Clouded (Virus Removal Instructions) - Recovery Instructions Included
Clouded Removal Guide
What is Clouded?
Clouded invents new and very malicious strategy for data encryption
Clouded ransomware is an encryption-based [1] parasite which attacks computers and aims to take their specific files hostage. Archives, media files, Office documents and similar files are of particular interest to the virus developers because they bear personal value to the victims. The relevance of the encrypted files is especially important in the further step of the attack — ransom demands. The correlation behind this is simple — the more personal files the ransomware encrypts, the more victims are willing to pay for their decryption. Currently, the extortionists demand 0.1 BTC [2] for data decryption, but even after making the payment, you can’t be sure whether you will receive the promised decryption key. It is very possible that the criminals will simply vanish with your money, leaving your files unreadable and appended with .cloud extensions. No matter how we would like to say that Clouded virus is decryptable, sadly, it’s not. There is currently no free decryptions software that would allow the ransomware victims to recover their files without supporting virus creators. And it seems that the malware experts will have to go a long way to create one because unlike most ransomware, this one creates individual encryption keys for each of the encrypted files. On top of it all, the virus is programmed to destroy all the encrypted files once the clouded.exe, doccompressed.exe or any of its executable files are terminated. You can try bypassing this malicious functionality by making backup copies of the encrypted files using specialized utilities such as CryptoSearch [3]. If you manage to secure the files, you can remove Clouded ransomware with professional antivirus software such as FortectIntego and wait for the decryptor to be invented. To recover files faster, you may also try out alternative methods provided at the end of this article.
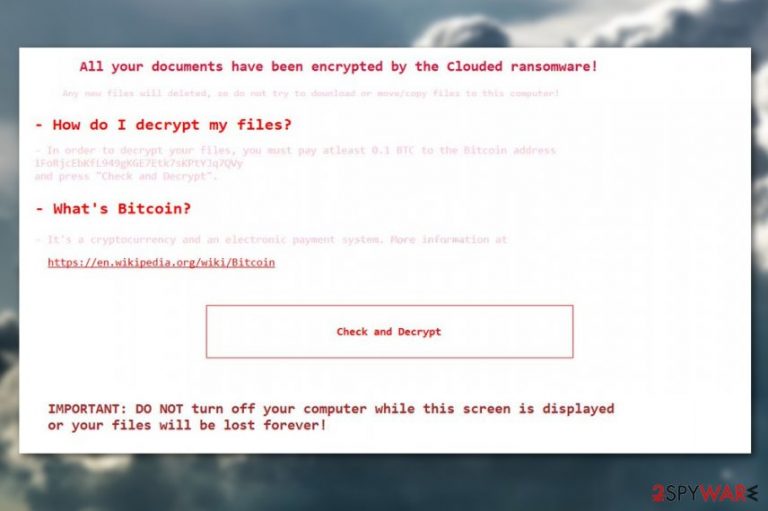
If you have never had your computer infected with ransomware before and feel uncertain what warning signs to look for, pay attention to the speed and performance quality of your device. Slowly operating or malfunctioning system is a tell-tale sign which signals that something might be wrong with your computer. Of course, you have to be extremely observant and know your device as the back of your hand to notice such changes. It is more common for the victims to notice the attack when it has already taken place. Typically, a ransom note is the initial thing that gives Clouded malware away. Below you can see a transcript of this note:
All your documents have been encrypted by the Clouded ransomware!
Any new files will deleted, so do not try to download or move/copy files to this computer!
– How do I decrypt my files?
– In order to decrypt your files, you must pay atleast 0.1 BTC to the Bitcoin address
1FoRjcEbKfL949gKGE7Etk7sKPtYJq7QVy and press “Check and Decrypt”.
– What's Bitcoin?
– It's a cryptocurrency and an electronic payment system. More information at
https://en.wikipedia.org/wiki/Bitcoin
button [Check and Decrypt]
IMPORTANT: DO NOT turn off your computer while this screen is displayed or your files will be lost forever!
Of course, you should not follow any of the demands listed in this note. Instead, start making preparations for the Clouded removal.
Experts opinion: Ransomware is most likely spreading via spam
While there currently there is no certainty about how Clouded virus spreads, the experts believe that the virus distribution strategy should not differ from the rest of the malware in this category. Experts are almost certain that at least on some degree, Clouded ransomware virus developers rely on malicious spam campaigns [4] to deliver malware on targeted devices. There are numerous malicious botnets such as Numucod or Grum [5] that are responsible for spreading spam throughout the world in various shapes and sizes. Having this in mind, you should forget the habit of opening random emails without checking their origin. Spare some time to investigate where the email came from and whether you really expected such letter to reach you. If anything raises suspicions — check back with the sender or simply delete the virus from your PC.
The benefits of automatized Clouded removal
Using reputable antivirus software to remove Clouded virus or other malware from the infected system is the best choice you have in this situation because this malware is very aggressive and any mistake while uninstalling it may end up in the loss of personal data or a complete corruption of the system. We firmly advise you trust Clouded removal only to the hands of professional security vendors who will make sure to provide you with the best service.
Getting rid of Clouded. Follow these steps
Manual removal using Safe Mode
Clouded ransomware virus may destroy your files if you fail to remove it from your device carefully. To safe yourself from unwanted errors, please decontaminate the virus by following the steps below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Clouded using System Restore
If the ransomware is making it impossible to remove its malicious contents from your computer, you should use the following trick to decontaminate it:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Clouded. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Clouded from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Since the virus is currently undecryptable, we suggest you try out the alternative data recovery methods our experts have indicated below.
If your files are encrypted by Clouded, you can use several methods to restore them:
How can you use Data Recovery Pro for the recovery of your files?
Data Recovery Pro is a simple automatic tool you can use for the recovery of your encrypted data. Learn how to use it in the tutorial below:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Clouded ransomware;
- Restore them.
Recover files encrypted by Clouded ransomware by applying Windows Previous Versions feature
Windows Previous Versions feature is a data recovery method which exclusively works only when the System Restore feature is enabled. If it was not enabled before the virus hit your device, the recovery won't work.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try out Shadow Explorer as an alternative data recovery method
Follow the guidelines down below to recover your data using Shadow Explorer. Remember that this strategy will not work if ransomware deletes Volume Shadow Copies of the files, so you may have to go for some other recovery solution instead.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Clouded and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Eric Geier. How to rescue your PC from ransomware. PCworld. News, tips and reviews from the experts on PCs, Windows, and more.
- ^ Nick Ismail. Has ransomware exploded because of bitcoin?. Information-age. For IT leaders from the UK’s fastest growing enterprises.
- ^ Catalin Cimpanu. CryptoSearch finds files encrypted by ransomware, moves them to new location. Bleepingcomputer. News, Reviews, and Technical Support.
- ^ Top 4 Spam Email Campaigns of 2016. TheMerkle. Technology news.
- ^ What is a Botnet?. KasperskyLabs. Resource center.







