doing so without realizing it.
Most people are unaware that they've been tricked, so they don't know where the activity is coming from. It also does not help that most don't have much experience with the push notification feature, which is generally extremely popular and employed by many legitimate websites. Scammers behind News-wuweci.cc also make use of it in a way that lets them deliver intrusive advertisements directly to victims' screens.
The worst part of it all is that these pop-ups could include all sorts of malicious content in them – links to suspicious websites that include promises of free gifts, menacing messages about virus infections or outdated software, and more. Please ignore everything coming from the site, as you could fall victim to even more scams, resulting in malware infections, financial losses, or even identity theft.[2]
| Name | News-wuweci.cc |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | After users click the “Allow” button within the prompt upon site entry |
| Symptoms | Pop-up notifications are shown on a desktop at random times |
| Risks | Push notifications sent by the site might result in you visiting dangerous websites; consequently, you might suffer from malware infections, financial losses, or personal data disclosure to malicious parties |
| Removal | You can stop the site from sending you notifications by following the steps below. To keep your computer safe, we also recommend scanning it for adware with SpyHunter 5Combo Cleaner security software |
| Tips | Make sure you clean your browsers after you delete PUPs from the system. To do that automatically, you can use FortectIntego |
Adware could cause redirects to suspicious websites
Scammers are well aware of the fact that few individuals would be ready to view websites that may jeopardize their security and that of their computers. In fact, it is unlikely (but not impossible) to come across a malicious website using a search engine like Google or just browsing websites that are regarded as trustworthy.
When users themselves access websites with questionable origins, problems arise. For instance, people searching for software cracks to get around Windows or other common software licensing procedures run the risk of being diverted to fraudulent websites and getting their systems infected with destructive malware, such as ransomware[3] which would encrypt all personal files and then demand ransom for their recovery.
A further possibility is that adware placed on users' computers would drive them to News-wuweci.cc or a similar website. Many people might not even be aware that adware operates on their devices since it is distributed through software bundling and other deceptive methods. The SpyHunter 5Combo Cleaner and Malwarebytes tools are ideal for adware removal – it is crucial to make sure that the system is examined for infections.
We advise doing a FortectIntego repair and maintenance tool scan on the computer after removing any malware, as it may be very helpful in dealing with system damage and other leftover files. Likewise, the app is capable of clearing browser caches for better privacy and removing junk from the device.
How to deal with malicious push notifications
News-wuweci.cc is just one of the hundreds of websites that arise on the web every day, trying to scam users into pushing “Allow” right after entering. If the request would be clear cut, rarely would anyone agree to it. However, scammers employ various social engineering tricks to make sure that accepting notifications would make sense. These are a few examples of messages you may encounter after entering this site:
- Click Allow to confirm that you are not a robot
- If you are 18+, click Allow
- Click “Allow” to win the prize and get it in our shop!
- Press “Allow” to watch the video
- Click Allow to start downloading, etc.
Week-tale.xyz, Garnly.com, or Conatysystems.com are just a few examples that employ identical messages and images to convince people to subscribe. Since users have previously dealt with verification methods such as captcha, they might not think twice and consider it just another such check.
However, keep in mind that accepting push notification prompts would only allow that particular website to deliver information directly to your screen at any point, so you should be careful. If you were already tricked or you clicked the “Allow” button by accident, you can block the website from sending you pop-ups via the browser settings as follows:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.
![Stop notifications on Edge 2 Stop notifications on Edge 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Ali Hussain. What Is Identity Theft?. Investopedia. Sharper insight, better investing.
- ^ Ransomware. Wikipedia. The free encyclopedia.






