Polski ransomware / virus (Removal Guide) - Aug 2017 update
Polski virus Removal Guide
What is Polski ransomware virus?
Polski ransomware variants emerge one after another
Polski virus is a computer virus that targets one particular Central-European country – Poland[1]. It infects the system to render all files useless and append .aes file extensions to them. Additionally, the malware leaves a ransom note that provides the sum of money that cyber extortionists demand – a ransom. The ransom note is called !!! – – ODZYSKAJ-PLIKI – – !!!.htm.
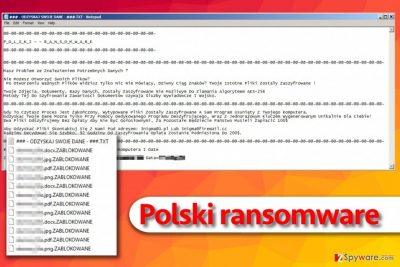
Later versions of the Polski ransomware use .ZABLOKOWANE extensions and ### – ODZYSKAJ SWOJE DANE – ###.TXT file as a ransom note. Cyber security experts agree that this new version belongs to Vortex ransomware group.
While English-oriented crypto-malware dominates in the market, a higher number of more “multicultural” viruses emerge. A while ago, a Malaysian virus has been detected. Usually, the main targets remain the same: it's the Unites States, Germany, France, UK, and other economically developed countries.
However, initiatives from hackers of other nationality have been emerging. For example, Czech ransomware rampaged on the web. Now Polish-speaking netizens became a new target. According to the ransom note, the developers sympathize with the notorious CryptoLocker[2] as they refer to this threat in the end.
The design of this threat does not remind of the mentioned-virus. However, its functionalities are certainly alike. However, it does not mean that even if you are infected with this malware, you can give into distress. Firstly, remove Polski and then consider recovering your affected files. As for the elimination, we recommend using FortectIntego.
It is likely that the malware targets Polish computer users, but not limited. This time the racketeers provided an extensive ransom note. Though all file-encrypting viruses operate in the same way, each of them possesses slight modifications[3]. Speaking of Polski malware, it exploits AES-256 algorithm to encode users’ data.
In the !!! – – ODZYSKAJ-PLIKI – – !!!.htm and !!! – – ODZYSKAJ-PLIKI – – !!!.txt ransom notes, the developers make quite an introduction to ransomware specifications. It even delivers several links to media articles about commonly known crypto-malware. Below, you can see the first lines of the ransom note.
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
P O L S K I R A N S O M W A R E
@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@
###########################################Nie możesz znaleźć potrzebnych plików na dysku twardym ?
Zawartość Twoich plików jest nie do otwarcia?
It is suspected that all the decryption keys are located in a distant command and control servers as two temporal email addresses are given: rsapl@openmailbox.org and estion@sigaint.org. The virus also leaves its mark by appending .aes and .aes256 file extension to the encrypted files. Instead of an ID number, the cyber villains suggest typing 61621122 in the “Subject” box.
Another common feature – encourage victims to pay by offering to decrypt a couple of files for free. As common for CryptoLocker, the hackers urge the users to hurry up with the transaction.
According to the note, after 72 hours the ransom will double. The initial sum remains to be 249 USD[4]. Despite the alerts, there are no guarantees that the crooks will play fair and return the data. Instead, focus on Polski removal.
New version of Polish ransomware emerges in summer of 2017
On August 7, 2017, cyber security researchers spotted a new version of Polski virus that uses different file extensions to mark encrypted files and also a freshly composed ransom note. The very first look at the virus reveals that it uses AESxWin tool (available on GitHub) to encrypt victim's files. The virus presents a slightly different ransom note (called ### – ODZYSKAJ SWOJE DANE – ###.TXT):
@@-@@-@@-@@-@@-@@-@@-@@-@@
P_O_L_S_K_I – – R_AN_S_O_M_W_A_R_E
@@-@@-@@-@@-@@-@@-@@-@@-@@
Masz Problem ze Znalezieniem Potrzebnych Danych?
Nie Możesz Otworzyć Swoich Plików?
Po Otworzeniu Ważnych Plików Widzisz Tylko Nic Nie Mówiący, Dziwny Ciąg Znaków? Twoje Istotne Pliki Zostały Zaszyfrowane !
Twoje Zdjęcia, Dokumenty, Bazy Danych, Zostały Zaszyfrowane Nie Możliwym Do Złamania Algorytmem AES-256
Metody Tej Do Szyfrowania Zawartości Dokumentów Używają Służby Wywiadowcze I wojsko.
The ransomware suggests writing to 3nigma@0.pl or 3nigma@firemail.cc for data recovery instructions. Clearly, the virus authors want a ransom from the computer user, although we do not recommend listening to their demands. They ask to pay $100 or $200 if the victim fails to pay within 92 hours. Instead of paying the ransom, we suggest you to remove the virus and check data recovery solutions we provided under this article.
Common ransomware infiltration methods
Usually, the majority of crypto-malware spread via spam emails. Crooks manifest their mastery by counterfeiting emails of official institutions. After noticing an email which is supposedly sent from the FBI or transportation agency, users rarely consider them suspicious.
The very malware resides in a .zip folder, .js or executable file. What is more, ransomware may await for new victims disguised in an exploit kit.
Speaking of Polski ransomware attack, it may occur as a result of using text messaging program called Gadu-Gadu. Malvertising is also an option. In short, boost up your computer security by regularly updating crucial system applications and then improve the general security of the computer by installing anti-virus and anti-malware programs. This combination will also help you decrease the number of spam emails and, likewise, decrease the risk of encountering a cyber menace[5].
Eliminate Polski ransomware with ease
When it comes to crypto-malware, it would be better not to waste time and start Polski removal immediately. You can do it with FortectIntego or Malwarebytes. Time is crucial as every spent minute might give the virus more chances to inflict greater damage[6].
After you successfully remove Polski virus, you can take a look at data recovery instructions. It is unknown whether the virus deletes volume shadow copies so you might stand a chance recovering the files. If you encounter any obstacles, feel free to use the below-displayed guide. Lastly, you may attempt terminate the malware by ending its task commands in Task Manager.
Getting rid of Polski virus. Follow these steps
Manual removal using Safe Mode
Can't launch an anti-malware program? Follow these steps to regain control of the device.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Polski using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Polski. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Polski from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Polski, you can use several methods to restore them:
Opting for Data Recovery Pro
If you failed to back up your files, this program might become one of the last solutions.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Polski ransomware;
- Restore them.
Try Windows Previous Versions function
If System Recovery was previously enabled, you might succeed in recovering the latest autosaved copy of a file. However, this method may take some time.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer method
They key advantage of this app is that it restores the files based on shadow volume copies. It is unlikely that the virus deletes these copies beforehand so you get another chance to recover important data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Polski and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ UsunWirusa. UsunWirusa. Malware Removal Guides, CyberSecurity News.
- ^ Antonios Papadimitriou. CryptoLocker Ransomware Is on the Rise — Here’s What to Do if You’re Attacked. SecurityIntelligence. Analysis and Insight for Information Security Professionals.
- ^ Ericka Chickowski. 10 Shocking New Facts About Ransomware. Dark Reading. Protect the business - enable access.
- ^ Herb Weisbaum. Ransomware: Now a Billion Dollar a Year Crime and Growing. NBC News. Breaking News and Top stories.
- ^ Jonathan Sander. Fighting Ransomware In A New Year With The Same Best Practices. Identity Week. Cyber Security News and Analysis for the IT Community.
- ^ Want to Sell More Ransomware Protection Solutions? Follow These Five Steps. The Var Guy. VAR, MSP, and Solutions Provider News.





















