Hoop file virus (Recovery Instructions Included) - Bonus: Decryption Steps
Hoop file virus Removal Guide
What is Hoop file virus?
Hoop is an infection that can prove to be detrimental if you don't take the right precautions
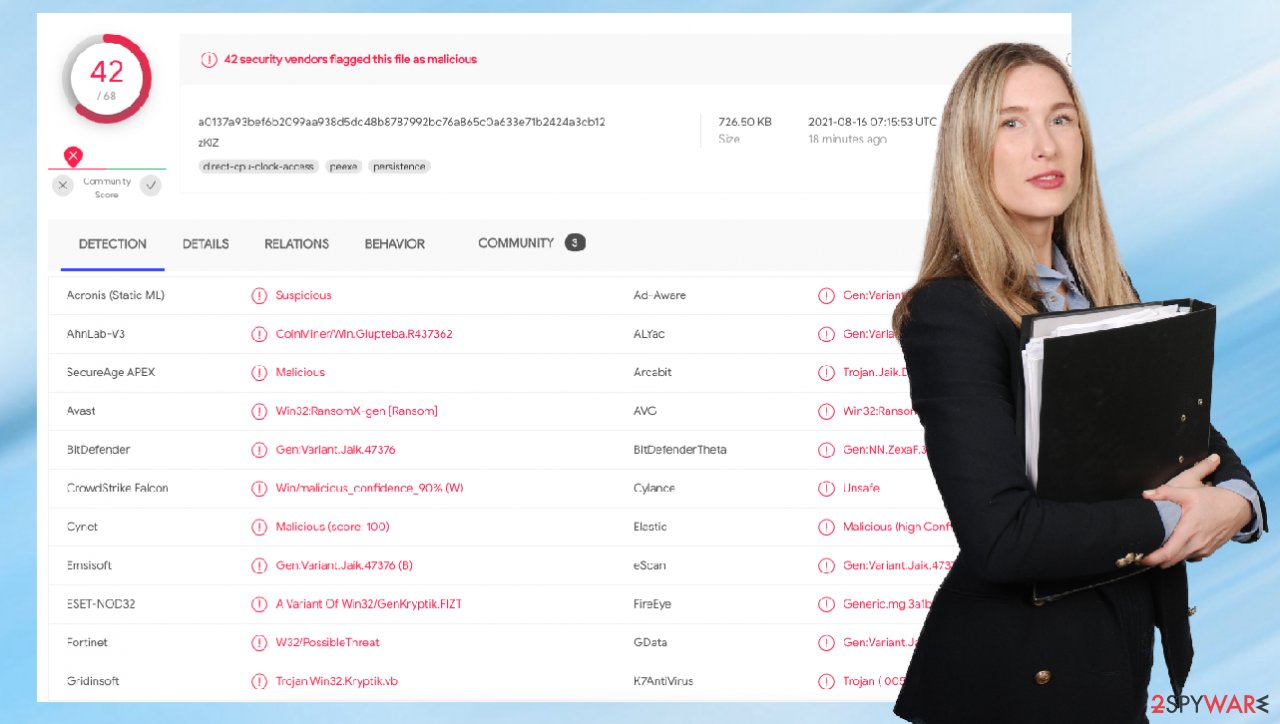
Hoop virus and any other malware that falls in this ransomware category may install itself onto your Windows computer as soon as a malicious executable file downloaded from torrent and crack websites, for example, are executed. Immediately after infiltration, system configuration changes, and the data encryption process begins. This file-locking process typically includes showing fake pop-up windows in order to stop victims from interrupting it by turning off their PC or laptop during the locking of videos and documents with the RSA or AES algorithm.[1] The particular version of the Djvu family tends to fake Windows update or a different process, so users do not interrupt the activity, thinking this is important for the machine.
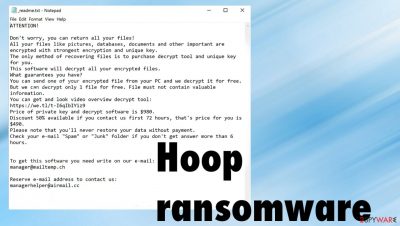
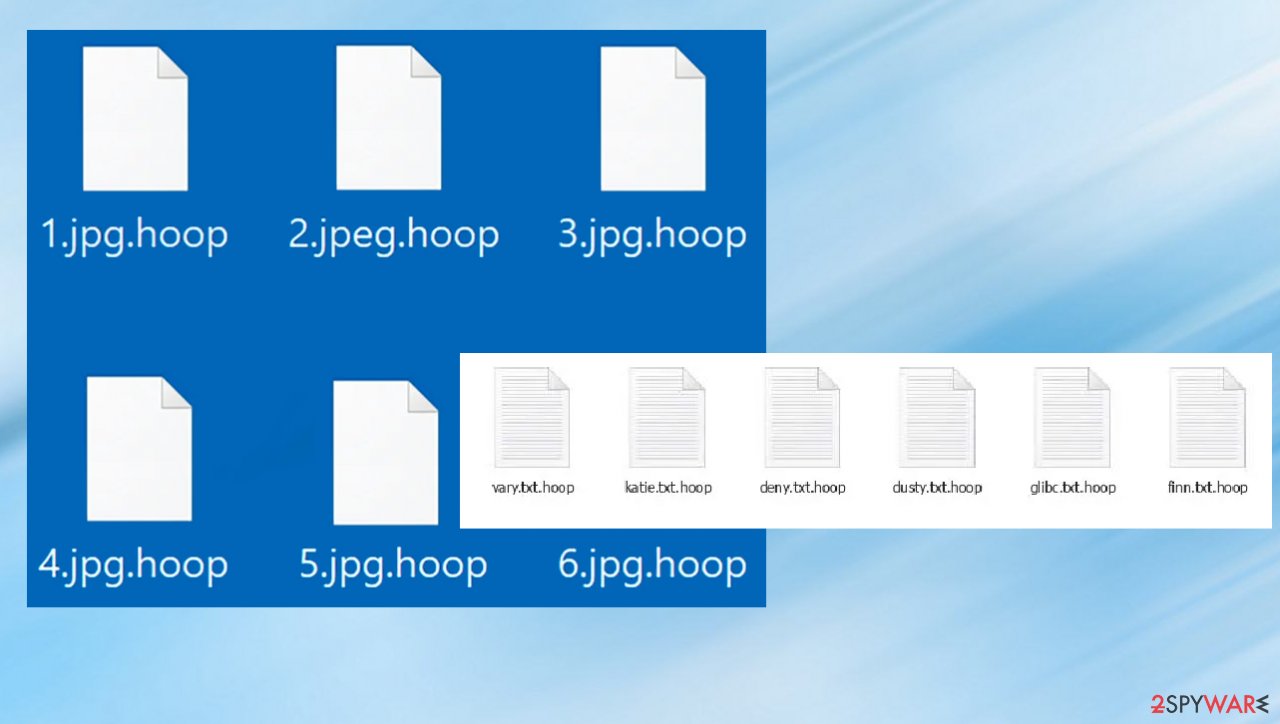
Ransomware is monetized by getting paid for a decryption tool – it encrypts files so that victims could not access them without a decryption tool purchased from the attackers. This feature allows criminals to fake legitimacy and makes people more eager to pay up. Hoop ransomware appends the .hoop extension to their filenames and generates a _readme.txt ransom note that provides contact and payment information about how you can recover your data if you are infected with the virus. That shouldn't be considered an option.
Typical behavior of this virus family is not changed for a while, so the ransom note file is named like this and contains the same text inside for years. The only different thing about these new versions – file appendix, contact emails. Those can be easily changed, but contact information also often gets repeated. Developers of the threat manage to release new versions weekly, and the latest ones include Muuq, Nooa, Reqg.
| Name | Hoop ransomware |
|---|---|
| Type | Cryptovirus, file locker |
| Danger | High level of danger because the infection involves money extortion |
| Family | Djvu/STOP ransomware |
| File marker | .hoop |
| Distribution | Software and game cracks, infected file attachments from emails, various other files found on torrents[2] |
| Ransom note | _readme.txt |
| Data recovery | Is possible for some of the versions when offline IDs get used in the encoding. Another option would be a media file restoring tool or third party data recovery applications (listed below) |
| Elimination | The most important is the virus termination. You shouldn't do anything else until the infection is removed. File restoring can happen once the virus is deactivated |
| System recovery | Your device can be affected significantly because the virus damages pieces in system folders. FortectIntego can find affected data and help solve the related problems |
The data locking virus delivers a ransom note titled that includes all the information required for users to understand the demands of cybercriminals. The hackers offer victims an opportunity to pay $980 in Bitcoin. It is possible to get a discount of 50% within the first 72 hours instead of paying full price.
When the user wants to make contact with cybercriminals, it is possible to reach them via email. If the victim does so, then criminals can look for a needed decryption tool and send that after the money transfer. This happens rarely, so make sure to remove the Hoop infection instead of paying. We will answer all the questions for you.
Should you follow the ransom note instructions?
The ransom note includes detailed instructions on how to pay after someone managed to create a Bitcoin wallet. This appears to be done by hackers to monitor whether their target is sincere about paying the ransom. The full ransom note also hints that cybercriminals may provide their victims with decryption software, so the payment ensures that files get recovered.
They can even go as far as to show them how to use it to decrypt files on the infected machine. This means that they do not plan on deleting victims' files after receiving money for them. That is only for creating trust. It is much easier and more profitable for hackers to continue extorting money from users who feel extremely anxious about their important data, so contacting them can end in money and data loss. DO NOT PAY for the Hoop virus creators. Researhcers[3] only advise against it.
The particular family of ransomware has an option of decryption because of the changes in encryption
If you have infected your computer with one of the Djvu variants, you should try using Emsisoft decryptor for Djvu/STOP. It is important to mention that this tool will not work for everyone – it only works if data was locked with an offline ID due to malware failing to communicate with its remote servers.
Even if your case meets this condition, somebody from the victims has to pay criminals, retrieve an offline key, and then share it with security researchers at Emsisoft. As a result, you might not be able to restore the encrypted files immediately. Thus, if the decryptor says your data was locked with an offline ID but cannot be recovered currently, you should try later. You also need to upload a set of files – one encrypted and a healthy one to the company's servers before you proceed.
- Download the app from the official Emsisoft website.
- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.
![Hoop file virus Hoop file virus]()
- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although by pressing Add folder at the bottom, you can also do it.
![Hoop file virus Hoop file virus]()
- Press Decrypt.
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt a file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID; decryption is impossible” – you are unable to decrypt files with this tool.
Is it possible to remove the infection?
Even the discount offers and test decryption claims shouldn't encourage you to pay for the criminals. Hoop is a sophisticated threat, so many changes on the machine can ensure persistence. The sooner you get rid of it, the better. Anti-malware tools are created for this purpose, so choosing the AV application is the best solution.
The attackers do not care about your files, so the virus can be set to delete any backup of the data to make it impossible to get your files back. They also generate other processes that affect the machine significantly. You need to deal with this situation yourself, but there are helpful tools that find the malware. Based on the detection, you can choose the app you would trust or rely on SpyHunter 5Combo Cleaner or Malwarebytes that we recommend.
Allowing the tool to remove all pieces of malware can disable Hoop and its processes, so anything malicious cannot be loaded and launched. Then, your files can be recovered properly, and there is no danger of getting files encrypted again. If you load backups or copies of files on the machine where the threat is still active, you can suffer from double encryption and permanent data loss.
The answer strongly depends on your personal circumstances and is different for every individual! For example, if you have previously prepared backups, all that needs to be done is remove malware from the system. Then you can load backups of files and replace affected pieces. Make sure security software has been updated before scanning it, so nothing slips through the cracks.
File recovery options for .Hoop encoded data
Since many users do not prepare proper data backups before being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool. Another option is data recovery tools. However, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.
- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
When Hoop ransomware is active on a device, the system can become damaged significantly in addition to direct file encoding. The damage includes major OS malfunctions that will lead to your computer breaking down and not working at all.
If you don't take care of this virus, then it could very well destroy any data stored within the infected PC's memory space or even delete an entire drive. There are no other options for cleaning up malware; if you put restored files back onto a contaminated machine – there isn't much hope left because once one infection has been found, chances are high others lurk nearby.
Be sure to eliminate every bit of unwanted code from your precious hard disk before trying again to restore important pieces. But also remember about system issues caused by the infection. Once you eliminate the ransomware and all the Hoop pieces, repair the machine fully.
We highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it can also remove malware that has already broken into the system thanks to several engines used by the program. Besides, the application can also fix various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
Do not ignore these important steps, and make sure to rely on helpful tools. Everyday users rarely are capable of fixing these issues created by the cryptovirus infection, so it is important to learn about the infection you are dealing with and take the needed steps to fight it. Encryption is a serious issue, but your computer can become useless if you do not remove the infection.
Some virus changes keep you from running tools like SpyHunter 5Combo Cleaner or Malwarebytes, so you might want to use additional help like Safe Mode. The following instructions can help enter the safe environment and run the AV tool, so the machine can get cleaned and your files later on – restored properly. Double-check before adding safe files to your computer.
Getting rid of Hoop file virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Hoop file and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Yimi Hu. A brief summary of encryption method used in widespread ransomware. Infosecurity. Cryptography resource.
- ^ 4 risks of using torrents. Startupsgeek. IT insights and tips.
- ^ Senzavirus. Senzavirus. Security news and virus removal guides.























