Reqg ransomware (Decryption Steps Included)
Reqg virus Removal Guide
What is Reqg ransomware?
Reqg ransomware infects your computer to extort money from you
Reqg is a ransomware-type infection that can prove to be detrimental to your personal files that reside on a Windows computer. Malware is typically installed as soon as a malicious .exe file downloaded from torrent, crack, and similar websites are executed; immediately after infiltration, system configuration changes, and the file encryption process begins.
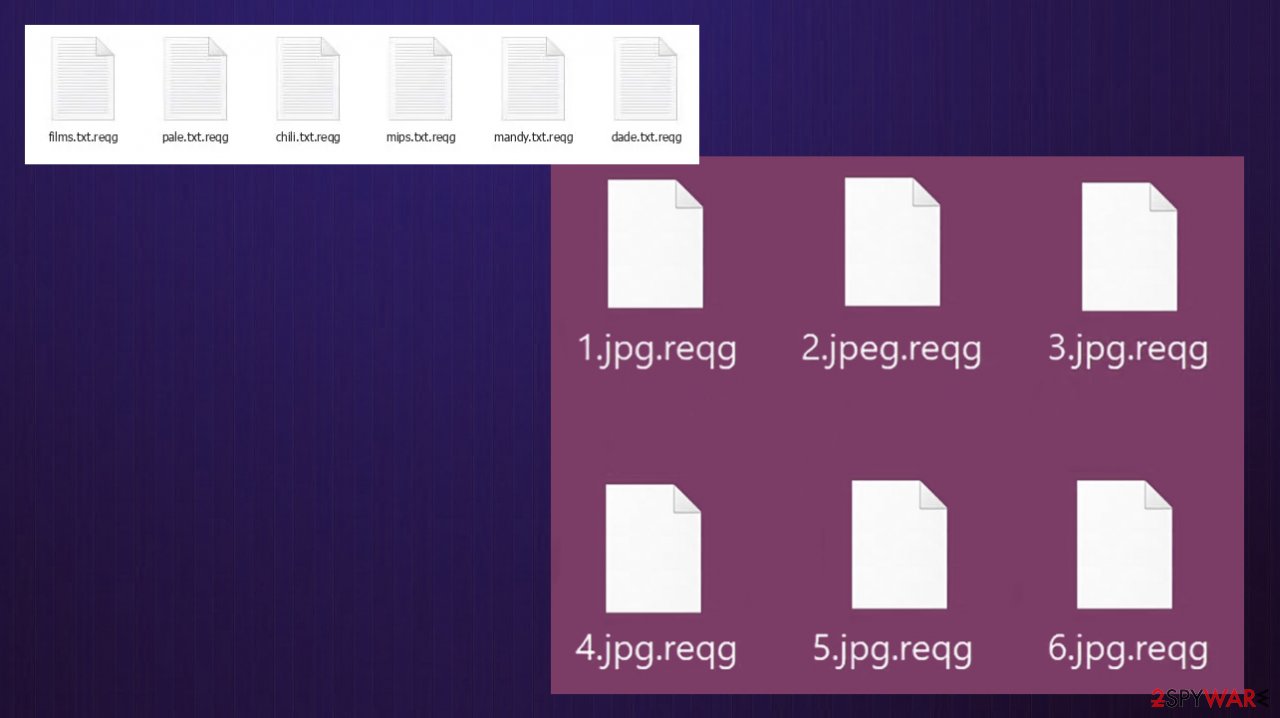
During this process, a fake Windows update pop-up window is usually shown purposely – this is to stop victims from interrupting data locking by turning off the PC. The virus uses a sophisticated RSA encryption algorithm to lock videos, documents, pictures, and all the other important personals files – they all receive a .reqg extension as well. After this, users can no longer open or modify file contents – this is one of the main symptoms and goals of ransomware.
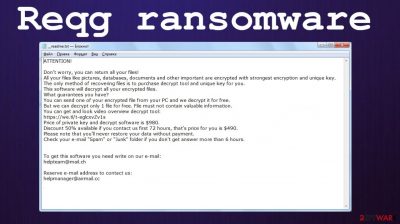
The data locking virus then delivers a ransom note titled _readme.txt. This file includes all the information required for users to understand the demands of cybercriminals. According to the message, victims have to pay a $980 ransom in Bitcoins to be transferred into a particular crypto wallet. As usual, hackers also offer a 50% discount if the contact is made within 72 hours of the attack. For communication purposes, two emails are provided:
- manager@mailtemp.ch
- managerhelper@airmail.cc
It goes without saying that at this point, many people panic. While ransomware is truly horrifying to experience, you should take a correct course of action and never rush to pay the ransom to cybercriminals, as there could be other methods that might just work for you.
Since Reqg ransomware is a version of a widespread malware strain known as Djvu. Due to its prevalence, cybersecurity researchers have been working hard to find ways to prevent the spread and help its victims. To this day, there are very few methods that could help only a limited number of victims. If you are among the lucky few, you might be able to restore your files with the help of the Emsisoft decryption tool – we explain how to use it below.
| Name | Reqg ransomware |
| Type | File locking virus, ransomware |
| Malware family | Djvu/STOP |
| Distribution | Software cracks, pirated program installers |
| Encryption method | RSA |
| File extension | .reqg |
| Ransom note | _readme.txt is delivered to several system locations, including desktop |
| Contact | manager@mailtemp.ch, managerhelper@airmail.cc |
| Previous versions | Muuq, Aeur, Nooa |
| Malware removal | To completely terminate malware from the infected computer, a full system scan with powerful anti-malware should be performed |
| Data recovery |
The only secure method to recover files safely is by copying them from backups. Other options include:
|
| Windows fix | In some cases, ransomware or other threats might seriously damage Windows systems to the point that the OS needs to be reinstalled. To avoid that, we recommend trying to fix the virus damage instead with tools such as FortectIntego |
Reqg ransomware: modus operandi
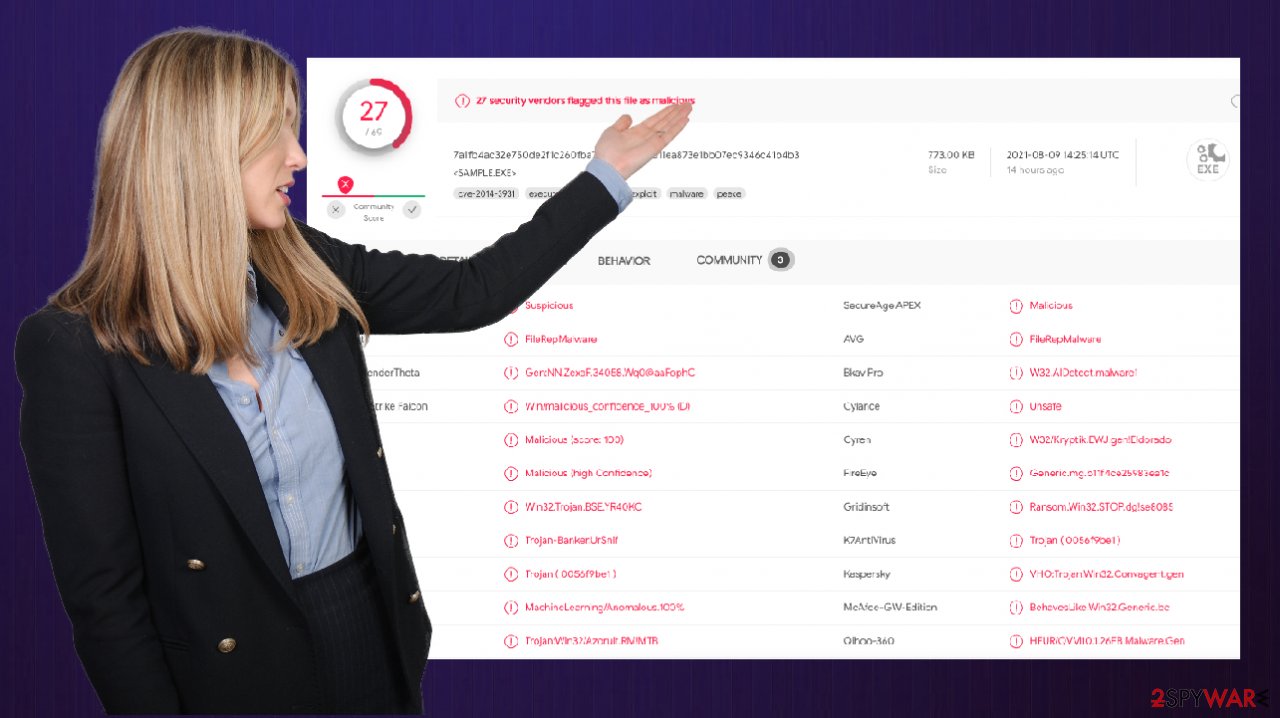
Reqg virus belongs to the notorious malware family, which originally was found as STOP ransomware at the end of 2017. Since its initial versions, such as Keypass or Infowait, the malware underwent quite a few changes over the years. In 2019, security researchers from Emsisoft had found cracks in ransomware’s AES encryption and managed to create a free working decryption tool that worked for 148 versions out of 160 at the time.[1]
Obviously, malicious actors are there to make profits, so they were very quick to react and changed the encryption method to a more secure RSA.[2] Ever since then, new versions of malware threaten hundreds of users every day – it became the most prevalent ransomware strain that attacks home users.
To avoid this dangerous infection in the future, we strongly recommend you stay away from torrents and websites that distribute software cracks.[3] Most importantly, never ignore warnings that come from your security software, believing that it is a false positive!
How to file encryption and ransomware works: methods to restore files
First of all, it is important to mention that ransomware infection and data locking are two separate processes. While the former can be dealt with with the help of powerful security tools, the latter is a completely different issue in itself.
Once you remove malicious files of the Reqg virus, your files will not be restored to their previous state, which means that you will still not be capable of opening or using them. This is a very harsh truth that many users struggle to understand and often believe that security software can restore the data. It is simply not what it is designed for.
In fact, cybercriminals are correct about the facts that they state in the ransom note:
ATTENTION!
Don’t worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-fhnNOAYC8Z
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
During the encryption process, the malware generates a key from the victim’s computer, which is sent to the servers that belong to the attackers. These keys are unique to each victim, which means that they can not be shared between different people who had their files encrypted with Reqg. Besides, the malware deletes all the Shadow Copies (automatic Windows backups) with the command vssadmin.exe Delete Shadows/All/Quiet to prevent users from restoring their files easily.
So, what to do now? How to deal with this difficult situation? The answer strongly depends on your personal situation, actually. For example, if you have previously prepared backups, all you have to do is remove malware from your system – we recommend using SpyHunter 5Combo Cleaner or Malwarebytes for the job. Make sure that security software is updated before you employ it to scan your device. If you cannot use your anti-malware for some reason, access Safe Mode with Networking – we explain how below.
Next, you have to prepare copies of your encrypted files. In case you fail to do that and attempt using recovery solutions, you might permanently damage your data, and even a working decryption tool will not help you. Make sure you backup on a separate storage device, such as USB flash or cloud storage (Google Drive, OneDrive, etc.).
Once that is done, you can proceed with the data recovery process. Keep in mind that paying cybercriminals is not recommended, as it only increases hackers’ motivation to produce more malware and infect more people – their illegal business works. Security companies, law enforcement agencies, and the infosec community are strongly against it, and so are we. Instead, try the methods below.
Emsisoft Decryptor
As already explained, the initial process of file locking includes retrieving a unique key from a remote server. If this operation is successful, then you are likely not going to get your files back. But if it fails, this means that there is still hope for getting one’s data unlocked with the help of a decryption tool from Emsisoft.
In order to know whether or not the decryption is possible, you need to try using the tool. Keep in mind that this method might take some weeks or even months to work, as one of the affected users needs to pay criminals, retrieve the key, and then share it with Emsisoft researchers.
- Download the app from the official Emsisoft website.
![Reqg ransomware Reqg ransomware]()
- After pressing the Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
![Reqg ransomware Reqg ransomware]()
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.
![Reqg ransomware Reqg ransomware]()
- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.
![Reqg ransomware Reqg ransomware]()
- Press Decrypt.
![Reqg ransomware Reqg ransomware]()
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
Try Data recovery software
If the above method revealed that online keys were used to lock your files, you are in a rather dire situation. However, there is a chance that third-party recovery software might be able to restore at least some encrypted files for you:
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Reqg ransomware Reqg ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don’t forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
Ransomware damage and how to fix it
This malware was previously distributed along a well-known banking Trojan AZORult, which is a dangerous malware capable of stealing user credentials, banking information, crypto-wallets, and other data. Therefore, it might be that there are other malicious programs installed on your system along with the ransomware. To make sure it is not the case, you should scan your device with anti-malware software.
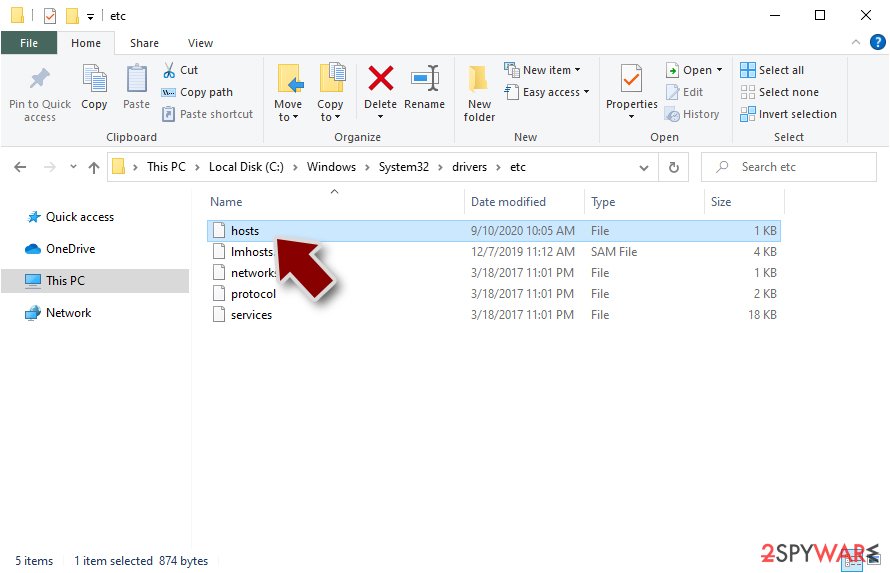
After eliminating all the malicious files and components from your system, there are plenty of other things to take care of. First of all, Reqg virus tampers with your “hosts” file – it inserts IP addresses of the most prominent security websites (including 2spyware.com), preventing users from seeking help with malware removal and alternative data restore methods. This is why you might get an error DNS_PROBE_FINISHED_NXDOMAIN when trying to access any of these websites.
Here’s an example of “hosts” file entries that were injected by ransomware:
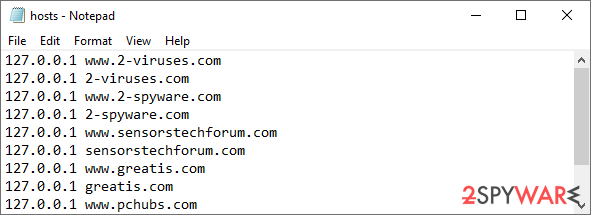
In order to restore your ability to access all websites without restrictions, you should either delete the file (Windows will automatically recreate it) or remove all the malware-created entries. If you have never touched the “hosts” file before, you should simply delete it by marking it and pressing Shift + Del on your keyboard. For that, navigate to the following location:
C:\Windows\System32\drivers\etc\
Once a computer is infected with malware, everything changes. The system may be altered to operate differently, and important files can get deleted or damaged without the possibility of being repaired by antivirus software. This leaves users struggling with performance issues, stability problems, and usability difficulties until they have no choice but to perform a full Windows reinstallation which gets rid of all traces of infection.
Therefore, we highly recommend using a one-of-a-kind patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it can fix various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors and freezes.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
Getting rid of Reqg virus. Follow these steps
Access Safe Mode to remove malware from Windows
If malware is not letting you use antivirus in normal mode, access Safe Mode and perform a full system scan from there.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.

Once you reach Safe Mode, launch SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable antivirus, update it with the latest definitions, and perform a full system scan to eradicate malware and all its malicious components.
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Emsisoft releases new decryptor for STOP Djvu ransomware. Emsisoft. Blog.
- ^ Ron Franklin. AES vs. RSA Encryption: What Are the Differences?. Precisely. Data and security.
- ^ Lawrence Abrams. Djvu Ransomware Spreading New .TRO Variant Through Cracks & Adware Bundles. Bleeping Computer. Technology news and support.





















