Criminals used Safari to redirect users to adult-oriented sites
On March 27, 2017, Apple released an update to iOS 10.3[1], which improved Safari browser’s (mobile version) behavior regarding JavaScript pop-ups. This update was released after researchers from Lookout[2] reported an issue in mobile Safari browser that allowed scammers to execute a never-ending loop of JavaScript pop-ups and prevent the user from using the mobile browser at all. It turns out that scammers managed to set up dozens of bogus websites that were meant to lure in people looking for pornography, erotic pictures, free music and similar content. After luring the victim into these websites, scammers immediately launched the scareware attack[3] from domains that they have registered. These phishing domains were titled as pay-police[.]com, x-ios-validation[.]com/us[.]html and similarly only to scare the victim and trick him/her into thinking that their naughty activities were auto-detected by some legal authorities. Those phishing websites[4] immediately launched a threatening message, for example, “Your device has been locked for illegal pornography” or “In order to remove blocking, you have to pay the fine of £100 with an iTunes pre-paid card.” At the same time, the malicious JavaScript code kept launching a “Cannot Open Page” pop-up, which reappeared each time the user tried to close it by clicking “OK.” Scammers sought to force the victim to pay the ransom, stating that it is the only possible way one could regain the control of the compromised web browser.
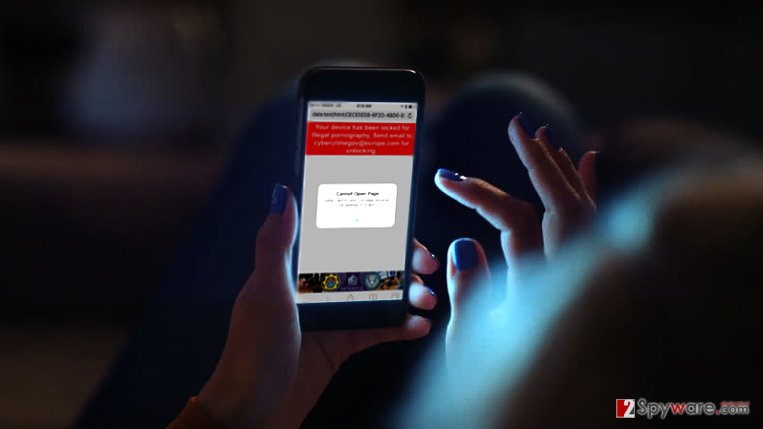
However, despite threatening messages and scary warnings to “deliver case materials to Metropolitan Police,” there was no real danger at all. It turned out that more experienced computer users were able to handle the problem by simply clearing Safari browser cache via device’s settings. Apparently, not many users sought for help due to content they were trying to explore. According to researchers from Lookout, “attackers effectively used fear as a factor to get what they wanted,” and here we can see a perfect example of a social engineering attack[5]. Scammers managed to force uninformed users to pay the ransom just by telling them that they are doing something illegal, although their statements were entirely incorrect. Some victims hastily supposed that it was true and paid the ransom instead of looking for help online using another device.
It is highly advisable not to believe scary messages that pop-up on your device’s screen and urge you to do something in a rush. If you haven’t upgraded your iOS device to 10.3 version yet, do it ASAP, however, do not forget that frauds quickly find new ways to deceive users; therefore we expect more similar scareware campaigns in the future.
- ^ About the security content of iOS 10.3. Apple Support. Apple Security Updates.
- ^ Andrew Blaich, Jeremy Richards. Mobile Safari scareware campaign thwarted Read more: Mobile Safari scareware campaign thwarted. Lookout Blog. Blog Posts from Cybersecurity Experts.
- ^ Defending Against a Scareware Attack. FraudWatch International. Expert Explanations.
- ^ How Can I Identify a Phishing Website or Email?. Yahoo Safety. Top Security Tips.
- ^ What is Social Engineering?. Webroot. Business Security Resources - Endpoint Information.

