Spora ransomware / virus (Removal Instructions) - updated Aug 2017
Spora virus Removal Guide
What is Spora ransomware virus?
Spora continues spreading all over the world
Spora is a ransomware-type virus that was first discovered on January 10, 2017. Malware uses an advanced combination of AES and RSA encryption keys to corrupt users data on the affected computer. Despite astonishing appearance and worldwide prevalence, virus activity has been slowed down for a couple of months. However, on August researchers warned about ransomware’s return.
Spora ransomware appears to be a data-encrypting Trojan[1] which derived from CryLocker. Malware started communicating with its victims only in the Russian language. However, after several weeks of operation, it has started traveling the whole world wide web. Currently, the most affected countries are Mexico, Poland,[2] and Sweden.[3]
It gets executed with the help of close.js file. JavaScript files are popular tools among hackers. Surprisingly, the malicious program uses an entirely different, and very complicated data encryption algorithm which seems to be immune.
Apparently, Spora virus creates contents of .KEY file by creating RSA key, encrypting it with a newly generated AES key. In addition, it encrypts the AES key with a public key inserted into the virus' executable file, and finally, saves them to .KEY. Data encryption routine of this malware is slightly less complicated: they are encrypted using an AES key encrypted with RSA cipher (unfortunately, we cannot say so about Spora ransomware removal).
According to the analysis, the virus currently targets only 23 file extensions:
.backup, .xlsx, .docx, .rtf, .dwg, .cdr, .cd, .mdb, .1cd, .odt, .pdf, .psd, .dbf, .doc, .sqlite, .accdb, .jpg, .jpeg, .tiff, .zip, .rar, .7z, .xls.
Files that have these extensions are secured using a long encryption key (the public key); meanwhile, the private key is sent to criminals remote servers and is kept there until the victim agrees to pay a ransom. Instructions on how to transfer the payment are provided in the ransom note which is usually saved on the desktop.
These instructions point the victim to a place that contains even more instructions – the official Spora ransom payment site which is sophisticated. Besides, currently, 10 different sites are used for collecting illegal ransoms, including spora[.]bz, spora[.]one, spora[.]hk, and others.
However, you should not analyze and use none of these payment sites after the attack. You should remove Spora ransomware from the PC immediately with the help of FortectIntego or another reliable malware removal program.
Spora’s activity increased in August 2017: three updates have emerged
Malware researchers spotted few new variants of Spora spreading in August. The first reports about ransomware updates appeared on August 4th.[4] The recent variant spreads as an obfuscated radF14DE.exe file.
It does not append any extension to the targeted files; however, it still corrupts them and demands to pay 90 dollars for data recovery. However, according to the ransom note, the size of the ransom will increase to 121 dollars if users do not pay in four days time.
The second ransomware update was reported on August 7th.[5] This variant spreads as an obfuscated PE/HTA bundle in ZIP archives that are attached to phishing emails. According to the latest data, ransomware runs from mshta.exe and cmd.exe files.
The third variant was reported on August 14th.[6] It aims at Russian computer users only. It spreads via malicious spam emails that include ZIP file. The archive includes pdf.wsf dropper that runs ransomware on the system. What is interesting, this version of Spora does not rename targeted files and does not append any extensions.
According to the ransom note, files are encrypted with RSA encryption, and in order to get back access to them, victims have to transfer 140 USD. If the payment is not made within 4 days, the size of the ransom increase to 189 USD.
Hackers give detailed instructions and surprise with a sophisticated Spora ransom payment site
Once Spora finishes its malicious activities, it drops a ransom note in each folder that has encrypted. The guidelines are written in Russian or/and English language. The name of the ransom note is created by using this scheme:
SPORA_< Sample ID >.hta
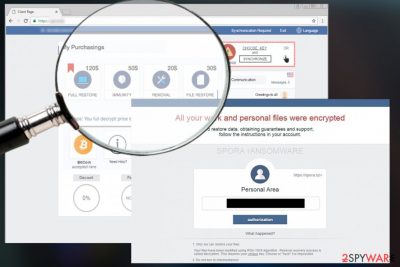
The payment site[7] differs from websites that typical ransomware viruses normally point to because it provides a variety of options for the victim:
- remove Spora virus for $20,
- restore files for $30,
- pay $50 for ostensible immunity to ransomware attacks;
- get a full restore package for $79.
Authors of the virus accept the payment in BitCoin currency[8] only. On January 16th, the payment website was improved, and a “Help” page was added. The site also has a public communication window, a table of transactions already made, and other little details that all make a very user-friendly interface[9].
No matter what, the malware is definitely not user-friendly as it wants to extort money[10] from the victim. In order to get the decryption key, victims are asked to pay the ransom and send the .KEY file to crooks via the payment site. If you have been hit by this virus, make sure you delete it immediately. It is highly advisable to use tools like FortectIntego or SpyHunter 5Combo Cleaner for successful Spora removal.
Spora 2.0 – the major update of the ransomware
oon after the original version of the virtual threat got unleashed, cyber villains introduced an updated variant of the malware – Spora 2.0 ransomware virus. The authors of this virtual menace launched a more crafty campaign to multiply their global infection rate[11].
EITest malicious code would redirect users to the website infected with an exploit kit. Shortly afterward, the web page would turn into a mosaic of miscellaneous source codes. Consequently, the notification “The HoeflerText font wasn't found” emerges.
In order to solve this inconvenience, the crooks offer to enable a special Chrome Font Pack. However, what users would download is not some fishy browser extension but a real virtual menace – Spora 2.0.
Interestingly, that the folder carrying infection are double-zipped. Now the crooks demand approximately 2000 USD in exchange for the files[12]. Despite the elaborate payment site, there are no reports whether the felons returned all files to their victims.
Crypto-malware spreads via malicious emails
Malspam is currently the main technique used to distribute Spora. In the beginning, when this threat was using Russian language only, misleading emails used such subject:
Скан-копия _ 10 января 2017г. Составлено и подписано главным бухгалтером. Экспорт из 1С.a01e743_рdf.hta.
In English that would be: “The copy of scan _ 10 Jan 2017. Written and signed by the chief accountant”.
However, this ransomware keeps changing, and it will definitely use different subject lines. You should be careful with emails and especially with their attachments because they might include infectious HTA files. These hideous files have double extensions, for example, PDF.HTA and the real extension is hidden so that the victim would think that .DOC is the real extension.
Let us remind you that HTA file is HTML executable file format, and so when the victim opens it, it downloads close.js JavaScript file to the system folder called %Temp%. Here, the infection activates itself by extracting an executable file and opening it. This executable file is the main file which is responsible for the data encryption procedure.
At the same time, HTA file opens a DOCX file, which shows an error message that says file cannot be opened. While the victim stares at this suspicious error, the ransomware encrypts all files on the system.
Spora removal guide
You can remove Spora virus quite easily using reliable anti-malware software. If you do not have one, we suggest installing FortectIntego or SpyHunter 5Combo Cleaner. If you want to use a different program, you can easily choose the one that you like after reading detailed software reviews in the Software section.
Please keep in mind that you are dealing with the virus of ransomware type, so it can try such things as blocking your anti-malware and antivirus programs when trying to remove it from the system.
If you are dealing with such problem right now, we recommend you to try rebooting your computer to a Safe Mode with Networking before launching anti-spyware software. If this option does not work, continue Spora removal with the help of System restore method.
Getting rid of Spora virus. Follow these steps
Manual removal using Safe Mode
Ransomware viruses are extremely hard to remove because they typically modify Windows Registry, clutter the system with malicious files and often drops additional malware. If your anti-malware program is blocked by Spora virus, perform the following steps and reboot your computer to Safe Mode with Networking before a scan. You should repeat it in normal mode once you finish the scanning process in Safe Mode.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Spora using System Restore
If rebooting to Safe Mode with Networking failed to work for you, you can try System Restore option to block the virus. Then, make sure you run a full system scan with anti-spyware software because system restore does not eliminate malicious files from your computer, it just blocks the ransomware.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Spora. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Spora from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.There are some data recovery methods that might help you to restore lost files. You can find descriptions of these methods below.
If your files are encrypted by Spora, you can use several methods to restore them:
Data Recovery Pro
Data Recovery Pro can help you to restore some of your lost files, so you should not miss the opportunity and try it:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Spora ransomware;
- Restore them.
Find lost data with ShadowExplorer
ShadowExplorer helps you to find previously saved file copies in case their latest versions get corrupted. Here's a quick tutorial on how to find the earlier versions of encrypted files:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Spora ransomware decrypter is not available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Spora and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ What is a Trojan Virus? - Definition. Kaspersky Lab US. Cyber Security Resource.
- ^ UsunWirusA. UsunWirusA. Polish website about recent cyber threats, their removal and prevention.
- ^ Gabriel E. Hall. Spora ransomware. Hur tar man bort? (Avinstallera guide). UtanVirus. Swedish website that provides malware removal tutorials.
- ^ Report on Spora update: August 4th. Twitter. The social network.
- ^ Report on Spora update: August 7th. Twitter. The social network.
- ^ Report on Spora update: August 14th. Twitter. The social network.
- ^ Jake Doe. Locky virus. How to Remove? (Uninstall Guide). 2-Spyware. Fighting against spyware.
- ^ Things you need to know. Bitcoin. The Internet of Money.
- ^ What is user interface. Webopedia: Online Tech Dictionary for IT Professionals.
- ^ Crypto-ransomware. F-Secure. News from the Lab.
- ^ Erwin Castro. New Google Chrome-Targeted Malware Uses New Clever Technique To Fool And Infect Users. University Herald. World News and Opinions.
- ^ Doug Olenick. Sage 2.0 ransomware now distributed along with Locky, Cerber. SC Media. The Cybersecurity Source.





















