How to remove rogue antispyware
Rogue anti-spyware (sometimes you can find it as rogue security software) is a term used to describe fake anti-spyware software. Programs that belong to this category can also be categorized as malware and virus. The main intention of rogue anti-spyware is to infect their computers, display aggressive security notifications and make their owners purchase its “full” or “licensed” version for fixing the system. In reality, the only thing that has to be eliminated is rogue security software.
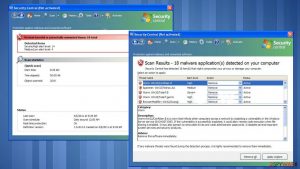
When dealing with the fake anti-spyware, you can be convinced that it is a reliable security application capable of finding malicious files on the system because such programs look very professional. Unfortunately, but no matter how good their GUI looks, they have no virus database, which should be there for an appropriate system scan and the ability to spot malicious files on the computer. In most of the cases, they report about legitimate system components and claim that the victim has to remove them from his/hers computer. That’s how rogue anti-spyware programs manipulate people into purchasing their “licensed” versions. As soon as hackers receive the money, they disable their rogue anti-spyware applications for a certain amount of time. Sooner or later, a virus starts its work again and tries to steal more money from its victim.
Removing rogue anti-spyware from the system is very important because such programs can also be used for infecting it with additional viruses. Also, they can be used for collecting various information needed for identity theft and similar crimes. Finally, they can cause serious issues related to computer’s functionality, such as system slowdowns and crashes. Each of viruses that belong to a rogue anti-spyware category can be removed with the help of reliable anti-spyware.
Routes used by rogue anti-spyware for infiltration:
The most of rogue anti-spyware programs infiltrate computers without users’ approval. Here are the main methods used for infecting computers:
- Malvertising. The majority of rogue anti-spyware apps have been spread via fake pop-up ads. Such notifications are typically set to report about possible issues related to computer, so there is no surprise why there are so many people who have clicked such ads and downloaded rogue software to their computers. Such ads can also claim that people will get the ability to fix their computers for free, but, as you can see, it is just another lie used to infect PC systems with rogue anti-spyware.
- Infected email attachments. A program, which belongs to a rogue anti-spyware category, can also be downloaded as a legitimate email attachment. Typically, viruses are spread as bank-related documents, invoices, reports, disclosures and similar attachments that could trick people into downloading them to their computers.
- Other viruses. There are lots of other threats that can be used for the distribution of rogue anti-spyware. The most popular of them are Trojan horses, worms, and backdoors. These threats can open the back door of the system and install needed files without victim’s interaction and approval. Also, the rogue anti-spyware trojan can hide these files in needed locations and then launch them as soon as a required moment comes.
Typical activity of such malware:
Programs that are categorized as Rogue anti-spyware seek to convince their victims that their computers are seriously infected and that the only tool, which can be used for removing notorious viruses, is the licensed version. If rogue manages to infiltrate the system, it starts seeking its aim with the help of such activities:
- Blocking legitimate security software and websites. This is an important task in the functionality of rogue anti-spyware because it helps the virus to prevent its elimination from the system. The only way to unblock legitimate websites and launch legitimate anti-spyware is to remove the threat.
- Causing continuous system scanners and warning messages. It may seem that Rogue anti-spyware software is capable of scanning computer just like legitimate anti-spyware. However, this activity is corrupted and used just for misleading the victim into thinking that his/hers computer is infected with tens or even hundreds of different threats. If the victim ignores the warning, rogue continues pretending to scan the system and keeps displaying its fake warning messages.
- Slowing down the whole PC’s functionality. For trying to convince its victim that computer is seriously infected, the rogue anti-spyware can cause system slowdowns, system crashes, and similar performance-related issues.
- Initiating redirects to its purchase page. From time to time, you can be redirected by a rogue anti-spyware to its purchase page. The most of such websites can be very dangerous, so it is not recommended visiting them.
The most dangerous examples of rogue anti-spyware:
System Tool. Since the day this rogue anti-spyware showed up in the PC world, System Tool has infected thousands of different computers. It is known that it started spreading around in 2010 and kept doing that for more than three years. This program had caused lots of various issues for its victims, including the loss of their money and infiltration of other malware. The main method that was used for distributing it involved fake notifications offering people to check their computers for free.
Security Defender This rogue anti-spyware showed up in 2011. Since then, it has been infecting poorly protected PC systems. Once inside the computer, it looks like it is capable of defending the system from malware. Unfortunately, but this image is used just to steal the money from unaware PC users. Security Defender has no uninstall option. It can be removed only with the help of reliable anti-spyware, which sometimes can be blocked because of the malware hiding inside the system.
The removal of rogue anti-spyware:
If you want to see what the real danger is, you must check your computer with the legitimate anti-spyware. The most reliable way to remove rogue anti-spyware from the system, is to run a full system scan with FortectIntego or SpyHunter 5Combo Cleaner. After launching one of these programs, you should see that system scanners and security notifications of rogue anti-spyware programs are filled with invented information.
Beware that rogue anti-spyware can block legitimate software for preventing its removal from computer. To avoid this issue, you should try one of these methods:
- Rebooting to Safe Mode with networking;
- Renaming executable file of your anti-spyware program;
- Using other PC to download anti-malware and transferring it to the affected computer with the help of USB drive and similar solutions.
Latest rogue antispyware added to the database
Removing Zuglomo.net ads
Removal of Pest Trap
Getting rid of Security Central
Information updated: 2017-05-11