PopCornTime ransomware / virus (Improved Guide) - Dec 2016 update
PopCornTime virus Removal Guide
What is PopCornTime ransomware virus?
The dangers of PopCornTime ransomware:
PopCornTime virus is a crypto-ransomware infection that originates from HiddenTear source code and imitates an online movie streaming service to infect computers. Please beware that the original PopCorn Time website has nothing to do with this virus. After finding out that their domain name was exploited for hacking purposes, the administrators of this domain issued a public warning [1]. Interestingly, the software which shares popularity among countless of netizens worldwide also sparks the extortionists’ imagination. It is not the first time since the domains have been compromised. There were multiple cases when the domain was suspected of spreading malware. Using popular brand names is not an uncommon phenomenon among the ransomware hackers. Recently, Locky ransomware has been discussing under Amazon name to infiltrate netizens‘ devices [2]. DailyMotion has also suffered a hijack assault [3]. In relation to this, the ransomware hides under PopCorn Time name, but it marks files with a distinguishable .filok and .kok file extension. It is interesting that before starting the encryption, the virus looks for specific files called been_here and server_step_one. The presence of these files on the computer indicate that is is already infected and no further actions need to be taken. In all other cases, the virus may initiate the lockscreen and begin the encryption. Even if this cyber misfortune has befallen you, there is no need to panic, install FortectIntego to remove PopCornTime.

Vindicating the name of the software is becoming a more difficult task for its authors. Hackers still come up with new malware versions which in one way or another exploit Popcorn Time name. It is not surprising since watching movies without charge is one the most popular activities in the cyber space. Luckily, a famous virus researcher Michael Gillespie had found this roaming malware before it wreaked more havoc on the Internet. PopCornTime ransomware exploits SHA-256 hash encryption technique to encode the files. Depending on the technical capacities of your operating system, the malware may take a couple of minutes up to half an hour to encode your files. The very process is disguised with a fake software download screen, so the victims usually do not suspect the encryption is even taking place. Later on, the cyber infection opens up the .txt and .html files named restore_your_files.html and restore_your_files.txt. to inform you about the conditions to retrieve the data. However, paying ransom does not boost up your chances of recovering the files [4].
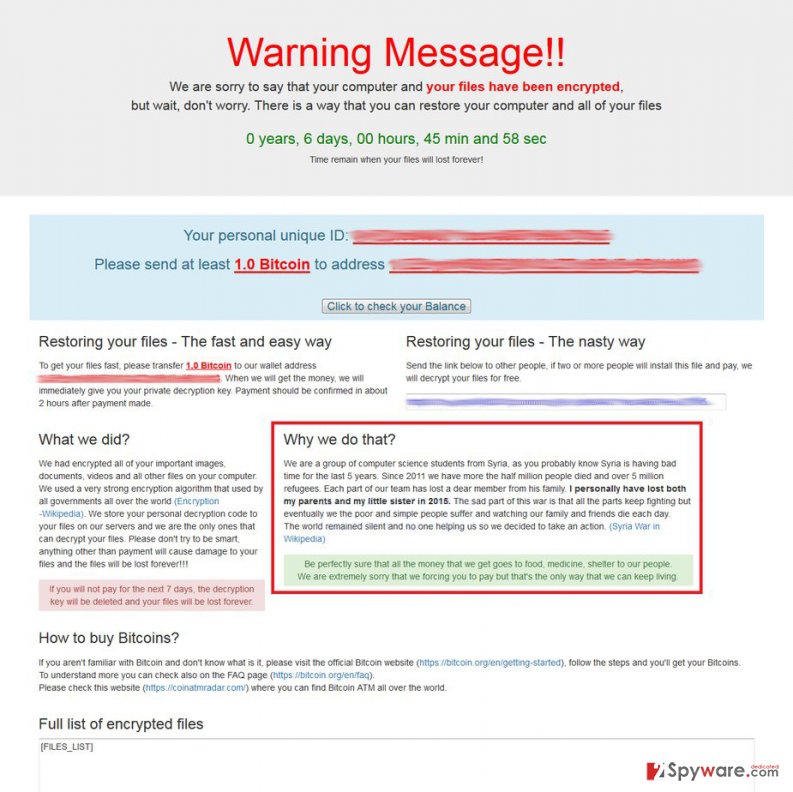
Update: PopCornTime ransomware introduces new and very nasty data decryption option
As evil as they are, PopCornTime virus developers have not used up all of their malicious potential just yet. The hackers are currently implementing a new ransomware distribution scheme which involves exploiting its victims for spreading the malware voluntarily. Well, not entirely so. The users are offered ransomware distribution as an alternative way of receiving the decryption key. So, instead of paying for it, they have to infect two more computers with this virus. This can be utilized by spreading its referral link included in the ransom note. The link leads to a TOR server which contains a file with PopCornTime payload. The users who download the file are immediately infected and the cycle perpetuates. Thus, the virus dispersion is expected to grow more rapidly in the upcoming weeks. Besides, the hackers now also threaten to start deleting the encrypted files if the victim fails to submit the correct decryption key 4 times in a row. This new intimidation technique that the hackers have implemented in the program’s source code might add to the virus growth as well.

Ransomware dispersion techniques:
The distribution methods of PopCornTime malware are not limited to spam emails. The latter channel has facilitated the hijack of countless ominous ransomware threats such as Cerber virus [5]. In the case of PopCornTime hijack, the very malware is delivered to victims‘ computers via Trojan-Dropper.Win32.Dapato.opig, and Win32/Trojan.Dropper.bed trojans. Nonetheless, not all security tools are able to detect it so far. Updating your anti-virus utilities should be your current priority. Therefore, restrain from using PopCorn Time domain for a while until virus researchers determine where the virus comes from. Lastly, if you spot that Popcorn Time.exe is trying to invade the system, terminate the process say exiting any installation windows and check the task list in the Task Manager. Let us proceed to PopCornTime removal.
Can I remove PopCornTime virus by myself?
The first thing you should do is either to install an anti-spyware application, such as FortectIntego or Malwarebytes, or update the current. Afterward, initiate the scanning progress. Usually, PopCornTime removal only takes a couple of minutes. Keep in kind that security tools do not decrypt the files so you will need to use extra utilities to recover your encrypted personal data. Only when the elimination process is finished, you can proceed to the data recovery methods. If you struggle to remove PopCornTime virus because of off system errors, enter the Safe Mode with Networking and follow the below-displayed guidelines.
Getting rid of PopCornTime virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove PopCornTime using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of PopCornTime. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove PopCornTime from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by PopCornTime, you can use several methods to restore them:
Does Data Recovery Pro help to decrypt files?
Regarding current ransomware activity on the Web, the developers of this program updated the software and now it may be able to decrypt some of your files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by PopCornTime ransomware;
- Restore them.
ShadowExplorer and its operation peculiarities
This utility recreates the files by using volume shadow copies which are located in a remote folder of Windows OS.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from PopCornTime and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Ernesto. Popcorn Time Warns Users Against Malware and Scams. TorrentFreak. A publication dedicated to bringing the latest news about copyright, privacy, and everything related to filesharing.
- ^ Millions of Amazon Users Targeted with Locky Ransomware via Phishing Scams. TrenMicro.Securing Your Journey to the Cloud.
- ^ Swati Khandelwal. dailyMotion Hacked – 85 Million User Accounts sSolen. The Hacker News. Security in a serious way.
- ^ Ryan Francis. Why these victims decided not to pay the ransom. CSO provides news, analysis and research on security and risk management.
- ^ David Bisson. Spam campaign tiptoes via Tor to deliver Cerber ransomware. Graham Cluley. Award-winning computer security news. advice, and opinion.





















