Removal guide for Default-Search.net redirect
Default-search.net Removal Guide
What is Default-search.net?
Default-search.net – a browser hijacker which sometimes comes together with Linkey ads
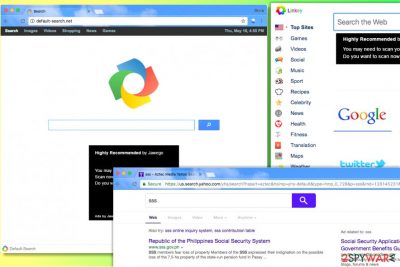
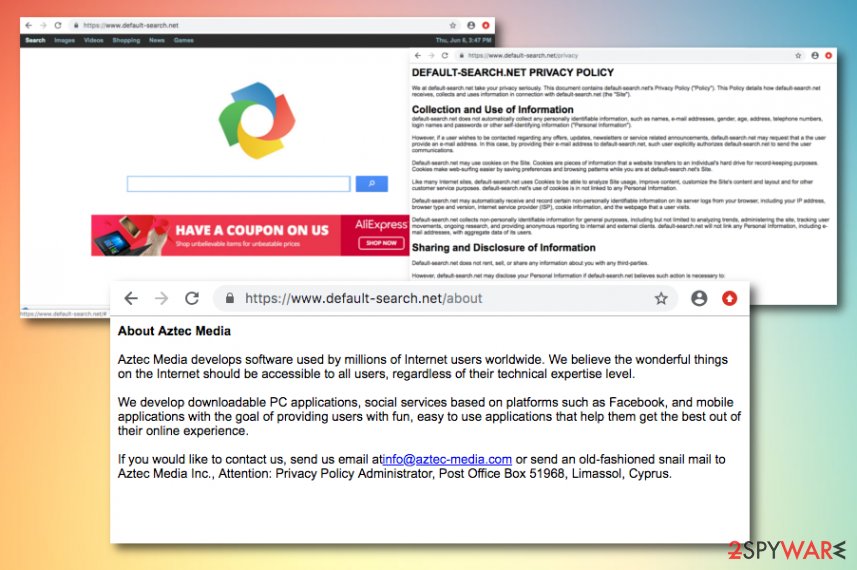
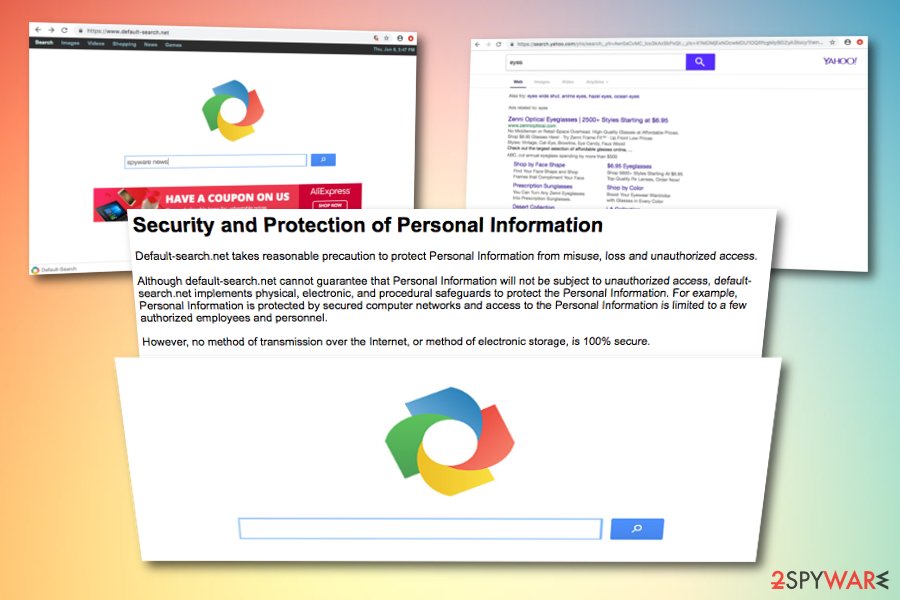
Default-search.net is a browser hijacker[1] that sets Default-search page as default start and new tab page in all web browsers. It usually arrives together with Linkey adware[2] or even Delta-Homes[3], and both of these are known to be incredibly sneaky spyware-type programs. Furthermore, Default-search.net appears to be associated with System Manager and these two applications have the same developer – Aztec Media, Inc. The browser hijacker takes control of main web browsers and makes them trigger redirects to http://www.default-search.net/ site every time the user wants to open a new blank page in the browser.
Default-search.net engine delivers deceptive Yahoo search results altered by Aztec Media, Inc. These search results are filled with bogus links that do not raise any suspicions when you first look at them. However, clicking on results brought by this dangerous search tool can immediately throw you onto hazardous websites[4] that you typically try to avoid visiting.
| Name | Default-search.net |
|---|---|
| Type | Browser hijacker |
| Developer | Aztec Media, Inc |
| Arrives with | Linkey adware and Delta-Homes |
| Search results | Yahoo |
| Activities | Redirecting, advertising, collecting browsing data |
| Distribution | Third-party apps, infectious hyperlinks |
| Removal | The elimination can be completed with FortectIntego |
Here are other unpleasant activities that can be performed by Default-search.net:
- The hijacker implements URL redirections in order to point web traffic to particular sites and generate pay-per-click revenue. You must be careful and not click on ads and sponsored links presented by this dubious search tool or you might end up visiting malicious or simply untrustworthy websites.
- Besides, to increase the probability of desired events, the hijacker employs various tracking technologies such as cookies and web beacons that help to collect and store particular data about the user's interests. Typically, Default Search hijacker collects victim's search queries, URL requests, the list of downloads, IP address and similar data.
- Collected data is used to provide ads based on content that the victim usually explores. The attacker affects overall computer's performance, therefore the computer becomes slow and causes unpleasant occurrences such as browser crashes.
Although browser hijackers such as Default-search.net are not created to track personal data, anything can happen while using third-party questionable apps. If you read this program's privacy policy, you will find out that the developers are not sure if personal information of users will be safe at all times even though they claim to take some safety measures:
Although default-search.net cannot guarantee that Personal Information will not be subject to unauthorized access, default-search.net implements physical, electronic, and procedural safeguards to protect the Personal Information. For example, Personal Information is protected by secured computer networks and access to the Personal Information is limited to a few authorized employees and personnel.
Experts inform to remove Default-search.net as soon as possible because it is considered to be a critical browser hijacker that in unison with Linkey completely disrupts computer's performance[5]. If you noticed these programs in your system, immediately run a system scan using reputable anti-malware software. For best results, our team suggests using the FortectIntego software.
Unfortunately, Default-search redirect virus usually comes in a bundle with Linkey software. When infected with these programs, users can find various suspicious files in their system, for example, a program called Settings Manager which we have mentioned before. Experts advise removing not only these programs, but also other suspicious ones because Linkey reportedly can be using different names to hide on the computer system.
Once this filthy adware gains control of the victim's computer and browsers installed on it, the victim shortly starts seeing Linkey Deals when browsing through the Internet. The user might also experience redirects to linkeyproject.com site. The aforementioned ads typically pop-up on the screen when the user stays on the same website for a couple of seconds.
In most cases, they emerge in the form of banners that have Linkey logo on them. Try to avoid clicking on those banners until you complete Default-search.net removal with anti-malware software, which will also remove Linkey's components at the same time.
To sum up, no matter that Default-search does not belong to malware category, it poses a threat to the computer because sponsored content that it provides can link to highly dangerous sites (such as phishing sites) that might attempt to swindle personal information from you or force you to install critical programs.
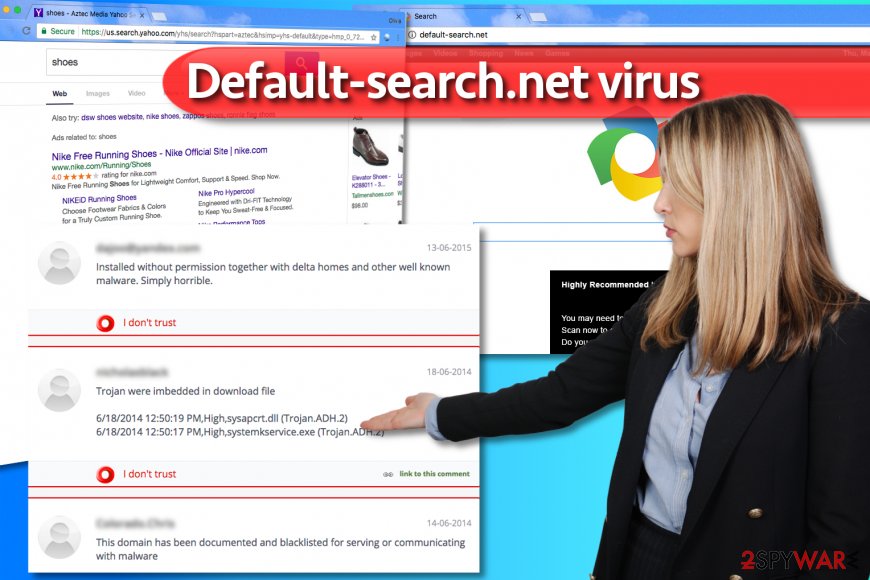
Windows 10 and Chrome users among the primary hijacker's targets
Experts from 2-Spyware have received a lot of questions from Windows users whose computers were compromised by the infamous browser hijacker. It seems that computer users can't remove default-search.net from Chrome browser despite their attempts to identify the hijacker on Windows 10 computer systems. Most of these reports came from Chinese[6] and US citizens.
However, it doesn't mean that other operating systems are resistant to this virtual threat. It can affect almost every Windows version and Mac operating systems as well.
To find out how to remove http://www.default-search.net/?sid=712&aid=59002, we recommend reading instructions added to this article. They were prepared by experienced IT experts who discovered a way to push the annoying hijacker out of the system.
NOTE. The spyware programs described in this article are known to be sneaky and versatile, so it is possible that their developers might be changing their distribution techniques and from time to time. What is more, you might not succeed in finding these programs on your system because their developer might be using different names for them.
If you are unsure how to block http://www.default-search.net/?sid=712&aid=59002 for good, consider using automatic spyware removal software that will identify the culprit causing those browser redirects and remove it for you.
Sneaky browser hijacker distribution tactics
Browser hijackers are spread using an unfair distribution method, which is known as “bundling” and is closely related to freeware and shareware. However, it is not difficult to avoid infiltration.
- Remember to read Privacy Policy and End User's Agreement when installing freeware to your computer;
- Avoid Recommended or Quick options when choosing installation settings;
- Instead, select Advanced or Custom installation mode and uncheck all pre-checked checkboxes that claim:
“Make Default-search my default search engine”, “Make Default-search.net my start page”, etc.
It becomes clear that you just need to pay more attention to the information provided by free software installers and you will easily avoid this browser hijacker. If you think that you have missed this check mark that allows installation of it, you should be very careful when browsing on the web. Please, try to avoid its corrupted search engine and ads that may try to pop on the screen during your browsing sessions.
Professional Default-search.net removal help
If you were tricked into installing these highly dangerous spyware examples, remove Default-search.net virus along with Linkey and other PUPs at once by running a thorough system scan with a powerful malware removal tool. As we said, you can use programs listed below the article or try to identify and delete dangerous files by yourself.
However, if you are an unskilled computer user, you should not try to deal with these programs on your own because your attempts to complete Default-search.net removal might result in failure. To gather all of the critical files, registry entries and helpers that keep this dangerous software on your system, employ a professional anti-malware software.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Default-search.net. Follow these steps
Uninstall from Windows
To completely uninstall Default-search.net from Windows along with its companions, use this tutorial and uninstall the following programs and all others that are named similarly: Delta-Homes, Linkey, Linkey Deals, Settings Manager.
After uninstalling all of these programs, fix infected browser shortcuts using further instructions. You need to delete suspicious URLs added to each browser shortcut's Target field.
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Follow the provided instructions and eliminate all of hijacker's remains from Firefox. If you want to be sure that all spyware components are deleted, refresh Firefox after carrying out these guidelines.
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
Chrome browser should contain several extensions that are responsible for serving bothersome ads and causing redirections to linkeyproject.com and other suspicious websites. Delete every extension that appears suspicious to you! For best results, reset Chrome.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Default-search.net registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ What Is Browser Hijacking?. Kaspersky Lab. Resource Center.
- ^ Trojan.Semnager. Symantec Security Response. Virus Definitions & Security Updates.
- ^ Delta-Homes.com. How to delete? (Removal tutorial). NoVirus. Information about the Latest Computer Viruses and Malware Removal Guides.
- ^ How to Avoid Malware. Northeastern University. Information Security News and Updates .
- ^ Is default-search.net Safe? Reviews & Ratings. MyWOT. Website Reputation Ratings.
- ^ Wubingdu. Wubingdu. Malware Removal Help.























