Smart Protector (Free Instructions)
Smart Protector Removal Guide
What is Smart Protector?
Smart Protector – a fake security tool with falsified virus scan results
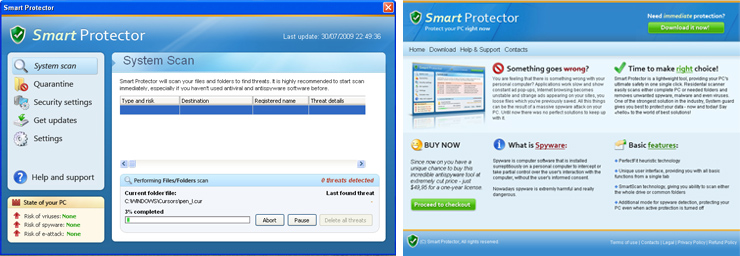
Smart Protector is a rogue security program that uses misleading and deceptive methods to trick you into buying the program. The rogue application is promoted through the use of bogus advertisements that pretend to be online anti-malware scanners. After the fake scan, those scanners state that your computer is infected and that you must install the fake security tool to protect your PC.
No matter what you click in those fake online warnings, you will be automatically redirected to the homepage of Smart Protector. Do not install this useless program. If it was installed without your knowledge, then remove it from the system as soon as possible.
| name | Smart Protector |
|---|---|
| Type | Rogue antispyware, fake security tool, PUP |
| Purpose | Persuade users into buying licensed version by showing falsified, predetermined virus scan results |
| risks | Monetary losses, privacy issues, malware infections |
| Distributions | Official pages, fake online virus scanners, software bundles, freeware |
| Elimination | Remove this rogue tool automatically by scanning your infected computer with a legitimate anti-malware software |
| System repair | To undo any damage, this parasite may have caused to your system, run system diagnostics with the FortectIntego computer tune-up tool |
You may actually find another program with a similar name that has many good reviews. It is called Smart Protector Pro, which is a legitimate program and has nothing to do with the fake anti-malware software. This parasite was promoted on official websites, but it could have been installed on your device without your knowledge through software bundles, deceptive ads, fake Flash Player updates, and other sneaky techniques.
Once installed, Smart Protector will ostensibly scan your computer and display various infections that won't be removed unless you first purchase the program. The scan results are fake. Please ignore them. To make things worse, this parasite will constantly display fake but legitimately looking security alerts from the Windows Taskbar. Here's an example of one of the fake notifications meant to scare you:
WARNING: Your PC is seriously infected!
There are 30 possible threats in your system. This can lead to loss of data!
It may also hijack your Internet browser and slow down your computer. That's why you must remove the intruder from the system. We recommend sticking to automatic removal by scanning your device with a reliable security tool. If you decide to do it manually, please use our free instructions displayed below.
If the rogue tool prevents you from downloading or opening legitimate AV software, please reboot your computer in Safe Mode with Networking and remove it then. Afterward, ensure that your device runs without any hiccups by performing system diagnostics with compatible software.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Smart Protector. Follow these steps
Uninstall from Windows
-
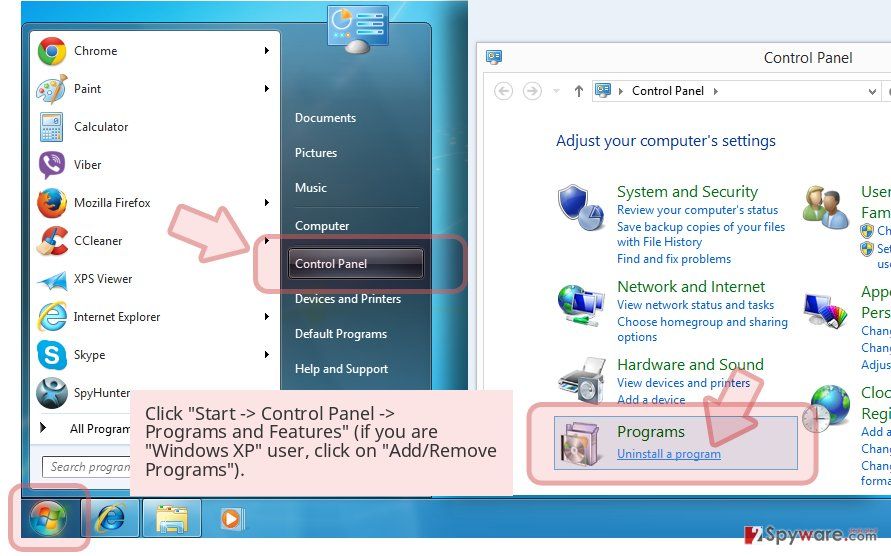
Click Start → Control Panel → Programs and Features (if you are Windows XP user, click on Add/Remove Programs).

-
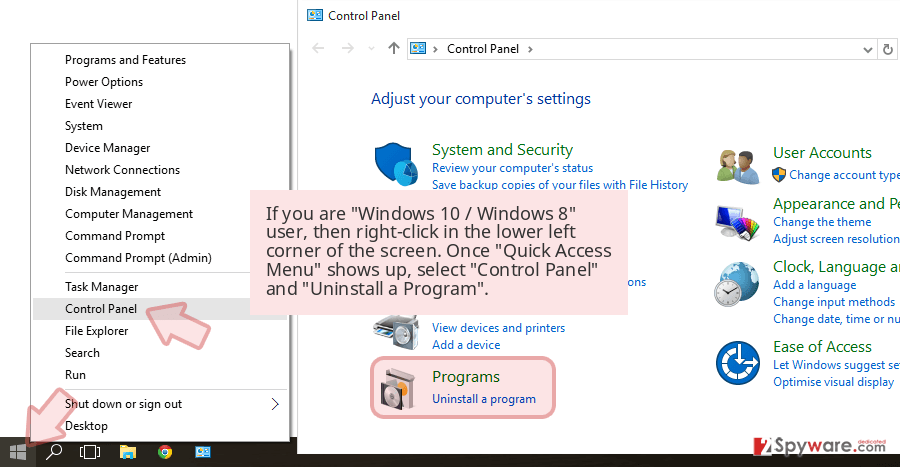
If you are Windows 10 / Windows 8 user, then right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.

-
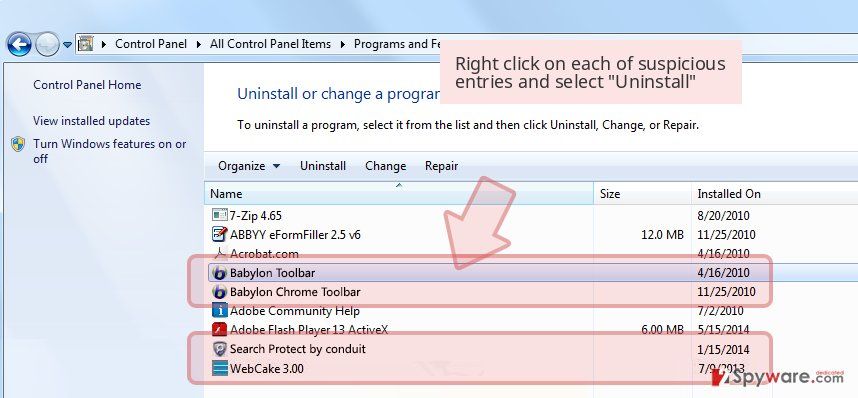
Uninstall Smart Protector and related programs
Here, look for Smart Protector or any other recently installed suspicious programs. -
Uninstall them and click OK to save these changes.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Smart Protector registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting rogue antispyware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.