Buran ransomware (updated Nov 2019) - Bonus: Decryption Steps
Buran virus Removal Guide
What is Buran ransomware?
Buran cryptovirus is the ransomware-as-a-service developed by threat actors who offer discounts for criminal customers online
Unfortunately, this virus is evolving and has at least Buran and Buran 2 versions. Researchers cannot offer any decryption tool for the victims because the behavior indicates the continuity and possible improvements like new branding efforts in the future.
A file-encrypting malware form that appends an extension of numerous random letters and numbers can also encrypt data without marking them or changing the extension. Buran virus is capable of removing recovery points, clearing logs, and deleting backups. The first report about the threat reported that the added appendix looks like a GUID (Globally Unique Identifier),[3] and is added to each encrypted document. Moreover, most of the files are marked with an identifier “BURAN” which signifies the dangerous infection.
| Name | Buran |
|---|---|
| Malware type | Ransomware |
| Versions | Buran and Buran 2 that is in use currently |
| Extension | The file marker is formed with victim's unique ID and is placed one every file after encryption made them useless |
| Family | VegaLocker ransomware |
| Ransom note | !!! YOUR FILES ARE ENCRYPTED !!!.TXT |
| Contact emails | recovery_server@protonmail.com and recovery1server@cock.li, polssh1@protonmail.com, polssh@protonmail.com, sanio.marino@aol.com |
| Damage | The new versions called Buran 2 can delete shadow volume copies, backup catalog, system state backups, and repeats those processes to ensure the file deletion. Additional changes and these facts make the file recovery even more difficult |
| Distribution | Email spam and malicious script injected document attachments are commonly used by ransomware developers, but this threat is known to mainly rely on Rig Exploit Kit as a vector for distribution. Many attacks also got successful due to the exploit of a common CVE-2018-8174 vulnerability |
| Identification | Use anti-malware tools to remove Buran ransomware and make sure to fix virus damage, corrupted files using FortectIntego as it can run a scan on your Windows machine |
After the data is blocked, a ransom message named !!! YOUR FILES ARE ENCRYPTED !!!.TXT[4] is loaded onto the desktop in order to inform the victims about what just had happened. The criminals urge contact via recovery_server@protonmail.com and recovery1server@cock.li email addresses that can also differ from version to version since this is a product used by many different criminals. In order to discuss all conditions about data restoring, the crooks demand users send their ID's to both emails and also provide them with an offer of free decryption of from three to five data files that take up no more space than 10 MB.
Buran ransomware is a dangerous threat that no one wants to see on their machines. However, if the cyber threat has already occupied your system, you should be prepared for all possible consequences. Note that, the criminals are capable of modifying various registries entries and tasks by activating remote commands.
This might also allow Buran ransomware to inject other malware straight into the system and cause severe damage to it. If a Trojan horse[5] ends up on your computer, you might find the entire system struggling to carry out even simple actions and launch programs. Moreover, trojans can relate to personal data and identity theft.
If you decide to contact the crooks, they will supposedly offer you a decryption tool for a particular price in order to bring back files that have been locked by Buran ransomware. Such people usually urge for Bitcoin[6] or another type of cryptocurrency which allows the process to remain safe and untrackable by others.
Buran ransomware message placed in text file reads the following:
!!! YOUR FILES ARE ENCRYPTED !!!
All your files, documents, photos, databases and other important
files are encrypted.You are not able to decrypt it by yourself! The only method
of recovering files is to purchase an unique private key.
Only we can give you this key and only we can recover your files.To be sure we have the decryptor and it works you can send an
email polssh1@protonmail.com and decrypt one file for free. But this
file should be of not valuable!Do you really want to restore your files?
Write to email polssh1@protonmail.com, polssh@protonmail.com
Attention!
* Do not rename encrypted files.
* Do not try to decrypt your data using third party software,
it may cause permanent data loss.
* Decryption of your files with the help of third parties may
cause increased price (they add their fee to our) or you can
become a victim of a scam.
We recommend denying any offers for ransom payments as this might be a scam. You risk losing money are being left by nothing. Rather than contacting these people and wasting your money and time, we recommend performing the Buran ransomware removal from the entire computer system and cleaning all infected directories. 
VegaLocker ransomware version Buran 2 advertised as a RaaS
In October 2019 ransomware campaigns got discovered that financially motivated threat actors delivered ransomware to organizations in Germany and other countries. These high volume attacks targeted companies via employees in the organization and relying on typical demanding messages attempt to make money from them. Improved and crafted malware designed to suit a wide range of environments and infection vectors, so the target was not a specific network.
It is believed that Buran ransomware tends to focus on victims in certain regions, hence the certain language in ransom messages and recent campaigns affecting German companies. Since it was discovered as a version of VegaLocker, Buran was noticed being sold on various Russian hacker underground forums. Using the affiliated scheme and offering criminals the discount for 25 instead of common 30 or 40 percent cut out of the ransom payments.
Buran creators focus on creating relationships with criminals and negotiate business schemes. The following message was discovered in Russian underground forums:
Buran is a stable offline cryptoclocker, with flexible functionality and support 24/7.
Functional:
Reliable cryptographic algorithm using global and session keys + random file keys;
Scan all local drives and all available network paths;
High speed: a separate stream works for each disk and network path;
Skipping Windows system directories and browser directories;
Decryptor generation based on an encrypted file;
Correct work on all OSs from Windows XP, Server 2003 to the latest;
The locker has no dependencies, does not use third-party libraries, only mathematics and vinapi;The completion of some processes to free open files (optional, negotiated);
The ability to encrypt files without changing extensions (optional);
Removing recovery points + cleaning logs on a dedicated server (optional);
Standard options: tapping, startup, self-deletion (optional);
Installed protection against launch in the CIS segment.Conditions:
They are negotiated individually for each advert depending on volumes and material.
Start earning with us!
The message created to promote Buran as a threat compatible with many versions of Windows OS and working for targets from various countries. However, former Soviet Republicks like Armenia, Belarus, Moldova, Russia, Ukraine, and other countries cannot get infected by the Buran 2 ransomware.
This is because of an additional location checking module, which ensures that data encryption in certain countries is not launched. Many facts about the threat remain the same as those characteristics reported back in May, so ransom note will be written to disk with the name “!!! YOUR FILES ARE ENCRYPTED !!!” and each file gets renamed with the new extensions with random values and victims' ID as an appendix.
As experts report, the Buran virus represents the evolution of the ransomware and the primary VegaLocker ransomware had a history of infections targeting companies. Developers are clearly working behind it and developing new features as branding tactics, so profits can generate from malicious actions. Interm of development, new versions with different features got discovered only months apart, so there is an expectation for more variants from these authors. 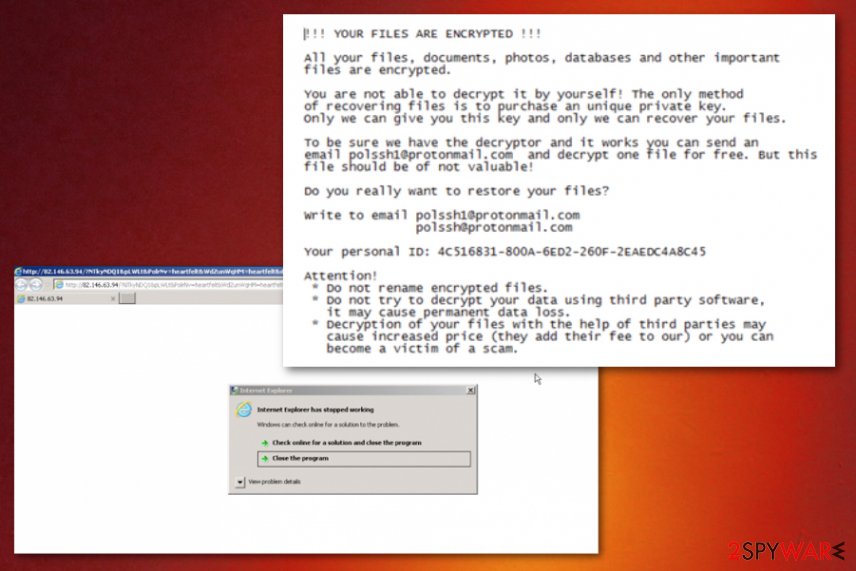
Rig Exploit kit and system vulnerabilities used to spread malware
Recent investigations on newer samples revealed that this ransomware was delivered through the Rig Exploit Kit that is popular among other ransomware developers. This exploit kit also uses Microsoft Internet Explorer VBScript engine, arbitrary code execution vulnerability CVE-2018-8174, to exploit the client-side and deliver malware on the system directly.
According to cybersecurity researchers from LosVirus.es[7] website, spam messages alongside pirated software packages are more often used for carrying a malicious payload. Ransomware-related infections are often spread via email spam and infiltrate users' computers by using stealth techniques. Usually, crooks pretend to be from reputable organizations and urge people to open the attached file for further important information regarding the received email letter.
We urge all users to be very careful while sorting out their email messages. If some letters have fallen straight to the spam section, better get rid of them without even opening as no reliable companies will waste your time by contacting like you in these types of ways. Furthermore, DO NOT open any attached files without scanning them with antimalware if you are not sure that they are safe to download.
Staying cautious on the Internet sphere and avoiding possible risks of malware infection is very important. The more serious you are with your online and computer safety, the better your chances will be for having a clean, optimized, and undamaged computer system. If you want to ensure that reputable protection does not fail you at any time of the day, you should get a strong and reliable antimalware program for this.
Automatical removal guidelines for Buran ransomware virus
First, we want to warn you that you should no try removing Buran ransomware virus on your own. By completing manual actions, you might bring more harm to your computer system, which can, later on, relate in severe machine and software damage. What you have do is reboot the PC with Safe Mode or System Restore to disable ongoing malicious activities.
Talking about the Buran ransomware removal process, we recommend performing it only with reputable antivirus or antimalware programs. However, you need to check the entire system for malicious executables and other content before getting rid of the cyber threat. You can complete such a goal with tools such as FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes since these applications may indicate damaged data and fix the issue.
After you remove Buran ransomware, you can start thinking about file recovery. We have provided you with some techniques that are informatively described at the bottom of this article. Just note that the ransomware elimination comes first before data recovery as if the malicious payload is still active, files will be encrypted again.
Getting rid of Buran virus. Follow these steps
Manual removal using Safe Mode
Activate the Safe Mode with Networking function on your Windows computer. Use the following guide to achieve this goal and prevent malicious activities from spreading further:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Buran using System Restore
Use the System Restore feature to stop Buran ransomware. If you do not know how to activate this function, take a look at these instructing steps:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Buran. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Buran from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Spotting encrypted files is definitely not the most pleasant view to see. However, do not panic and rush to contact the crooks as other ways might be more helpful for data recovery. What you have to do is take a look at the following file restoring techniques and complete each step carefully to reach the best results possible.
If your files are encrypted by Buran, you can use several methods to restore them:
Use Data Recovery Pro for file recovery:
If Buran ransomware has done some cruel work on your files and you are wondering how to return them back without paying the criminals, we suggest trying this software.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Buran ransomware;
- Restore them.
Windows Previous Versions feature is suitable for data restoring:
Restoring encrypted files is a difficult process. However, you might still have a chance of returning some of your documents to their previous states. Continue with this method if you have enabled System Restore in the past:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer might allow you to return some files back:
If the ransomware virus did not eliminate Shadow Volume Copies of your encrypted data, you should give this method a try, and you might recover some of your locked documents/files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Sadly, no official Buran ransomware decryptor has been released yet. Cybersecurity experts are currently working on its development.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Buran and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Doug Olenick. Buran ransomware detailed, found to be based on VegaLocker. Scmagazine. Security news.
- ^ Alexandre Mundo and Marc Rivero Lopez. Buran Ransomware; the Evolution of VegaLocker. McAffe. Securing tomorrow. Today.
- ^ Margaret Rouse. GUID (global unique identifier). Search Security. Tech Target.
- ^ DEMONSLAY335. !!! YOUR FILES ARE ENCRYPTED !!!.TXT. Pastebin.com. Relevant details.
- ^ Trojan. Malwarebytes. Computer technology page.
- ^ What is Bitcoin?. Coin Desk. Information source.
- ^ Losvirus. Losvirus. Spyware related news.





















