Rememberbyshop.top ads (scam) - Free Guide
Rememberbyshop.top ads Removal Guide
What is Rememberbyshop.top ads?
Rememberbyshop.top is a malicious website that tries to make visitors participate in a survey for expensive gifts
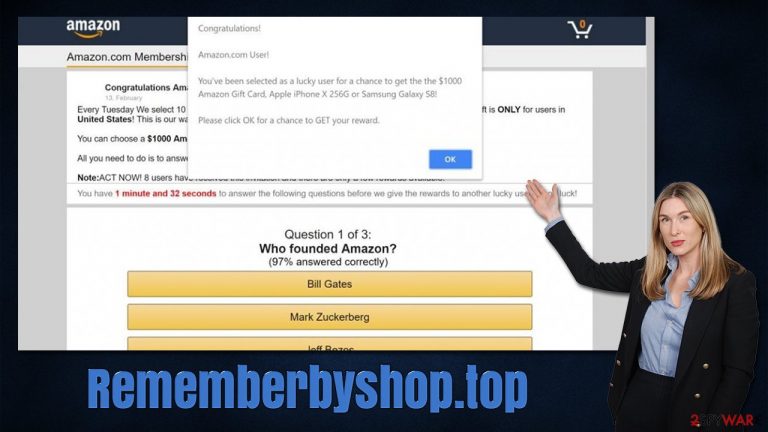
You might encounter Rememberbyshop.top accidentally while browsing the web on Google Chrome, MS Edge, Mozilla Firefox, or Safari on Windows or Mac computer. Upon entry, you might be shown all sorts of surveys or other types of scams, although it has been noted that it mostly propagates the “You've made the 9.68-billionth search” scam.
According to the message, the visitor has been selected by Google to receive an alleged “thank you gift.” There are three prize trophies displayed, with buttons below to select one of them. Once this is done, users are then redirected to further pages that can ask them to provide personal information or make them subscribe to useless services, just to later be charged monthly fees. In other cases, people might be presented with similar scams that incorporate gift cards and other attractive prizes, although the principle of operation remains the same.
If you have encountered the Rememberbyshop.top fake giveaway, you should not interact with it further, as your personal details might be leaked to cybercriminals, or you might end up suffering from financial losses or even identity fraud.
Below we will explain how the scam operates in detail, what to do to avoid them. Likewise, while the appearance of scams while browsing the web does not necessarily mean your device is infected, there is a chance that adware[1] is causing these redirects, so this aspect should always be investigated as well.
| Name | Rememberbyshop.top |
|---|---|
| Type | Scam, phishing, adware |
| Goal | Make people provide personal information, subscribe to useless services, download malicious software or subscribe to push notifications |
| Distribution | Redirects from other malicious websites, adware |
| Dangers | Those who have malicious software installed on their systems are more likely to encounter dangerous websites, resulting in financial losses, malware infections, etc. |
| Removal | To get rid of unwanted apps manually, you can follow our removal guide below. If the unwanted ads and other disruptive behavior does not stop, you should scan your computer with security software and delete all threats automatically |
| Further steps | Malware or adware infections can diminish the performance of your computer or cause serious stability issues. Use FortectIntego to remediate your device and ensure that the virus damage is fixed |
How survey scams operate
Social engineering[2] is a technique that plays with human emotions in order to reach the desired effect. It has been implemented on the world wide web for many years for various malicious purposes – be it malware infections, sensitive information extraction, and much more. The fact is, the scheme is never used for anything positive and can be disastrous for those who are tricked by it.
There is plenty of fake surveys, lottery, free gifts, and other scams out there. Users would not visit websites (such as Rememberbyshop.top) that spread these scams intentionally – they are typically led there by some type of link click or an automated script on another site.
In most cases, malicious redirects are employed by less secure websites, such as those that host pirated software, illegal video streaming,[3] X-rated, gambling, online gaming, and much more. Likewise, adware could also be one of the main reasons why users are encountering malicious ads and websites while browsing the internet.
Once on the fake website, users are usually caught off guard by an unexpected proposition – they can get free stuff! To make the scam more believable, its creators use the names of popular companies such as Google, Amazon, UPS, or similar. They also use common themes, formatting, and other attributes that would remind users of the official source.
Here is one of the messages that users might see once they enter Rememberbyshop.top:
You've made the 9.68-billionth search!
Congratulations! You are the lucky winner!
Every 10 millionth search is reached worldwide, we will proclaim a winner to send out a thank-you gift.
Please select your lucky prize below and claim it by following the instruction.
Here you can see typical phishing techniques being used – visitors are told to be the chosen ones for a free gift to be received. They are offered to click on one of the three options, which usually reveals a pricy item, such as the latest iPhone or a PlayStation. Next, people are asked to enter their personal details, such as name, email, and sometimes even credit card details.
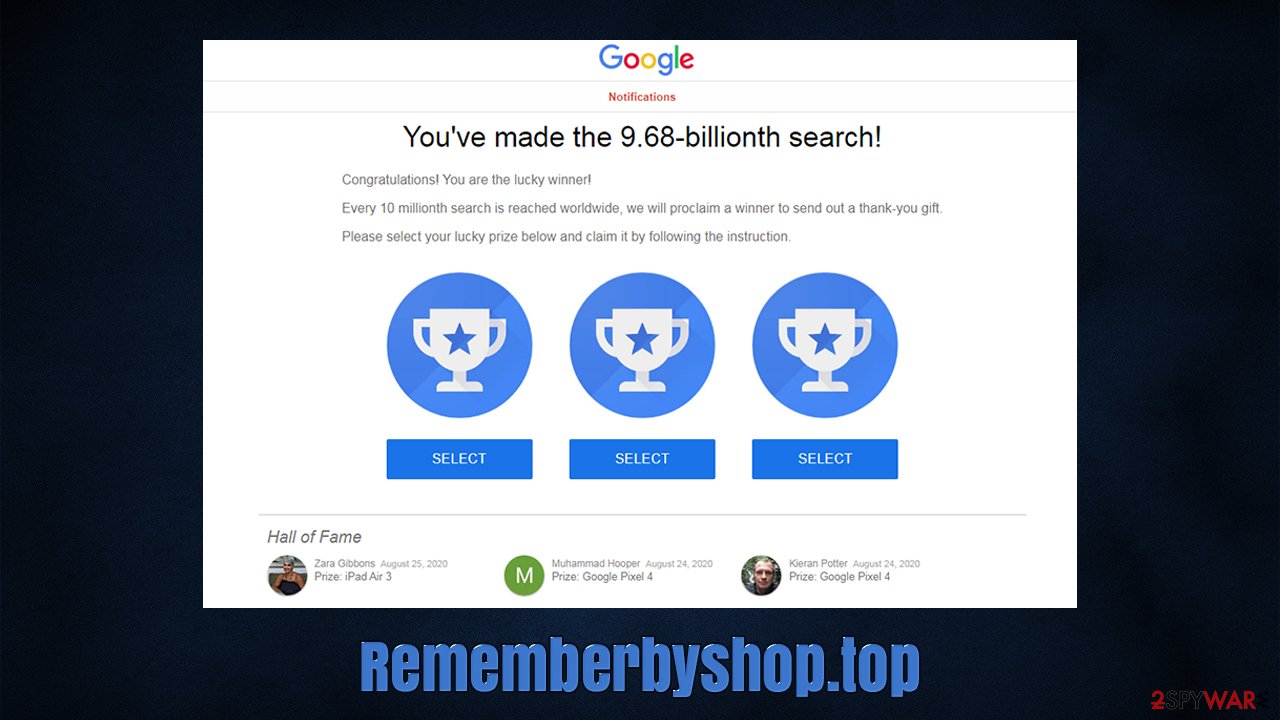
Allegedly, the credit card information is needed for the shipment costs or something similar. Later, they might be shown a “Success” page and told to wait for the gift to arrive, only to later see that it never happens. Unfortunately, it is too late by then. Those who fall for the scam risk having this information stolen and used for malicious purposes. For example, it might be sold on the dark web to the highest bidder. It all comes down to money.
To avoid being scammed in the future, please always check the URL that shows the message – it always serves as a strong base to recognize deception. You should always keep in mind that Google or any other company would not randomly give out expensive gifts to people – there are simply no benefits to it. Remember, if it sounds too good to be true, it likely is the case.
Checking the device for infections
First of all, if you have interacted with Rememberbyshop.top scam, you should immediately change the passwords you could have disclosed. Also, if you have entered your banking details, make sure you contact your bank and explain what happened, you should receive the help you need to prevent further issues with your account.
Another important step here is making sure that your system does not have any malicious programs installed on it. Therefore, the first thing you should do is scan your system with powerful security software, such as SpyHunter 5Combo Cleaner or Malwarebytes. It can locate all malware and most aggressive adware and remove it automatically for you.
Nonetheless, some potentially unwanted applications might not be detected automatically as they are not inherently malicious, but they can lead to a lot of privacy and security issues in some cases. Thus, check the installed applications section as follows:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Adware, browser hijackers, and other potentially unwanted programs quite often come in the form of browser extensions. While unintentional installation is possible, some apps that have been running on users' browsers for years later turn out deceptive (usually due to owner change).
Therefore, if you are experiencing various browsing disturbances – ads, redirects – you should also check your extension section. If you are not sure which add-on is causing problems, we recommend removing them all and then reinstating each app separately to find the culprit.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.

MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Finally, you should either reset or clean your browser's cached files. Cookies and other technologies can be used to track you and stay installed for years if not removed. Besides, large caches might start causing errors while browsing. If you want a quick way to do that, scan your system with FortectIntego. Alternatively, proceed with these steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Will Kenton. Adware. Investopedia. Sharper insight, better investing.
- ^ Social Engineering. Imperva. Data protection.
- ^ Vincent Chang. Be wary of malware from free video streaming websites. The Straits Times. Breaking News, Lifestyle & Multimedia News.
