CryptConsole ransomware / virus (Removal Instructions) - Jun 2018 update
CryptConsole virus Removal Guide
What is CryptConsole ransomware virus?
CryptConsole – a decryptable ransomware that keeps coming back with new variants in 2018
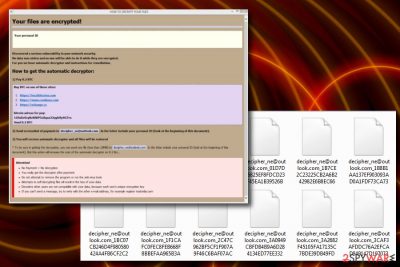
CryptConsole is a ransomware virus that has been active since January 2017. The 2.0 variant came soon after the first one – in February of the same year, and the latest member of the virus family is CryptConsole 3. Previous versions of this malware have been asked 0.2 Bitcoins for data recovery; then hackers proceeded to demand 0.7BTC, while the most recent releases, like xzer@tutanota.com, demand a lesser payment of $1000 in Bitcoin. The functionality of all versions of ransomware has similar features but uses different contact email address and the file extension (or a prefix) name. Latest virus variants use redbul@tutanota.com and heineken@tuta.io email addresses used to contact virus authors. Fortunately, all variants of this cyber threat seem to be decryptable, except for one – the latest version of the CryptCosnsole ransomware-type virus.
| SUMMARY | |
| Name | CryptConsole |
|---|---|
| Type | Ransomware |
| Versions |
someone_ne@india.com, decipher_ne@outlook.com, unCrypte@outlook.com, qar48@tutanota.com, xzer@tutanota.com, szem@tutanota.com, desparo@tuta.io |
| Ransom size | 0.14, 0.2 or 0.7 BTC |
| Distribution | Spam email attachments, malicious websites, etc. |
| Danger level | Medium. Does not encrypt files; however, renames them so that the victim cannot use them |
| Elimination | Automatic deletion only – download FortectIntego or Malwarebytes |
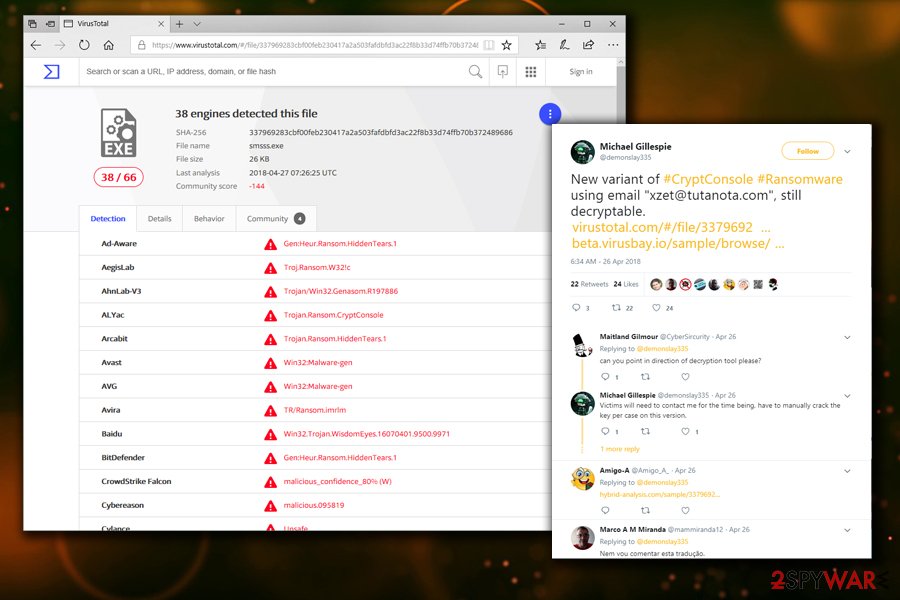
Changing file names back and adding the correct extension would make data usable again. Fortunately, official decryptors are available to execute this task. However, in April 2018, security researcher Michael Gillespie[1] discovered a new variation of the virus, which appends xzet@tutanota.com extension. According to the specialist, this version of CryptConsole is still decryptable, although it requires the researcher to look at each case individually as the decryptor might not work.
Following that, in June 2018, Gillespie discovered[2] the new variant of CryptConsole which uses xser@tutanota.com email address and demands $1000 in BTC for file release. Nevertheless, decryption of this version is possible, and users affected by this virus should contact the researcher. As of now, he cannot disclose weakness of the ransomware, as it is still extremely active.
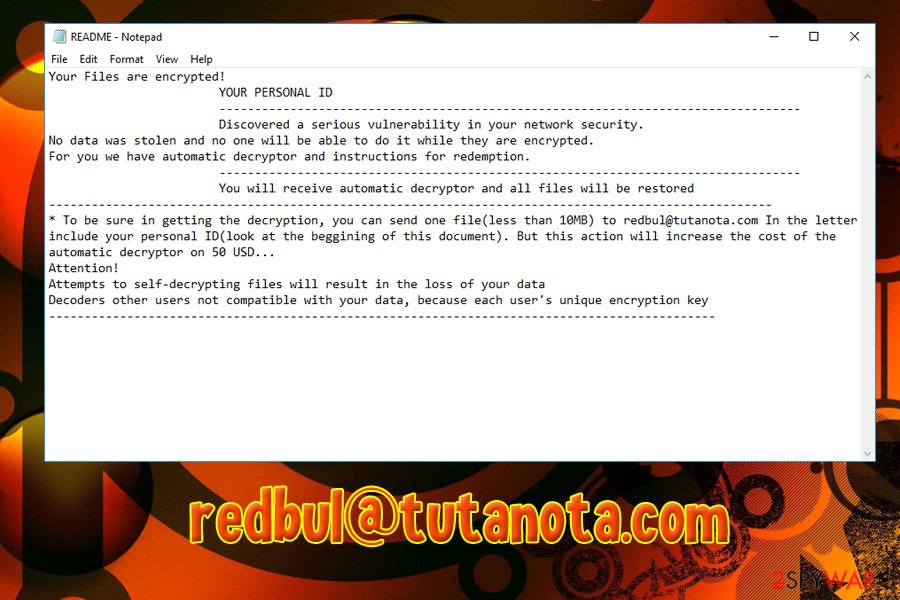
Ransomware did not wait for long to show up again. In early July 2018, security experts discovered another two new variants of CryptConsole virus – Redbul@tutanota.com and heineken@tuta.io. Similarly to previous versions, the malware uses an email address + randomly generated numbers as file extensions. Redbul@tutanota.com uses rEADME.txt or readme.txt ransom notes, and also offers users to decrypt one file (up to 10MB) for an extra of $50 payment for the service. Both of these versions are decryptable.
The second ransomware's version – CryptConsole2 seems to be more sophisticated than its predecessors. This version can encrypt victim's files with AES or similar encryption algorithm (experts are still discussing on this part) and then require 0.7 BTC for their decryption. The virus also drops “README.hta” ransom note that asks the victim to use xzer@tutanota.com or desparo@tuta.io for getting in touch with its developers. We do not recommend that as each of its versions are decryptable.
The latest variant of the virus, dubbed CryptConsole-2018, includes all the versions which appeared in 2018. The most famous one is Sequre ransomware, which appends sequre@tuta.io_ [hex], sequre@tuta.io_ [random_0-9A-Z] or [ransom_email] _ [0-9A-the Z] file extensions, and demands 0.14BTC for file release. The virus also drops ransom note called HOW DECRIPT FILES.hta which is displayed in virtually the same manner as previous messages from hackers.

Origins of the CryptoConsole are still unknown
At first, it was believed that Crypt Console ransomware is closely related to Globe ransomware as the .HTA file presented to victims looks identical to the one which is used by Globe.[3] However, the virus does not encrypt[4] data, and all threats are bogus. Nevertheless, CryptConsole removal should be performed urgently (it might open the doors to other severe infections).
The ransom note of this virus reads:
Your files are encrypted!
Your personal ID:
Discovered a serious vulnerability in your network security.
No data was stolen and no one will be able to do it while they are encrypted.
For you we have automatic decryptor and instructions for remediation.
How to get the automatic decryptor:
1) 0.7 BTCBuy BTC on one of these sites:
https://localbitcoins.com
https://www.coinbase.com
https://xchange.ccbitcoin adress for pay:
Send 0.7 BTC2) Send screenshot of payment to someone_ne@india.com. In the letter include your personal ID(look at the beginning of this document).
3) You will receive automatic decryptor and all files will be restored
* To be sure in getting the decryption, you can send one file(less than 10MB) to bit-tray@tutanota.com In the letter include your personal ID(look at the beginning of this document). But this action will increase the cost of the automatic decryptor on 0.1 btc…
Attention!
• No Payment = No decryption
• You really get the decryptor after payment
• Do not attempt to remove the program or run the anti-virus tools
• Attempts to self-decrypting files will result in the loss of your data
• Decoders other users are not compatible with your data, because each user’s unique encryption key
• If you can’t send a message, try to write with the other e-mail address, for example register mail.tutanota.com

As you can see, the victim is asked to send 0.7 or more Bitcoins to a provided Bitcoin address, make a screenshot of the transaction document and send it to criminals via email. Currently, known email addresses that are associated with the virus are:
- someone_ne@india.com;
- something_ne@india.com;
- decipher_ne@outlook.com;
- unCrypte@outlook.com;
- qar48@tutanota.com;
- xzet@tutanota.com;
- szem@tutanota.com;
- desparo@tuta.io
- xser@tutanota.com
- redbul@tutanota.com
- heineken@tuta.io
The files are renamed accordingly using these email addresses, depending on the version. For example, a file called picture.jpg gets renamed to picture.jpg.someone_ne@india.com or picture.jpg.qar48@tutanota.com. This behavior mimics working ransomware. However, as we already mentioned, files do not get corrupted, unlike in the case of Cerber[5] or Spora viruses.
If this foolish virus has attacked you, better remove CryptConsole or its second version ASAP with anti-malware tools like FortectIntego or SpyHunter 5Combo Cleaner. There is already a decrypter for this virus available, and you can find its download link below the post.
What is interesting about this virus is that it suggests the victim try the imaginary “decryption service.” It asks to send a file not larger than 10MB to one of the emails mentioned above and include the personal ID, which is written in the HOW TO DECRYPT YOUR FILES ransom note. However, other viruses typically suggest this proof that decryptor exists for free, and CryptConsole ransomware doesn’t.
It says that if the victim wants to restore one file and find out that the decrypter actually works, the initial ransom price increases by 0.1 BTC. No matter what, you shouldn’t care about the price of the ransom because you can recover your files for free. Before you use the decrypter created by a malware researcher M. Gillespie, you should complete the CryptConsole elimination procedure using proper anti-malware tools.
Ransomware might sneak into device not only from a malicious email
Criminals distribute malicious payload using social engineering.[6] They often send thousands of spam emails directed to unsuspecting users. Their primary goal is to make the malicious file look like it is a safe one.
So they create a document named, for example, “Invoice,” “Scan,” “Purchase Order” or similar. Typically, they use .doc, .pdf or .txt file formats (however, other file types can be used as well), and insert a script into them, which has to be opened with Macro function. If the victim proceeds with opening the file, the malicious script downloads malware from the Internet and immediately infects the entire system with it, meaning that all data gets corrupted.
Other ransomware viruses can infect systems by using vulnerabilities in the system, so it is advisable to keep all programs up-to-date and protect the system with decent anti-malware software.

Delete CryptConsole and recover your files
Security experts[7] advise that the best way to remove CryptConsole virus is to perform a system scan with anti-malware software. Such scan checks the system and finds all malicious files associated with the malware. You might also detect some potentially unwanted programs on the system.
It goes without saying that to removing spyware/malware automatically takes less time and detects more infectious files than the manual method. Besides, ransomware is a very complex program, and it is tough to remove it. Therefore, before you run the system scan, read these CryptConsole removal instructions first. Then, you can download the decrypter and learn how to rename your files to previous states.
Getting rid of CryptConsole virus. Follow these steps
Manual removal using Safe Mode
To start the removal process, reboot your PC using explanations provided below. This will help to deactivate the virus. In some cases, this step is not necessary, however, it is always better to remove malware when the computer is in a Safe Mode.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove CryptConsole using System Restore
Try using System Resore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of CryptConsole. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove CryptConsole from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Data Recovery Pro was designed to fix corrupted files. In some cases, it might help with decrypted files.
Windows Previous Versions can be useful if Windows Restore function was enabled at the time of file encryption.
If the virus did not delete Shadow Volume copies – this method will help.
If your files are encrypted by CryptConsole, you can use several methods to restore them:
Data Recovery Plus might be useful
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by CryptConsole ransomware;
- Restore them.
Windows Previous Versions feature
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Recover your files using Shadow Explorer
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Restore files entirely with CryptConsole decryption tool
As we have already mentioned, there is a CryptConsole Decrypter available, and you can use it absolutely for free. Download the tool from here and start restoring your files. Warning: The Google Safe Browsing mode considers this download page as not secure. Use this tool at your own risk! Although we are sure that the tool is safe, better scan the system with anti-malware tools just to be sure. You can remove the decrypter right after restoring your files.
For the newest versions of CryptConsole ransomware, you should contact Michael Gillespie as every infection has to be fixed manually by the researcher. You can find his Twitter profile here.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from CryptConsole and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Michael Gillespie. New varaint of CryptConsole Ransowmare. Michael Gillespie on Twitter.
- ^ Michael Gillespie. Spotted another CryptConsole version. Michael Gillespie on Twitter.
- ^ Marshall Honorof. Globe Ransomware Channels Purge Movies, Ruins Files. Tom's Guide. Tech Product Reviews, Top Picks and How To.
- ^ Rick Correa. How Fast Does Ransomware Encrypt Files? Faster than You Think. Barkly Blog. Endpoint Security Blog.
- ^ No slowdown in Cerber ransomware activity as 2016 draws to a close. Microsoft Malware Protection Center. Threat Research .
- ^ Nate Lord. Social Engineering Attacks: Common Techniques & how to Prevent the Attack. DigitalGuardian. A new Dawn for Data Loss Prevention .
- ^ Faravirus.ro. Faravirus. Romanian IT professionals.





















