FireCrypt ransomware / virus (Tutorial) - Improved Instructions
FireCrypt virus Removal Guide
What is FireCrypt ransomware virus?
Key information FireCrypt ransomware
FireCrypt virus has attracted IT experts‘ attention since it is no ordinary file-encrypting threat. Observing the tendencies, IT analysts have already predicted the rise of crypto-malware threats [1]. Likewise, hackers rush to meet such expectations. In comparison with other viruses launched recently, this malware contains additional features. While the case of Vindows Locker reverberated throughout the community when ransomware tried to disguise as a tech support scam, the current threat is set to perform (distributed-denial-of-service) DdoS attacks [2]. In this article, you will find more information on how to battle this threat and remove FireCrypt. Do not waste time and start the elimination process with FortectIntego.
The malware attempts to paralyze the efficiency of the device with a poor DDoS attack. What is more, it employs a sophisticated AES-256 algorithm to lock out the files. That is how the racketeers ensure that their virus is not easily taken down. The exquisite code lowers the chances of generating a decryption key. Since the developer combined two methods to create this tool: software and strings of multiple source codes. Such method granted the creator more flexibility. Moving on, the employed application, known as BleedGreen, creates a unique ransomware executable. Furthermore, the builder provides a disguise for the executable. In other words, the .exe binary will be entitled as a .doc or .png file.
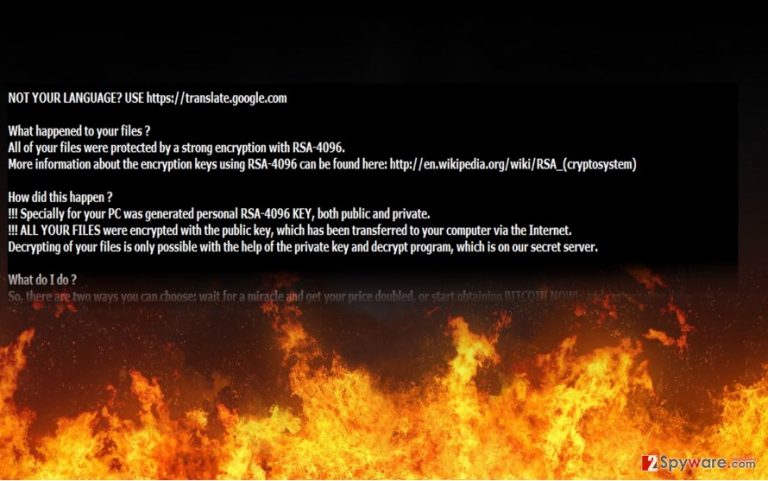
The ransom note immediately gives out an impression that FireCrypt malware is the misdeed of a teenager. It contains uncensored text and skulls which have been a common image for computer viruses. After it settles on the device, FireCrypt ransomware terminates Task Manager processes. Likewise, more experienced computer users fail to interfere with the processes. Speaking of the title, it was called so since it appends .firecrypt file extension. Later on, it will leave its ransom file on the desktop. It comes in two formats – READ_ME.txt and READ_ME.html files. MalwareHunterTeam, which was first to track the cyber infection, concluded that the virus has a striking resemblance to another malware – Deadly For a Good Purpose virus.
Besides the similar ransom note, the source codes bear similarities, and bitcoin addresses lead to the same address. .firecrypt file extension virus demands 500 dollars in exchange for the files. It also urges victims to remit the payment as soon as possible before the decryption key is deleted. Time limits have been a popular way to scare users. Recently, some hackers decided to play even dirtier and encourage its victims‘ to receive the decryption key by infecting their friends [3]. In this case, the malware does not ask you to do so. Nonetheless, you should not do so as the decryption key is not stored and it is pointless paying the money. There have been attempts to combat the growing business. One of the recent ones, specifically in California, rules that a ransomware creator might be sentenced to imprisonment up to four years. Tracking the perpetrators remains a challenge [4]. Meanwhile, ordinary users must find alternative ways to combat ransomware. After you complete FireCrypt removal, scroll down to the very bottom of the page to see some file recovery suggestions.
The transmission peculiarities of the ransomware
Knowing its distribution tendencies is no less important that being aware of the termination characteristics. The current ransomware is quite new so little is known about its transmission peculiarities. Regarding the fact that the crook disguises the binary under .doc or .png file, it is most likely to spread via spam emails. The latter has been common for transmitting ransomware. Similarly, FireCrypt hijack took pace. You might be interested in the possible ways how to reduce a number of spam messages [5]. Note that hackers devise an elaborate technique to lure users into their trap by sending emails presented as fake tax refund notifications or invoices.
How long does it take to remove the virus?
Time is a crucial factor in eliminating crypto-malware. For an effective FireCrypt removal use an anti-spyware application (FortectIntego or Malwarebytes). The software also comes as practical utility detecting and eradicating less serious files. After you remove FireCrypt virus, proceed to data recovery. More information is provided below. Lastly, you should keep in mind that malware might lurk in torrent sharing or web pages overcrowded with fake download buttons. While you are installing new programs, advance attentively not to install questionable installers and download accelerators.
Getting rid of FireCrypt virus. Follow these steps
Manual removal using Safe Mode
If you find it difficult to complete the elimination process, use these instructions to regain the access to the computer.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove FireCrypt using System Restore
System Restore might be another solution.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of FireCrypt. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove FireCrypt from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by FireCrypt, you can use several methods to restore them:
Opting for Data Recovery Pro
This tool helps retrieve missing and locked files after an unexpected system crash. It contains a simple and clear manual.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by FireCrypt ransomware;
- Restore them.
The usefulness of ShadowExplorer
This tool recreates the files using shadow volume copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from FireCrypt and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Ian Barker. Ransomware set to increase in 2017. Betanews. Technolohy News and Analysis.
- ^ What is a DDoS Attack?. Digital Attack Map. Top daily DDoS attacks worldwide.
- ^ Christine Kern. New Ransomware Forces Victims To Spread Virus For Key. Business Solutions. Growth Strategies for the IT channel.
- ^ Greg Masters. Ransomware crime bill goes into effect in California. SC Media. The Cybersecurity Source.
- ^ Jack Schofield. How can I stop spam emails?. The Guardian. World and UK News..







