Repairquickcompletelythefile.vip ads (scam) - Free Guide
Repairquickcompletelythefile.vip ads Removal Guide
What is Repairquickcompletelythefile.vip ads?
Repairquickcompletelythefile.vip is an untrustworthy website that might expose you to online scams
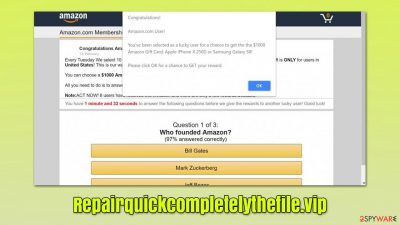
There is a huge number of websites on the internet, and that number is constantly growing. While most of these sites are used as a source of entertainment, news, socializing, and streaming content online, a small portion of them are dedicated for malicious purposes, and Repairquickcompletelythefile.vip belongs to the latter group – it is dedicated to promoting various fake deals and make people install browser hijackers or other suspicious software.
Users might encounter this site under different circumstances – clicking on a link on some other website is the most likely culprit. At other times, the URL might temporarily show up before accessing another page. Even though this activity does not mean anything sinister when encountered just once, repeated encounters might be a sign of adware infection.
Adware is a type of potentially unwanted software that is usually spread via software bundles or similar deceptive methods, thus users might not even know that they have it installed. This is why checking the system for malware is so important as soon as symptoms become apparent. We explain how to deal with that in the later sections of the article.
Repairquickcompletelythefile.vip can often incorporate all types of scams or lead to other websites that promote them. Therefore, it is highly recommended to avoid interacting with anything related to it – closing the tab and not exploring the contents or the site is the best thing to do.
Unfortunately, since many users might fall for the fake messages it displays, the consequences might already be unavoidable (this is one of the main reasons why it is important to know more about how scams work). We will provide more information about scams and how to avoid being a victim of one below.
| Name | Repairquickcompletelythefile.vip |
|---|---|
| Type | Scam, adware, redirect |
| Distribution | Software bundles, malicious redirects, ads |
| Symptoms | Redirects to suspicious websites that hold plenty of commercial or scam content; fake messages offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| risks | Installation of other potentially unwanted software or malware, personal information disclosure to cybercriminals, financial losses due to scams, etc. |
| removal | Adware can be installed as a browser extension or a program on the system. You can either get rid of it manually by following our guide or scanning your system with a powerful SpyHunter 5Combo Cleaner security tool |
| Additional steps | Cleaning web browsers is one of the secondary things you should do after PUP/malware removal to secure your privacy. You can use FortectIntego to do it quickly |
Online scams: what you should know
As already mentioned, not all websites are created to be informative or useful. There are plenty of malicious actors out there who are willing to trick users into doing something that they would not initially – this is one of the main principles of social engineering[1] – malware operators and scam websites use it regularly.
While most users would not visit malicious websites on purpose, the probability of encountering them often falls on them. For example, torrents, illegal video streaming, software cracks, and similar sites often have booby-trapped links and downloads which, once clicked, could reroute users to Repairquickcompletelythefile.vip, Redlight-mc2.club, Rememberbyshop.top, or similar places.
Once users land on the destination site, they might be shown practically anything, although it always comes down to it being deceptive. Here are a few examples:
- A message might tell that visitors have been selected to participate in a survey and all they have to do is answer a few questions about themselves and that they are eligible for a gift such as the newest iPhone. Then, they might be asked to provide personal information about themselves (such as email, name, etc.) or even be tricked into providing their credit card details in order to allegedly confirm their identity.
- Fake and illegal video-streaming websites would operate similarly, promising users copyrighted videos in exchange for personal information such as credit card details.
- Users might be shown with an unexpected warning, flashing window, or similar message which would claim that their device has been infected with a virus. They would be then asked to call fake tech support or download software that would allegedly get rid of the virus. These scams can be particularly dangerous as they impersonate legitimate tech companies such as Microsoft or Google.
- Fake updates or “missing software” warnings might use the name of Flash or other popular software[2] to make users install malware on their systems.

As evident, the diversity of scams is very broad and the likelihood of encountering them varies depending on your own actions. First of all, you should always avoid high-risk websites, as they are usually poorly protected against hacks or are even operated by malware actors.
Employing powerful security software, such as SpyHunter 5Combo Cleaner and Malwarebytes, can stop the execution of most malware attacks on the web. Of course, the security can never be 100%, but it significantly reduces the overall risk of malware infections. Likewise, an effective ad-blocker can prevent malicious scripts from being executed once a dangerous website is accessed.
Stop the Repairquickcompletelythefile.vip redirects effectively
It is important to mention that if you have only encountered a suspicious website once you clicked on a link and never interacted with anything shown in further pages, you shouldn't be too worried, as the chance of being infected is relatively low. That being said, you should never dismiss the possibility of the infection, and we recommend following the steps below to ensure that it is not the case.
Let's start with the programs that are installed on the system level – these could be the most impactful on the system as a whole. When it comes to malware categories, potentially unwanted programs usually don't use obfuscation[3] techniques and are visible on the installed program list.
Note: if adware you are infected with is aggressive, SpyHunter 5Combo Cleaner security software can get rid of it for you fully, and you won't gave to proceed with the steps below.
If you are using Windows, you should access Control Panel and then go to the installed program list. Here, look for anything suspicious – file converters, video players, system optimizers, and similar. If you are not sure, simply skip this step entirely.
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
On a Mac, moving an app to Trash might not suffice when it comes to adware. There could be plenty of additional files that might be placed on the system, so you might have to delete them too.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Next, we should check the extensions that are installed on your browser. In recent years, most potentially unwanted applications are spread mainly as extensions, as they are very easy to make. If you have never done that before, here are the instructions for major browsers:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
You should then take your time to clean the web browsers properly to ensure that the tracking is no longer is performed via cookies or other technologies. For example, cookies might stay on the browser locally for months or even years if they are not deleted manually. You can clear browser caches manually as we explain in the instructions or using FortectIntego PC maintenance and repair tool.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Social Engineering. Imperva. Data protection.
- ^ Graham Cluley. Fake Adobe update really *does* update Flash (while also installing cryptominer). Tripwire. The State of Security.
- ^ What is Malware Obfuscation?. SecurityBoulevard. Security Bloggers Network.












