Lilocked ransomware (Virus Removal Guide) - Sep 2019 update
Lilocked virus Removal Guide
What is Lilocked ransomware?
Lilocked ransomware is a cryptovirus that targets Linux-based servers and runs Exim software to get on the system
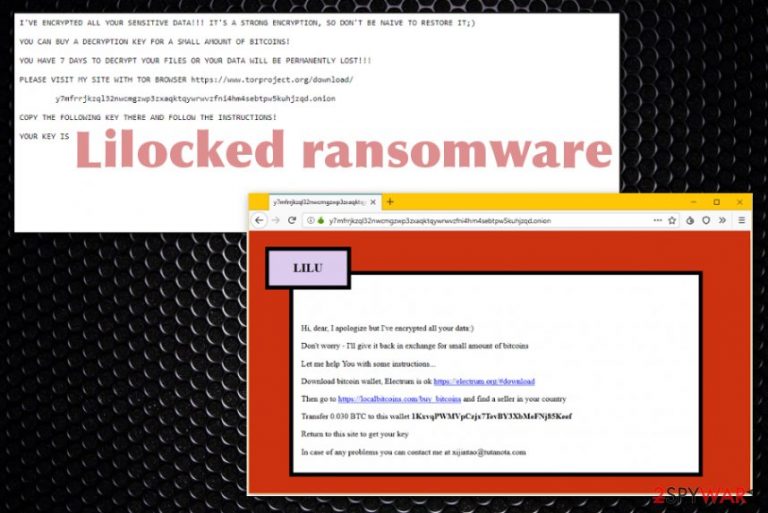
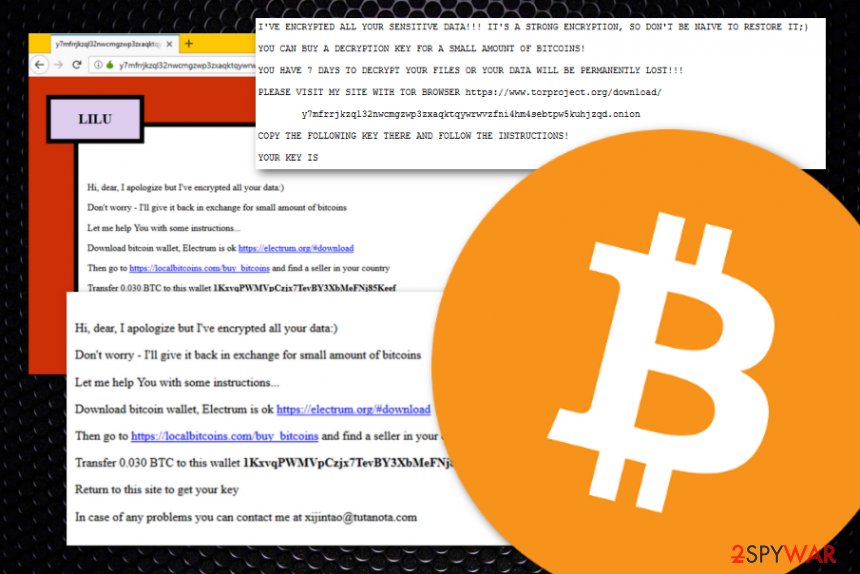
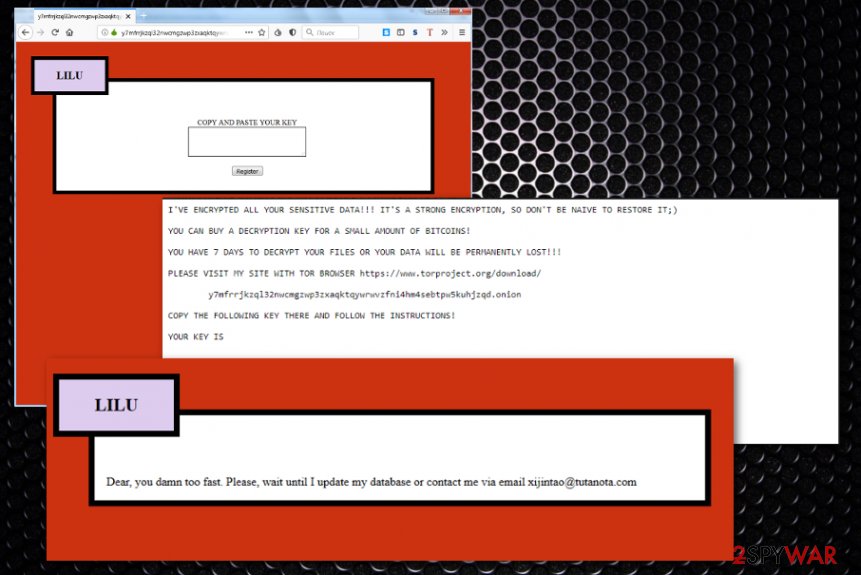
Once Lilocked ransomware virus is done with the file locking process, the ransom note named #README.lilocked.txt gets placed in each folder where the cryptovirus encodes data.[2] The file contains a ransom note, additional information about the encryption and the victims' ID. Then the user gets redirected to the portal, which displays a demand for payment with a particular amount of money needed for receiving the data recovery key. Some reports state about the ransom that goes to $300 and more in Bitcoin. According to recent reports, this threat encrypted more than 6 700 servers already.[3]
| Name | Lilocked ransomware |
|---|---|
| Type | Cryptovirus |
| Target | This damaging ransom-demanding and file-encrypting cyber threat is known to target and attack those machines which are running the Linux operating system |
| First spotted | Security researchers have released some news reports on this threat and they have claimed that Lilocked malware has appeared in the cybersecurity sphere in the middle of July this year |
| Particular features | Encrypts files, marks with .lilocked appendix, delivers ransom demand and loads the dark web page with further instructions and the required amount for file recovery |
| Ransom note | Once Lilocked virus ends up on the targeted machine, it placed the #README.lilocked.txt ransom note in each folder that holds encrypted data |
| File marker | All data and files that are encrypted by Lilocked virus are left with the .lillocked appendix near to their filenames |
| Possible damage | Files get encrypted, possibly permanently and cannot be opened or used properly, info-stealing or damaging malware can get installed and corrupt the device even more |
| Already known | According to various cybersecurity news reports, this virus has already encrypted thousands of Linux-based servers, some of which are included in Google search results |
| Distribution | The ransomware virus might be capable of spreading via outdated WordPress services or outdated software such as Exim. In addition, other malware, spam email attachments, malicious files, vulnerable RDP can carry the malicious payload |
| Elimination | Get the anti-malware tool and remove Lilocked ransomware. Clean the damage using FortectIntego. Also, do not try to eliminate the cyber threat on your own as there is a big risk of creating harm |
Lilocked ransomware is a fairly new cryptovirus that came to the light recently and has no association with previously discovered malware. This program infiltrates the system and encodes stored data. It doesn't affect system files and mainly focuses on files in HTML, SHTML, JS, CSS, PHP, INI, and various image file formats.
Since there is no particular number of victims and the initial entry point of the malware remains unknown, all the facts are generic and based on the functionality and similarities to the common cryptovirus. Lilocked ransomware can victimize even more people than those 6.700 infected servers already known for the researchers.
It is believed that Lilocked ransomware uses outdated WordPress site on the server as a vector of spreading the threat. But this is only an assumption with no particular payload or sample to analyze or confirm. Nevertheless, the virus starts its processes immediately after infiltration and delivers the following ransom note for the victim:
WE APOLOGIZE BUT YOU NEED TO PAY THE RANSOM – ALL YOUR FILES HAS BEEN LILOCKED
IT IS STRONG ENCRYPTION AND YOU LOSS YOUR DATA UNLESS YOU PAY US
PLEASE VISIT OUR SITE WITH TOR hxxps://www.torproject.org/download/y7mfrrjkzql32nwcmgzwp3zxaqktqywrwvzfni4hm4sebtpw5kuhjzqd.onion
COPY THE FOLLOWING KEY THERE AND FOLLOW THE INSTRUCTIONS, YOUR KEY IS
When the provided link is clicked, Lilocked ransomware shows a website that prompts the victim to enter the provided key and then asks them to pay the particular amount in Bitcoin. Particular attempts of malware researchers revealed that criminals demand up to 0.03 BTC – more than $300. The transfer should be made in the Electrum wallet, and then the victim should get encrypted files recovered.
Lilocked ransomware has been detected by tens of different AV engines as a malicious piece of software. However, the detection name might differ each of them when you use another antimalware tool. According to Virus Total virus examination, the ransomware virus is most commonly spotted by these detection names:[4]
- Other:Malware-gen [Trj] (AVG and Avast).
- Trojan.Linux.Lilock.A (Bitdefender).
- Trojan.Linux.Lilock.A (B) (Emsisoft).
- HEUR:Trojan-Ransom.Linux.Lilock.a (Kaspersky).
- Ransom.Lilocked (Symantec).
Reports claim about numerous servers infected with the Lilocked ransomware strain
It is known that Lilu is targeting web servers since the middle of July this year but some of the samples obtained already are related to websites. There is no pattern in particular that can reveal more information about the threat or its developers. However, it is common to believe that Lilocked ransomware uses exploits to gain access to wanted systems.
Even though researchers have discovered that almost 7,000 affected servers remain in the Google search results, specialists have been guessing that there is a much bigger number of infected systems from which the majority might not even be saved in the Google search database.
Particular Exim EK is possibly used to spread on web servers in this campaign.[5] Various pages get delivered on the same web page that the virus redirects to. However, clicking on them can lead to more severe malware than Lilocked ransomware itself. For example, you might get infected with cryptocurrency mining viruses.
You need to remove Lilocked ransomware as soon as possible, and symptoms get noticed because info-stealers can obtain personal data and lead to serious privacy or identity issues. Pages where the key is required opens, other instructions also get displayed for the victim. All this content makes people more scared and tricks them into paying the hefty mounts.
However, experts[6] never recommend to pay and instead offers to perform Lilocked ransomware removal instead. Lilu virus developers only care about your money and have no mercy for their victims. There might be many speculations about the threat, but further analysis is needed and a sample of the virus required for that. You can contact Michael Gilespie on Twitter to provide any information.
Ransomware creators have many methods of spreading crypto-demanding malware
Ransomware infections are known to be capable of spreading through outdated web services such as WordPress or particular software, for example, Exim, that is also out of date. However, these are only just a few ways of how ransom-demanding malware is capable of reaching the targetted computer system.
In addition, it is common for cybercriminals to distribute such type of threats by hacking unprotected RDP configuration and the TCP 3389 port is known to be one of the most vulnerable to hacking attempts. Furthermore, malware developers might take advantage of security flaws (especially when the computer does not include an antivirus tool or it has not been updated regularly).
Furthermore, you can easily meet ransomware through deceptive downloads, botnets, and fake updates, shady download sites are all used to deliver file-locking malware. However, the primary method still is spam emails and infected file attachments filled with malicious macros.
Cybercriminals are very likely to pretend to be from well-known shipping companies, e.g. FedEx or DHL, and tend to send random people order confirmation messages. Usually, the emails come with a particular link which clicked executes the malware or a suspicious attachment that also holds malicious payload.
Protect yourself from possible malware attacks
The best way to stay safe and keep your computer system undamaged from ransomware and similar malware attacks is to pay attention to both manual and automatical security measures required. First of all, ensure that antivirus protection is installed on your machine and operating properly. For good functioning, you need to make sure that regular updates are always completed.
Continuously, keep yourself away from suspicious third-party networks that are marked as unsafe or just cause the feeling of concern. The most avoidable sources should be p2p ones such as The Pirate Bay, various adult-dating and adult-content websites, gambling, and online-gaming networks. If you are looking for a particular product, get it from a reliable source and always check the developer's reputation.
Last but not least, you have to learn how to verify misleading email messages. What you have to do is always check the sender and make sure that the letter does not come from a bogus person. Furthermore, go through the entire text and search for grammar mistakes as no reliable company will leave their texts full of mistakes. Finally, all received attachments should be scanned with antimalware before opening them.
Get rid of the malicious Lilocked ransomware virus with anti-virus protection software
Lilocked ransomware virus is known for attacking servers, websites and already encrypted thousand of servers and data stored on them. You need to react as soon as possible if you want to avoid permanent damage and the possible loss of money. Since there's no pattern – the servers are random, no one is immune or safe.
You shouldn't pay the ransom and remove Lilocked ransomware instead. Gather encrypted files for the potential decryption later on and rely on file backups for restoring processes. You can also check methods listed below for file recovery if needed.
However, for the most important process- Lilocked ransomware removal, you need to get anti-malware tool like FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes and wipe the system down. Such software allows to see detected malware and delete all those programs with associated files.
Getting rid of Lilocked virus. Follow these steps
Manual removal using Safe Mode
Activate Safe Mode with Networking to disable malicious Lilocked ransomware
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Lilocked using System Restore
Employ System Restore to bring your computer back to its previous state before Lilocked ransomware
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Lilocked. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Lilocked from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Lilocked, you can use several methods to restore them:
Data Recovery Pro is a tool for data restoring functions
Use this software for bringing your files and data back after Lilocked ransomware encryption
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Lilocked ransomware;
- Restore them.
Use Windows Previous Versions feature for data restoring
If you have used a System Restore, you should give this method a try
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try ShadowExplorer for file recovery
If the virus did not get in time to eliminate Shadow Volume Copies of your encrypted files, you can use this software
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
There is no official decryptor for Lilocked ransomware
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Lilocked and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Michael Gilespie. Vector assumption. Twitter. Social platform.
- ^ Pierluigi Paganini. Thousands of servers infected with the Lilocked Ransomware. Security Affairs. Word Press.
- ^ Anmol Sachdeva. Thousands of Linux servers infected by Lilu(Lilocked) ransomware. Fossbytes. Technology news.
- ^ 26 engines detected this file. Virus Total. File info.
- ^ Jay Gairson. Reply to demonslay335. Twitter. Maztec Status.
- ^ Bedynet. bedynet. Spyware related news.







