Trojan:JS/Cryxos (Virus Removal Guide) - Tech Support Scam
Trojan:JS/Cryxos Removal Guide
What is Trojan:JS/Cryxos?
Trojan:JS/Cryxos is the threat that delivers notification messages about computers' or web browsers' issues that the virus triggered
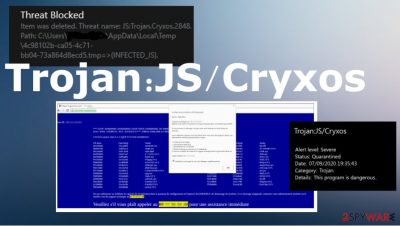
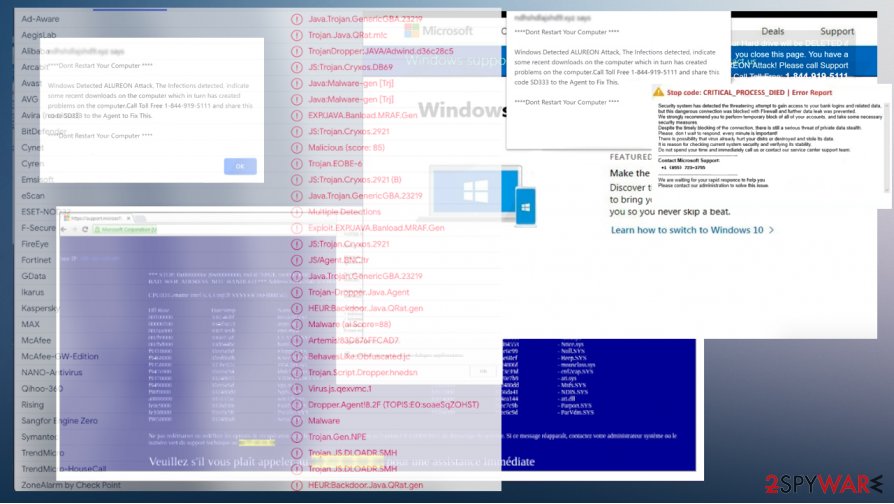
This infection typically can be triggered after opening a malicious site with a dangerous JavaScript or when downloading the file from an insecure email notification. Trojan:JS/Cryxos virus shows notifications to trick people into thinking that their device is infected and that there are some risks or even serious damage the reported virus can cause. This infection is reported by various sources[1] because AV tools detect[2] the intruder that aims to make a profit for the creators. The machine is not compromised even though alerts and warnings state so.
Calling the given phone number can lead to serious infections and hard-to-remove malware infiltrations. Remember that Apple, Microsoft, and other software developers DO NOT send such messages and system alerts to your web browser or desktop in general. None of them offer help via a particular phone number. This fact should encourage you to question such messages like Trojan:JS/Cryxos alerts that are not legitimate or related to any serious security risks.
| Name | Trojan:JS/Cryxos |
|---|---|
| Type | Technical support scam,[3] spamming tool |
| Issues | The social engineering campaign that relies on false claims about virus detections and computer issues. These notifications and alerts offer to contact technicians on the other side of the provided phone number |
| Danger | Contacting these alleged technical support team members might lead to fake computer program promotions, direct money loss, or malware infiltration |
| Fake technical support phone numbers | +1-800-330-7028, +1-855-723-3755, +1-800-278-6064, +1-833-272-0272, +1-844-919-5111 |
| Distribution | Compromised websites, rogue programs, advertisements, and unwanted applications can trigger the infection that shows fake error messages and system warnings |
| Elimination | You can remove Trojan:JS/Cryxos and other intruders by running the anti-malware tools or reliable security programs that can help you with serious infections |
| Repair | The infection can trigger issues with the system when certain files get added or altered. Such damage may disrupt the performance of the computer, so run FortectIntego to see if any problems can get fixed |
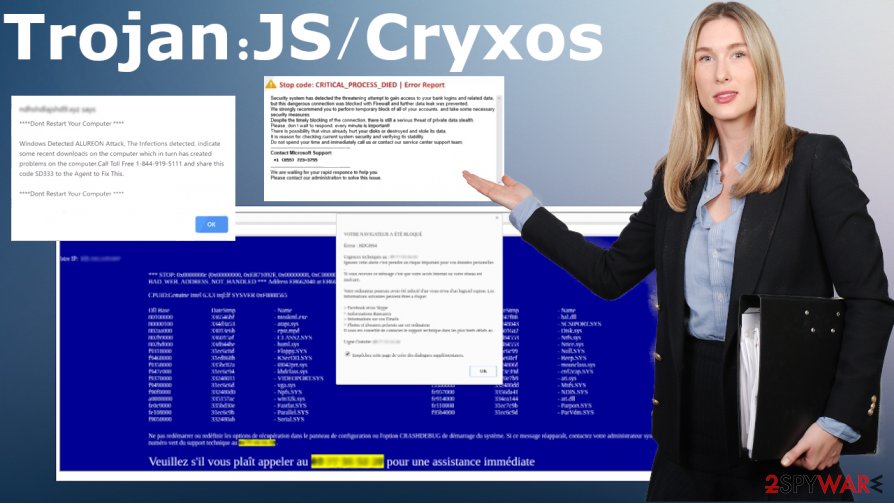
Trojan:JS/Cryxos messages might vary in languages because some variants open the web browser page that displayed an alert resembling the legitimate Microfost message to enhance the impression about the legitimacy of this alert. Many versions of the fake alert can surface the desktop of yours.
It is not surprising because Trojan:JS/Cryxos creators aim to achieve their goals no matter what. The main indication that such messages are false – phone numbers and encouragements to contact people directly. Legitimate vendors do not do that. Real alerts from the system do not come with contact information or suggestions to remove the infection.
A possible version of a fake error message that Cryxos trojan shows on the screen:
Windows Security
Microsoft Edge
The server ****** is asking for your user name and password.That server also reports:
“__________
System_Protect_-_PROTECT_ERROR_0xEB6468728
Contact_Microsoft_Support__+1_(855)_723-3755_Toll-Free.”
You may see the resemblance with other tech support scams, a direct scam that relies on using Microsoft name or report about a particular trojan. Trojan:JS/Cryxos is similar to Windows Defender Alert: Zeus Virus, Microsoft Warning Alert, “Microsoft has detected suspicious activity”, and many other scammy messages. These programs can create issues with the system and trigger damage in the functions, so rely on FortectIntego or similar program to repair these issues.
Fortunately, some tools can help you to remove Trojan:JS/Cryxos from the machine and check for the infection that those reports warn about. Based on the file's detection rate from a malicious email that created these issues, you can easily find a tool that finds and terminated the threat.
Of course, the detection name for the Cryxos trojan depends on the database that the selected AV detection tool uses. So you should run a program like SpyHunter 5Combo Cleaner or Malwarebytes to find threats, infections, other security risks. After the system cleaning, such messages should end.
Trojan Cryxos can lead to more serious issues with the machine if you decide to call the provided number or write the email, contact these criminals in other ways. The alleged further assistance that scammers promise can be a conversation with malicious people that aim to receive payments from you directly, so they give the information for you or even rely on remote access tools that can stop malware too. Avoid clicking on such messages and do not contact malicious people.
The malicious email in such a campaign can lead to serious malware infection
Spam emails often get used for spreading infections like this. It is common because malware creators aim to distribute products widely and quickly. Email notifications trick people into opening the attached file that contains malicious macro viruses or script running the installation directly on the machine.
You can avoid such alerts legitimacy of notifications from unknown senders and pay close attention to files that you open on the machine directly. There are many issues that such malicious emails can trigger. You need to take the fact that many actors aim to land their programs on your system by showing false messages about invoices and order details.
The malicious email can be named as an order confirmation email or the alert about other information. Check the sender and source of the information before you open the email and download the file. Some AV vendors offer to scan the document before downloading that.
Terminate any programs and processes related to the Trojan Cryxos virus or other scams
The Trojan:JS/Cryxos virus can run various processes in the system and trigger changes on the computer to trigger more issues with the performance, so those claims about risks and blocked access seem more believable. There are many aims that these actors have, so your device can get affected significantly without you understanding what happened.
Trojan:JS/Cryxos removal gets difficult due to those alterations and damage in the system. You can receive help from automatic tools like SpyHunter 5Combo Cleaner or Malwarebytes and go even further to use the System Restore feature that allows the recovering machine to a previous state.
If you managed to remove Trojan:JS/Cryxos, you should always double-check still. Running another anti-malware tool or security program and checking for problems with security can improve the performance further. Also, tools like FortectIntego check for file corruption, alterations in the system, and program performance.
Getting rid of Trojan:JS/Cryxos. Follow these steps
Manual removal using Safe Mode
You can reboot the machine in Safe Mode with networking and then run the anti-malware tool for cleaning the machine properly
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Trojan:JS/Cryxos using System Restore
Remove Trojan:JS/Cryxos by using System Restore feature
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Trojan:JS/Cryxos. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Trojan:JS/Cryxos and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting spam tools
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Trojan:JS/Cryxos. Microsoft. Security intelligence report.
- ^ Detection rate. VirusTotal. Online malware scanner.
- ^ Technical support scam. Wikipedia. The free encyclopedia.





















