OpenToYou ransomware / virus (Recovery Instructions Included) - Free Instructions
OpenToYou virus Removal Guide
What is OpenToYou ransomware virus?
What happens when OpenToYou virus hijacks your PC?
OpenToYou virus is new ransomware detected in the last days of the 2016 year. Regarding its ransom message, it does not convey a sophisticated impression. Nonetheless, it should not be the reason to underestimate it. According to the acquired information, it is the virus which belongs to the series of @india.com crypto-malware. The developer or a group of cyber criminals responsible for these infections have been in the ransom market already since the beginning of last year and continuously releasing one or two viruses in the fortnight. In general, ransomware has become quite an issue since the emergence of Locky and Cerber virus [1]. But their terror attacks have been backed with the threats created by this cyber gang. In any case, if this virtual misfortune has befallen you, there is no need to panic. What you need to right now is to remove OpenToYou. For that, you can use FortectIntego.
File-encrypting viruses may not be such a problem if not for their specific features. Every user who encountered this cyber infection is presented with a dilemma. Even when the threat is eliminated, the files remain encrypted. The strength of crypto-malware lies in the ability to encode files with complex encryption algorithms [2]. There is a variety of them, but mostly AES and RSA are used. Since the most viable way to decrypt the files is to acquire decryption key, the hackers scare users into purchasing their Decryptor or the key to unlocking the files. What is more, publications of open source file-encrypting [3] threats also contribute to the activity of this type of viruses. Specialists suspect that the attacks of crypto-malware threats may only increase in 2017 [4]. However, data retrieval is uncommon despite the overall high numbers of ransomware viruses. Thus, even if opentoyou@india.com file extension virus has encoded your files, there are few chances that the crooks will return the files. Thus, concentrate on the elimination of the threat. More information is provided in the final section of the article.
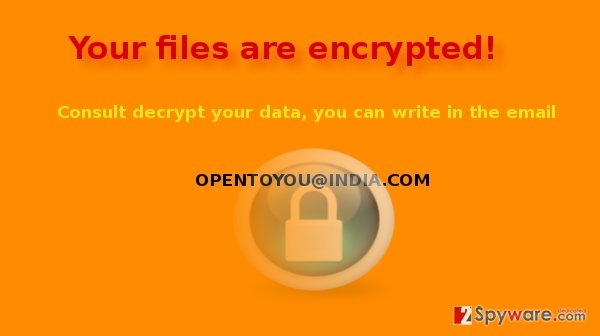
Speaking of the peculiarities of OpenToYou malware, the ransomware does not possess any exceptional characteristics. It attaches -opentoyou@india.com extension to the locked files. When the encryption process is complete, a victim finds !!!.txt file on the desktop which suggests victims to contact the hackers using the email address:
Your files are encrypted!
To decrypt write on email – opentoyou@india.com
When the threat sneaks into a device?
OpenToYou@india.com hijack may take place through different channels. The most popular of them remains spam emails. Though in some cases you might consider getting revenge on a spammer who tries to fools you with the fake winning of a lottery, nowadays such emails possess corrupted attachments [5]. If you open them out of curiosity, you may end up with ransomware on the device. Beware of exploit kits and trojans as well. In comparison with the former method, it is nearly impossible to detect it without the assistance of security applications. Usually, they dwell in torrent or file-sharing domains.
Is it possible to eliminate the virtual infection completely?
In the case of a file-encrypting threat, we recommend installing an anti-spyware application. Updating it before the scan is of key importance since the outdated version may fail to detect the binary of OpenToYou ransomware. Recent malware elimination utilities, such as FortectIntego or Malwarebytes, eradicate the threat completely. It does not take too long for either tool to remove OpenToYou virus from the computer. However, data decryption is a different matter. Some of the alternative suggestions are provided below.
Getting rid of OpenToYou virus. Follow these steps
Manual removal using Safe Mode
If you struggle with OpenToYou removal, the cause might be the modified settings of the device. Some ransomware threats lock computer screen. Likewise, these instructions will help you regain access and then continue with the elimination procedure.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove OpenToYou using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of OpenToYou. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove OpenToYou from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by OpenToYou, you can use several methods to restore them:
The benefits of Data Recovery Pro
If you do not have a backup of your files at hand, this tool might be one the last solutions.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by OpenToYou ransomware;
- Restore them.
Opting for ShadowExplorer
The essence and key advantage of this application lie in recreating the files based on shadow volume copies. They are automatically created by every Windows OS. If ransomware does not access them beforehand, you might succeed in acquiring lost data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from OpenToYou and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ City residents fall prey to ransomware attacks. The Tribune. Voice of the People.
- ^ Contel Bradford. 5 Common Encryption Algorithms and the Unbreakables of the Future. StorageCraft. Backup and Disaster Recovery Blog.
- ^ Karsten Hahn, Tilman Frosch. It's Educational - On the No 1 Argument for Open Source Ransomware. G Data Security Blog.
- ^ Ian Murphy. SecureWorks sees 2017 held to ransom. Enterprise Times. A mix of news, features, blogs and podcasts covering the information technologies used by enterprises.
- ^ Jess Bolluyt. 7 Hilarious Ways You Can Get Revenge on Spam Emails. CheatSheet. Gear and Style.







