VegaLocker ransomware (Quick Decryption Solution) - Improved Instructions
VegaLocker virus Removal Guide
What is VegaLocker ransomware?
VegaLocker ransomware is a dangerous computer virus which does not add any extensions to locked files

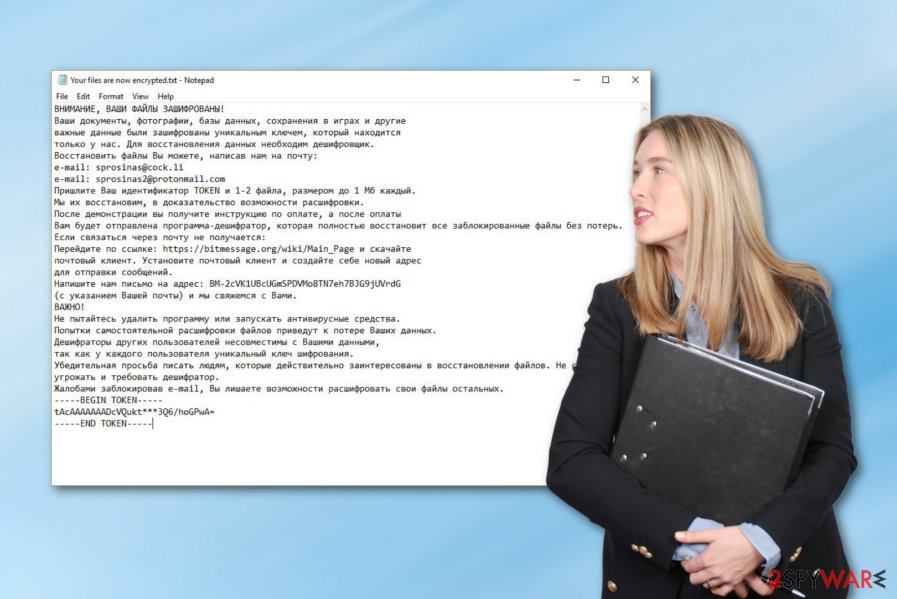
VegaLocker ransomware is a cryptovirus which performs the encryption[1] after successful infiltration. However, this cyber threat has one big difference from other of its kind – it does not apply any appendix or rename any encrypted files or documents. Of course, it does provide a ransom message which is named “Your files are now encrypted.txt” or “ABOUT YOUR FILES.txt”. We can guess that cybercriminals target Russians or Russian-speaking users as the note is written in the Russian language. The crooks demand some money which needs to be transferred in Bitcoin and provide email addresses such as sprosinas@cock.li, sprosinas2@protonmail.com, or sup24@keemail.me, sub24@protonmail.ch.
| Name | VegaLocker |
|---|---|
| Category | Ransomware |
| Appendix | No appendix is added to locked files |
| Ransom message(s) | “Your files are now encrypted.txt” or “ABOUT YOUR FILES.txt” |
| Encryption keys | Such as AES, RSA, SHA, etc. |
| Target | Russian people or Russian speakers |
| Emails | sprosinas@cock.li, sprosinas2@protonmail.com, or sup24@keemail.me, sub24@protonmail.ch |
| Detection | You can try using FortectIntego for detecting malware-related objects |
There is a big possibility that, once you are infected with VegaLocker virus, you will find rogue entries injected in the Windows Registry section or suspicious-looking processes running in the computer system. One of the odd components will be the ransom message which usually looks like this:
ВНИМАНИЕ, ВАШИ ФАЙЛЫ ЗАШИФРОВАНЫ!
Ваши документы, фотографии, базы данных, сохранения в играх и другие
важные данные были зашифрованы уникальным ключем, который находится
только у нас. Для восстановления данных необходим дешифровщик.
Восстановить файлы Вы можете, написав нам на почту:
e-mail: sprosinas@cock.li
e-mail: sprosinas2@protonmail.com
Пришлите Ваш идентификатор TOKEN и 1-2 файла, размером до 1 Мб каждый.
Мы их восстановим, в доказательство возможности расшифровки.
После демонстрации вы получите инструкцию по оплате, а после оплаты
Вам будет отправлена программа-дешифратор, которая полностью восстановит все заблокированные файлы без потерь.
Если связаться через почту не получается:
Перейдите по ссылке: https://bitmessage.org/wiki/Main_Page и скачайте
почтовый клиент. Установите почтовый клиент и создайте себе новый адрес
для отправки сообщений.
Напишите нам письмо на адрес: BM-2cVK1UBcUGmSPDVMo8TN7eh7BJG9jUVrdG
(с указанием Вашей почты) и мы свяжемся с Вами.
ВАЖНО!
Victims are given three days to show contact, otherwise, they are threatened that files will be permanently lost. Even though crooks use hardly-identifiable encryption algorithms, this does not mean that you have to rush and pay the VegaLocker ransomware cybercriminals. A particular amount of money is not demanded this time but matters are urged to be discussed via email letters.
Instead of paying the crooks, we suggest performing the VegaLocker ransomware removal by using anti-malware programs. Additionally, we offer to install a tool such as FortectIntego or SpyHunter 5Combo Cleaner to detect all malicious files, entries, and other virus-related components that might be safely hidden in the computer system by the ransomware virus infection.
Another important reason to get rid of VegaLocker ransomware on time is the virus's ability to make the system vulnerable to other infections. Each malware causes security flaws and might allow other threats to sneak into the system. Additionally, some cryptoviruses are capable of deleting Shadow Volume Copies which means that if you do not hurry up and terminate the virus ASAP, you might not be able to restore your encrypted data.
You cannot remove VegaLocker ransomware by yourself as this process requires a lot of practice and some actions can be performed only by reputable anti-malware. Remember to be careful next time and continue reading about ransomware avoiding tips and how to keep your important data protected from unwanted exposure or encryption.
Recently, the developers of VegaLocker ransomware have released another very similar version of this notorious file-locking cyber threat. It uses the ABOUT YOUR FILES.txt ransom message to inform users about the secret encryption process. This virus still seems to be targeting Russian speakers as the note is written in the Russian language. Crooks provide two email addresses in the text message: sup24@keemail.me and sup24@protonmail.ch.
For further information, it is known that the latest version of VegaLocker ransomware uses a mixture of SHA and RSA encryption algorithms in order to lock up files on the targeted machine. Additionally, once installed, the dangerous file-locking virus places the blanki(скореевсего образец вируса).exe file in the infected computer system from which the hazardous payload might be identified. The ransomware is detected as Win32:Malware-gen by Avast and AVG antivirus programs.
Ransomware can spread through malicious email attachments
According to computer specialists from Virusai.lt,[2] ransomware viruses are most commonly spread via malicious email messages and their attached executables or infected links that come injected inside the message itself. We urge all users to be careful while opening received email and deleting all letters that they are not sure about and look suspicious.
Another popular ransomware distribution source can be various third-party pages which are created for downloading software, films, and various applications for free. Peer-to-peer networks[3] are promoted by secondary sources and often lack protection. This vulnerability allows criminals to inject malware into unprotected hyperlinks or even software packages.
For further protection, you should always be careful while visiting websites on the Internet, downloading particular software, and so on. However, our specialists also offer to download and install a reputable computer security program for safety purposes. In some cases, the human eye might not catch all hazardous content, so, this can be done by antivirus tools.
VegaLocker ransomware should be terminated ASAP after detection
If your antivirus tool has detected the ransomware infection, you need to remove VegaLocker virus fast. If you do not have an anti-malware tool[4] which will allow you to find all virus-related components on your system, we suggest considering to download and install an expert-tested program such as FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes.
After the VegaLocker ransomware removal, make sure that you reboot the entire computer system. For data recovery steps, look below this text. Moreover, be prepared for the future – gather all important data and store it on remote servers or devices where no one, except you, will be able to reach it.
Getting rid of VegaLocker virus. Follow these steps
Manual removal using Safe Mode
Use Safe Mode with Networking to disable the ransomware infection and its hazardous activities:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove VegaLocker using System Restore
Enable the System Restore feature to deactivate the cyber threat:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of VegaLocker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove VegaLocker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.We have provided some methods below which should help you get some of your files back.
If your files are encrypted by VegaLocker, you can use several methods to restore them:
Using Data Recovery Pro might allow you to restore some data:
Try this method and you might succeed in data recovery.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by VegaLocker ransomware;
- Restore them.
Windows Previous Versions feature can be helpful with file restoring:
If you want to recover some of your files that were blocked by VegaLocker ransomware, you can try performing data recovery with this tool.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer is a tool which might help with data recovery purposes:
Give this method a try if the virus did not damage or permanently erase Shadow Volume Copies of locked documents.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official VegaLocker decryptor has been discovered yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from VegaLocker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Encryption. Techopedia. Tech terms and definitions.
- ^ Virusai.lt. Virusai. Computer information and malware prevention tips.
- ^ James Cope. What's a Peer-to-Peer (P2P) Network?. Computer world. From IDG.
- ^ Margaret Rouse. Antimalware (anti-malware). Search Security. Tech Target.





















