.666 (njkwe RaaS) ransomware (Virus Removal Instructions) - Bonus: Decryption Steps
.666 (njkwe RaaS) virus Removal Guide
What is .666 (njkwe RaaS) ransomware?
.666 (njkwe RaaS) is a file-encoder that can be purchased on various underground forums as Ransomware-as-a-service
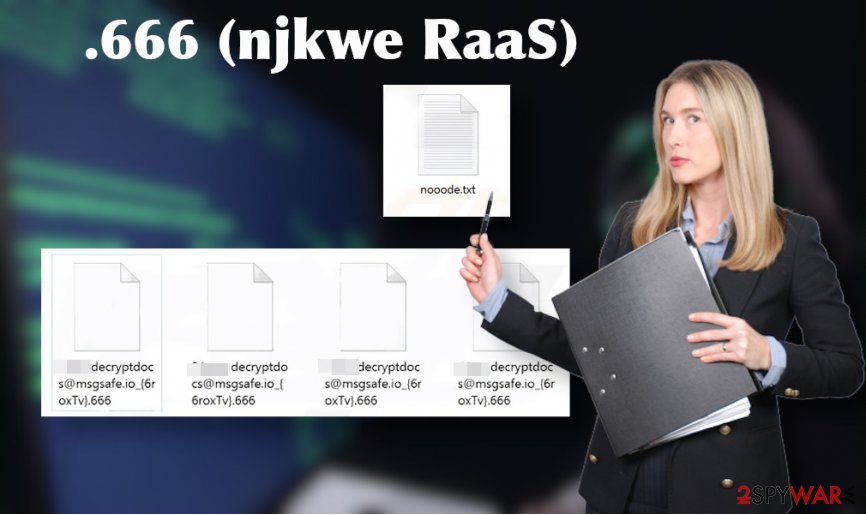
.666 (njkwe RaaS) is the name of a Paradise ransomware variant, which has resurfaced in the midsummer of 2020. The virus takes advantage of the army-grade algorithm RSA-2048 or RSA-1024 to lock the files detected on the infected system. As a consequence, data, such as pictures, photos, Microsoft Office documents, music, videos, etc. become unusable and owners cannot even tell what is in certain documents. All of the corrupted files feature the identical logo and .666 file extension.
The original version of the .666 (njkwe RaaS) ransomware used to append .paradise, .sell, .ransom, .logger, and other file extensions. Nonetheless, this latest variant distinguishes from the others by the .666 file name, nooode.txt ransom note, and new criminal contacts – decryptdocs@msgsafe.io or decryptdocs@firemail.cc.
The .666 file virus is one of few ransomware viruses that can be purchased by wanna-be hackers on the underground forum and with the slight customization become a new Paradise ransomware strain. The so-called Ransomware-as-a-service[1] (RaaS) reduces the need to code malware and creates the group of affiliates that spin the ransomware circle. Therefore, we recommend people to take precautionary measures to protect PCs and laptops from ransomware attacks. Avoid downloading pirated software or opening spam email attachments as they may carry payload-dropper file VgvdhF8ESVZDurYTgkA.exe.
| Name | .666 (njkwe RaaS) |
| Type | Ransomware/file-encrypting virus |
| Related files | VgvdhF8ESVZDurYTgkA.exe |
| Encryption algorithm | RSA-2048 or RSA-1024 |
| File extension | .666 file virus |
| Family | Paradise ransomware |
| Symptoms | All personal files are locked using .666 extension The ransom note can be found on the desktop The system becomes sluggish High CPU consumption can be noticed Random system restarts can occur, etc. |
| Removal | The only solution for getting rid of ransomware virus is to run a full system scan with a robust anti-malware while in Safe Mode with Networking |
| Virus damage | To gain persistence the virus alters various Windows OS settings. It is capable of disabling certain processes, creating new registry keys, or deactivating programs. Thus, right after ransomware removal, experts recommend recovering the system using FortectIntego tool |
The njkwe ransomware is a cyber threat that focuses on file encryption process and money extortion. Therefore, it initiates various background processes to become persistent and successfully launch the encryption software. In case of success, it locks all personal files, and each document, photo, picture, video, or file archive becomes inaccessible.
Encrypted files can be easily distinguished as each of them get the .666 file name. There's no way to open, rename, or move the locked files because they are locked using a strong encryption code, which can be cracked only using a unique decryption key that is stored by criminals.
The decryption key for every victim is unique. A person who is suffering from .666 (njkwe RaaS) virus attack is supposed to email decryptdocs@msgsafe.io or decryptdocs@firemail.cc. The message necessarily has to contain a unique ID number, which is provided on the nooode.txt ransom note. The ID typically consists of six randomly selected characters (e.g. 5xgtHk).
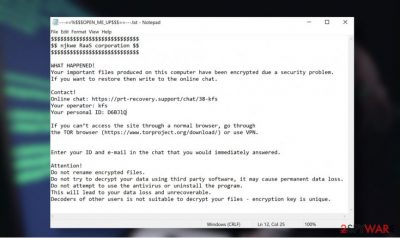
$$$$$$$$$$$$$$$$$$$$$$$$$
$$ njkwe RaaS corporation $$$
$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$
$$ All your information is copied in case of refusal of payment will be sold $$
$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$$WHAT HAPPENED!
Your important files produced on this computer have been encrypted due a security problem.
If you want to restore then write to the by email.Contact!
email: decryptdocs@msgsafe.io
ar
email: decryptdocs@firemail.cc
Your personal ID: –
Enter your ID and e-mail in the chat that you would immediately answered.Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Do not attempt to use the antivirus or uninstall the program.
This will lead to your data loss and unrecoverable.
Decoders of other users is not suitable to decrypt your files – encryption key is unique.
Criminals do not disclose how much money they are expecting to get. The note does not specify the size of the ransom but based on the previous Paradise ransomware variants it's very likely that criminals expect to get a ransom not lesser than $500 in Bitcoins. No matter what size of the redemption is, do not support criminals. Remove .666 (njkwe RaaS) virus from the system and try alternative data recovery methods instead.
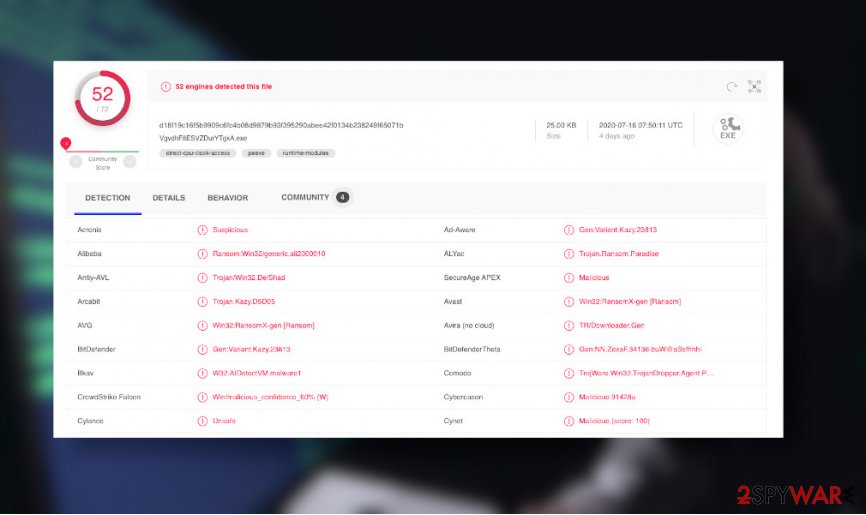
.666 file virus removal requires the usage of a professional AV engine. If you have one installed, update it and run a scan while the system is rebooted into Safe Mode with Networking. The software should inform you about suchlike detection:
- Win32:RansomX-gen [Ransom] (AVG)
- Gen:Variant.Kazy.23813 (BitDefender)
- A Variant Of Win32/Filecoder.Paradise.C (ESET-NOD32)
- HEUR:Trojan-Ransom.Win32.Gen.vho (Kaspersky)
- Ransom_Gen.R002C0WGE20 (Trend Micro)
- Win32:RansomX-gen [Ransom] (Avast)
- TrojWare.Win32.TrojanDropper.Agent.PRQ@8a (Comodo)
- Gen:Variant.Kazy.23813 (B) (Emsisoft)
- Ransom.RaaS (Malwarebytes)
- Trojan:Win32/Ymacco.AAD1 (Microsoft), etc.[2]
Set the anti-virus tool to perform a full .666 (njkwe RaaS) removal and restart the system. After that, scan your machine with FortectIntego utility to fix virus damage and then follow the instructions on how to recover .666 files. You can either use inbuilt Windows features or rely on third-party data recovery tools.
Obfuscated files appended to email spam attachments run the payload droppers
Ransomware is one of the most dangerous cyber threats. Not only because it causes significant losses, but also because it spreads in the most stealthy manner and manages to get inside thousands of machines. Usually, hackers rely on techniques like exploits, brute-force attacks, remote code execution via unprotected RDPs, and similar. In fact, these methods most successfully work for the attacks on businesses and corporations.
The majority of home users' PCs are infected via spam. Professionally-looking emails are often sent to unsuspecting PC users who fall for opening the PDF, Word, Excel, and other forms of attachments believing that these are some kind of forms, order confirmations, or financial information.
The malicious attachments are macro-filled documents[3], so clicking on them activates the ransomware payload, which extracts the malicious executables and activates the ransomware. Once activated, there's no way to deactivate the payload unless you immediately understand that a virus entered the machine and reboot it into Safe Mode. At that time, a full scan might save the day. Anyway, to prevent this from happening, render a powerful spam filter, use a professional AV engine, and be cautious when web browsing because suspicious content can cause damage to the system.
Learn how to remove .666 (njkwe RaaS) file-encrypting virus easily
Njkwe RaaS virus removal is one-sided. There's no other way to get rid of it except run a full system scan with trusted anti-virus software. Ransomware is not a single file or installer. It's a composition of malicious processes, files, registry entries, processes, and others. Therefore, to stop all malicious performance that a cyber infection is capable of initiating, it's imminent to reboot the machine into Safe Mode and then set an anti-virus scanner to perform a full check.
There are many AV programs to choose, though we recommend using SpyHunter 5Combo Cleaner or Malwarebytes tools as both of them are powerful enough to quarantine and delete .666 virus files. The scan process can take some time, so be patient and let the application perform its task.
Upon a full Njkwe virus removal, run a scan with FortectIntego repair tool. Unfortunately, this program won't recover the .666 files. However, it will check the system for virus damage and perform a repair procedure to ensure a smooth PC's performance. The elimination of a virus is not the same as file recovery. Ransomware encrypted files are difficult to restore without working decryption software. Nevertheless, at least some of the files can be restored by running a scan with data Recovery Pro, exporting Volume Shadow Copies, or enabling previous file versions. For more information, follow the tutorial below.
Getting rid of .666 (njkwe RaaS) virus. Follow these steps
Manual removal using Safe Mode
To stop malicious .666 (njkwe RaaS) processes, you may need to reboot Windows into Safe Mode with Networking as explained below:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove .666 (njkwe RaaS) using System Restore
Restoring the system to the previous state may help to recover damaged system components.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of .666 (njkwe RaaS). After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove .666 (njkwe RaaS) from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Although there's no free .666 file decryption key available, cybersecurity experts from NoVirus.uk[4] recommend trying alternative data recovery methods instead of paying the ransom.
If your files are encrypted by .666 (njkwe RaaS), you can use several methods to restore them:
Data Recovery Scanner might help
Data Recovery Pro scan might recover some of the personal files locked by this ransomware. Therefore, give this tool a try.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by .666 (njkwe RaaS) ransomware;
- Restore them.
Windows Previous Versions feature for the rescue after encryption
If you have been using Windows Previous Version feature before, you should try to enable the previous versions of the encrypted files as explained below. This method might take some time as every file has to be recovered separately.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use Shadow Explorer
Shadow Explorer is a tool that might perfectly work in recovering the files encrypted by njkwe ransomware using .666 extension. However, this option can work only if the ransomware does not run a command do delete the Shadow Volume Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official decryptor available.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from .666 (njkwe RaaS) and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Ransomware-as-a-Service (RaaS): How It Works. TripWire. Cybersecurity experts.
- ^ VgvdhF8ESVZDurYTgkA.exe analysis. VirusTotal. Free URL and file scanner.
- ^ Julie Splinters. Macro-less Microsoft Word spam attachments infect users with malware. Ugetfix. A guide on how to fix issues on Mac and Windows OS.
- ^ SECURITY AND SPYWARE NEWS. NoVirus. Virus and spyware news.





















