Internet Protection (Virus Removal Guide) - Dec 2019 update
Internet Protection Removal Guide
What is Internet Protection?
Internet Protection is a fake security software that implements various scam messages to make users buy its licence
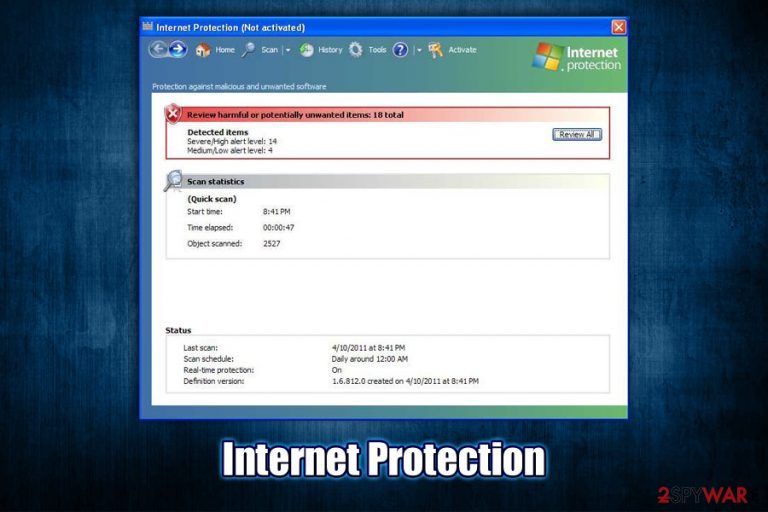
Internet Protection is a rogue anti-malware software that belongs to the scareware[1] category. In most cases, the application is accidentally installed from software bundles acquired from third-party websites, so users are usually unaware where it came from in the first place. In other cases, users might be tricked by fake updates that represent Flash Player.[2] As soon as the application gets installed, it immediately performs an alleged system scan, finding hundreds of Trojans, worms, spyware, and other types of malware. Of course, these findings are fake, and Internet Protection is a scam.
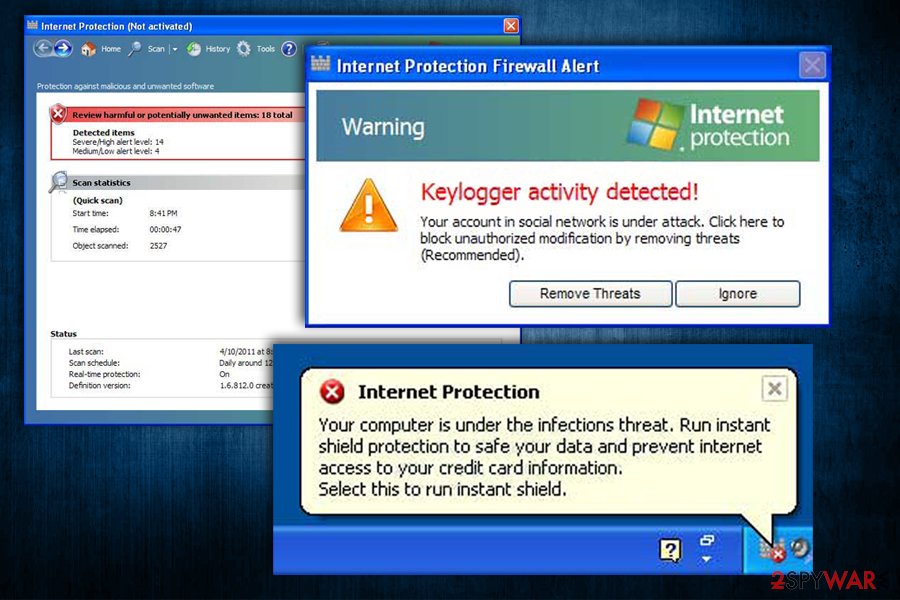
The main goal of Internet Protection developers is to make users believe that their machines are in grave danger due to malware infections. To make the scam more believable, the app uses similar colors and icons that resemble Microsoft Windows attributes. Until Internet Protection removal is performed, users will keep constantly spammed with notifications and pop-ups that claim malware infections and that they need to purchase a full version of the program in order to save their computers and sensitive information.
| Name | Internet Protection |
| Type | Rogue anti-spyware, scareware, malware |
| Infiltration | The virus is installed on the system along with other software from insecure third-party sites. Alternatively, users may get tricked by fake Flash Player updates or install it intentionally while being deceived about its true functionality |
| Symptoms | Numerous warnings and pop-ups that show fake security alerts and ask to purchase software licence to allegedly remove malware found on the device |
| Risks | Money loss, installation of other malware, MS Windows system compromise |
| Removal | In some cases, the malicious app may be difficult to remove manually. In such a case, access Safe Mode with Networking and perform a full system scan using reputable anti-malware like SpyHunter 5Combo Cleaner or Malwarebytes |
| Recovery & optimization | Just as many other programs of such type, Internet Protection alters the registry and some other vital Windows settings, which might result in system errors or crashes post-termination. To repair the damage done to the OS, we highly recommend using FortectIntego |
Internet Protection is a Trojan that aims to scam people and is just one of many “recycled” programs that use exact same methods for its operation. The malware family it belongs includes tools like System Security, Antivirus 2009, Security Defender, Security Tool, and many others.
Luckily, these malicious programs are dying off, and it would be rare to download them via Google Chrome, Mozilla Firefox, or another browser, as online scams now focus on not so obviously-malicious tools. Nevertheless, it does not mean that Internet Protection and all the other programs of such kind are completely gone, so it is important to keep an eye on such threats.
Calling Internet Protection a virus or malware is absolutely accurate, as the tool engages in malicious activities once it is installed on the host machine via deceptive ways. Because users are unaware where the app comes from, and it uses a legitimately-looking interface, they might believe that their systems are actually in danger. This is especially true for less experienced computer users.

Upon Windows boot, Internet Protection will automatically launch itself and perform fake scans, which will return hundreds of entries. Even when the program is not running, it will display one of the following security warning messages in pop-up windows:
Internet Protection Your system has come under attack of harmful software. Click here to deactivate it.
Internet Protection External software tries to control variety of your system files. This may lead to breaking of some data in your system. Click here to protect remote access to your PC & delete these programs.
Internet Protection Firewall Alert Warning Keylogger activity detected! Your account in social network is under attack. Click here to block unauthorized modification by removing threats (Recommended)
Suspicious activity in your registry system space was detected. Rogue malware detected in your system. Data leaks and system damage are possible. Please use a deep scan option.
Another reason to avoid rogue anti-spyware tools is its persistence. Quite often, users will not find the entry within the Control Panel or uninstallation might completely fail due to running background processes. Consequently, Internet Protection removal might become a real nightmare, especially to those who are unfamiliar with the techniques it uses.
To remove Internet Protection virus easily, you should simply employ reputable anti-malware and perform a full system scan. In case that does not work, you could also access Safe Mode with Networking, as explained below. Note that after you uninstall Internet Protection, you might suffer from Windows crashes and various errors. If that is the case, remediate your machine with PC repair software FortectIntego – it will remove the damage done by Internet Protection malware.
Be careful when browsing the internet or installing new programs
Rogue software can be found on various third-party websites, and some users actually opt for it when trying to find alternatives to legitimate tools. As a result, they risk infecting their machines with potentially unwanted programs, scareware, and even malware. Therefore, the first step to better computer security is to avoid visiting websites that host pirated programs,[3] as well as software cracks or keygens – these sites are never safe and should not be trusted.
Besides, torrent and warez sites do not adequately protect visitors and might be infused with malicious JavaScript, which would sometimes initiate an automatic malware installation procedure. Thus, when looking for software to install, rather than trust reliable websites that hold a good reputation – you can find website and application reviews everywhere on the internet. Also, during the installation process of new software, always opt for Advanced/Custom settings instead of recommended ones, as sometimes optional components might only be removed in such way.
Finally, beware of fake updates – the message usually pops up seemingly out of nowhere and claims that Java or Flash components are out of date. Never “update” software in such a way – either set up automatic updates for each of the installed apps or go to the official website and download them from there.
Get rid of Internet Protection malware from your machine
Internet Protection removal might sometimes not that easy of a process, considering that the virus can perform various changes on the infected system. For example, if the app has a background process running, or registry is set in a particular way, it automatically gains persistence. If that is the case, you can access Safe Mode with networking and remove Internet Protection without problems via Control Panel.
You can also get rid of the Internet Protection virus by scanning your machine with anti-malware software. Additionally, due to Windows registry modification, we highly advise you run a scan with FortectIntego, as it could restore all system files that might have been damaged due to the infection.
Getting rid of Internet Protection. Follow these steps
Manual removal using Safe Mode
Access Safe Mode with Networking and remove Internet Protection malware either manually or automatically.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Internet Protection and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting rogue antispyware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Scareware. Techopedia. Where IT and Business Meet.
- ^ Val S. Fake Adobe Flash Update Installs Ransomware, Performs Click Fraud. Symantec. Security blog.
- ^ Nicholas Godwin. The Dangers of Using Pirated Software and Why You Should Stop Right Now. Make Tech Easier. Computer Tutorials, Tips and Tricks.
