Vindows Locker (Removal Guide) - updated Dec 2016
Vindows Locker Removal Guide
What is Vindows Locker?
3 main facts you should know about Vindows Locker ransomware
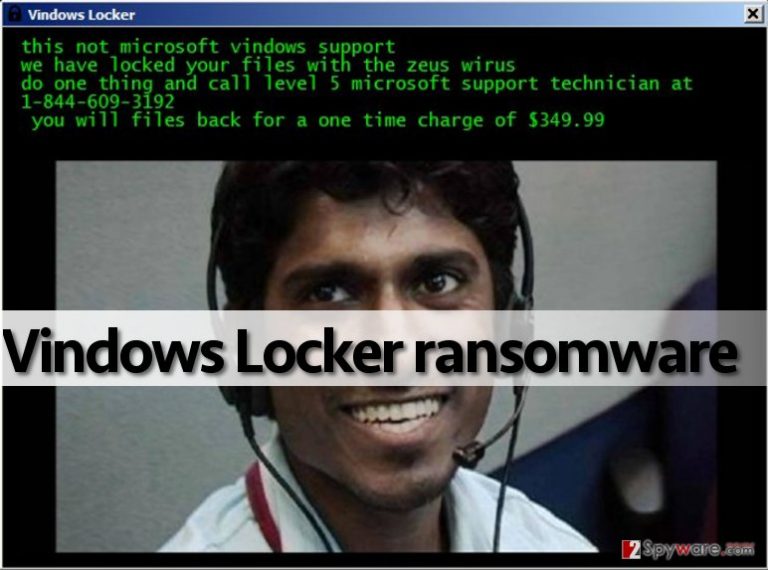
Vindows Locker ransomware is not a typical file-encrypting infection. After looking at it closer, you can see that it resembles a Tech Support Scam virus which aim is to trick users into thinking that their PC system is infected and that they need to contact the special tech support. However, this malware is actually considered to be the ransomware-type parasite because it can also encrypt your files and ask you to pay the special ransom. Besides, Vindows Locker virus can also initiate a lock screen imitating the attack of Zeus malware [1] on your computer’s desktop. This old trojan horse is really dangerous, so its appearance on the system can threaten almost every PC user that he or she needs to dial the special number (1-844-609-3192 in this case) and pay $349.99 to fix the computer.
When infected with Vindows Locker, you can see how many files it can affect. The list of files includes photos, videos, documents, music, databases, and more. All affected files have .vindows file extension appended right after the original file extension. They can’t be opened, so you can find yourself in a big trouble if these documents are your business files or similar data which is considered important. Later on, the ransomware displays a huge window named “Vindows Locker” which provides the following information:
This not microsoft vindows support
We have locked your files with the zeus wirus
Do one thing and call level 5 microsoft support technician at 1-844-609-3192
You will files back for a one time charge of $349.99
This message is very confusing because criminals deny themselves in it. Firstly, they state on their warning message that “this is not Microsoft Windows support”. However, then they encourage people to contact “level 5 Microsoft Windows support technician” and pay the money. What is more interesting is that, unlike typical ransomware-producing criminals, authors of this particular malware do not ask people to buy Bitcoins and transfer them to a certain wallet [2]. They want you to provide your credit card details and buy some suspicious services over the phone. This is primarily why this virus reminds us of Tech Support Scam viruses. However, these infections do not normally encrypt victims files. It means that tech support scammers have improved their filthy games and started to apply more aggressive methods to extort cash from computer users.
If the window of Vindows Locker ransomware popped on your screen, you should know only one thing – your PC has been attacked by criminals, who distribute a malicious program over the Internet and seek to convince inattentive computer users to download and install it. Therefore, it is right to say that it spreads like a Trojan horse. Keep in mind that this virus might come along other malware example, so to completely clean your system, you must use proper malware removal tool. Use your antivirus or download one of our recommended programs (for instance, FortectIntego or SpyHunter 5Combo Cleaner) to properly remove Vindows Locker and related malware from the system. Before you start Vindows Locker removal procedure, reboot your PC in a Safe Mode with Networking. To find out how to do this, read instructions provided further.
November 2016 update:
In November 2016, security experts from Malwarebytes Lab found a crack in Vindows Locker ransomware code and come up with a working decryption tool [3]. However, according to experts, their tool should be used only on the infected machine – if transferred to some other environment, it will not be functional. However, you can download Vindows Locker decrypter for free and try it on your infected computer just by clicking the link provided at the end of the article. If you don’t want to install anything, you can also try data recovery instructions provided by 2-spyware experts. In this case, you should remove its files at first. Then you should perform steps given in “Data Recovery” section.
Ransomware uses system vulnerabilities to infect computers
If you have been infected with .vindows file extension virus, you should remember what files or programs you have recently installed. Have you visited suspicious websites lately?[4] Have you been asked to install some updates, applications, or download some questionable files? Maybe you have received a vague email lately and opened files attached to it? There are many locations where you can catch the malicious Vindows Locker payload and “help” it infect your computer system, and sadly it happens very frequently because scammers manage to obfuscate malicious viruses and make them appear secure. This is why such threats sometimes manage to bypass antivirus protection. Therefore, you should keep your anti-malware software up-to-date, avoid visiting shady Internet sites, install freeware using Custom or Advanced options only, and never open questionable email letters that carry attachments or contain shady hyperlinks because they can involve you to phishing attacks [5]. Clicking on them and opening them can unleash the Vindows Locker malware and severely damage your computer system!
Things to remember about Vindows Locker removal:
If this tech support scam virus-like ransomware has infected your PC, and now you see a picture of an indian hacker on your screen, do not panic. You shouldn’t pay such amount of money to criminals, which most likely will not help you to recover your files. So instead of searching for your wallet, remove Vindows Locker virus using anti-malware programs. Do not try to carry out Vindows Locker removal manually unless you are an expert in programming. Otherwise, follow these instructions to start your computer in a Safe Mode with Networking and start wiping malicious files with the help of anti-malware software.
Getting rid of Vindows Locker. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Vindows Locker using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Vindows Locker. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Vindows Locker from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Vindows Locker, you can use several methods to restore them:
Advantages of Data Recovery Pro
Install Data Recovery Pro, which is great tool for data recovery. If your files have been locked, you can try to recover them by following these steps:
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Vindows Locker ransomware;
- Restore them.
Advantages of Windows Previous Versions
If you have enabled System Restore mode a while ago, now you can take advantage of it and recover original file examples. Follow the guidelines below.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Advantages of the ShadowExplorer
ShadowExplorer is a software that helps automatically recover files using their Volume Shadow Copies. Of course, most of the ransomware creators make sure that these backup files are deleted from the computer. Nevertheless, you can always give this method a try. Here is what you will have to do:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Vindows Locker decryptor
Malwarebytes team has released a Vindows Locker decryption tool that significantly facilitates the task of the data recovery. You can download the decrypted by clicking the previously indicated link. If the utility fails to recover files and does not eliminate .vindows extensions, feel free to use the aforementioned data recovery techniques.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Vindows Locker and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ What is Zeus (malware). Wikipedia, the free encyclopedia.
- ^ How to Store Your Bitcoins. CoinDesk, the world leader in news and information on digital currencies.
- ^ Tech support scammers up their game with ransomware. Malwarebytes Labs.
- ^ Jessica Dolcourt. 9 tips for avoiding suspicious Web sites. Cnet. The download blog.
- ^ Prevent . Google Support Page.







