Vortex ransomware / virus (Removal Instructions) - updated Apr 2018
Vortex virus Removal Guide
What is Vortex ransomware virus?
Vortex ransomware – crypto malware that is still actively infecting users
Vortex ransomware is a dangerous crypto-virus[1] which is believed to belong to Polish hackers. The original variation of this ransomware is called Polski ransomware. The file-encrypting threat employs AES-256[2] cipher to encode victim’s photos, documents, videos, and other potentially important data. When encrypting files, the malware adds .aes file extension to every file affected file. All three variations: Vortex, Polski, and Flotera are known to append the same extension.
| Name | Vortex ransomware |
|---|---|
| Variations | Polski, Flotera |
| Ransom note | JAK-ODZYSKAC-PLIIKI.txt |
| File extension | .aes |
| Detected as | Trojan.Ransom.Vortex, TR/FileCoder.mshfm, Trojan.GenericKD.5465013 |
| Email addresses | rsapl@openmailbox.org, polskiransom@airmail.cc, Hc9@2.pl, Hc9@goat.si. |
| Removal | To get rid of ransomware, we recommend usinf FortectIntego or Malwarebytes. Then, proceed to data recovery. |
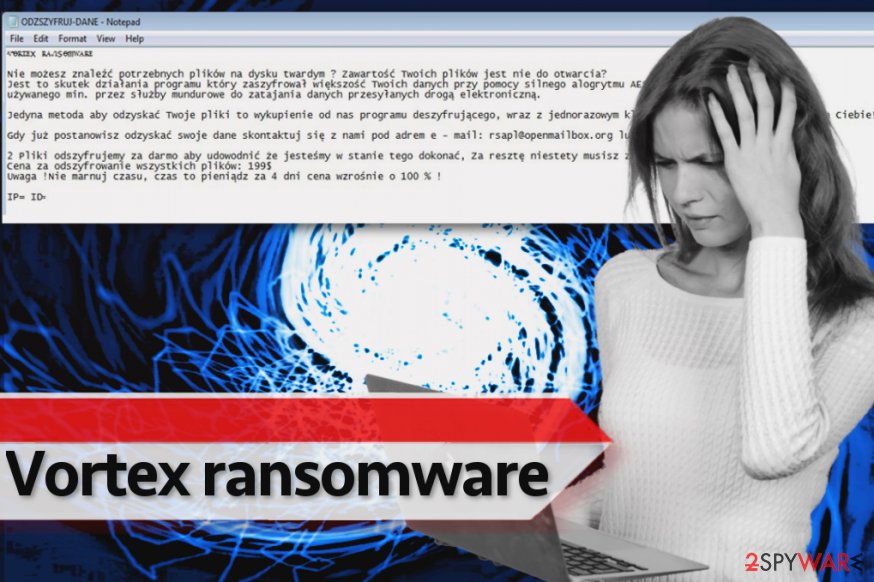
Vortex virus corrupts files in all computer drives but skips system folders to keep the computer running. Once the virus is done with the encryption process, it immediately saves some text into a ransom note, which it names as ODZSZYFRUJ-DANE (stands for DECRYPTION DETAILS in the English language). It also gets a random 40-char password from sethcardoza[.]com/api/rest/tools/random_password_generator/length:40/complexity:alphaNumeric site.
The latest version of Vortex ransomware reportedly uses #$# JAK-ODZYSKAC-PLIIKI.txt name for the ransom note. In this text file, the virus calls itself P_o_l_s_k_i – – r_a_n_s_o_m_w_a_r_e. It demands $100 as a ransom (if the victim pays immediately) or $200 after 4 days.
The first signs of the malware were detected in March, 2016. However, after a month, researchers noticed a hike in its activity again. Flotera ransomware uses the same ransom note and file extension to mark affected files. It exclusively targets Polish[3] users.
The virus subsided for a couple of months, but it got active again in summer months, particularly, June, 2017. The virus hides under pg_ctl.exe or any other randomly named file. Most of anti-virus tools detect the threat as Trojan.Ransom.Vortex, TR/FileCoder.mshfm, and Trojan.GenericKD.5465013, etc. It is not recommended to pay the ransom as the decrypter is already created.[4]
Vortex virus does not create any fancy-looking .html-based ransom notes like Spora virus does[5]. It simply saves the information in a simple .txt file and drops it on the desktop. It is possible that such ransom notes are stored in every folder with encrypted files, too.
It turns out that Vortex ransomware virus wants to get $299 from the victim in exchange for a decryption tool. It provides two email addresses for the victim and asks to write to them to get further instructions regarding data recovery. This crypto-virus is associated with these email addresses: rsapl@openmailbox.org, polskiransom@airmail.cc, Hc9@2.pl or Hc9@goat.si.
According to the ransom note, the victim has four days to get in touch with the criminals and pay the money they demand; otherwise, cybercriminals promise to lift the ransom price by 100%. We do not recommend you to deal with cyber terrorism by following cybercriminals’ commands. You should not pay the ransom, especially because the chances of recovering your files are low.
Even if you paid, you would get no guarantees regarding data restoration[6]. Since your files are encrypted, there is nothing you can do to force cybercriminals to help you. Therefore, instead of writing a letter to ransomware developers, remove Vortex ransomware with FortectIntego or another trustworthy anti-malware software. If you have never experienced a ransomware attack, read Vortex virus removal instructions first.
You can find the instructions right below the post. It is very important to eradicate all malicious files from PC because leaving some ransomware remains automatically makes your system more vulnerable to malicious attacks.
A new look – Flotera ransomware
It seems that Polski ransomware developers have decided to step up their ransomware game one more time and release a slightly improved version of Vortex. This time, they dubbed the virus as Flotera ransomware, or, as the virus calls itself, Ŧl๏tєгค гคภร๏๓ฬคгє.
This version is not significantly different compared to the original version – it still uses !!!-ODZYSKAJ-DANE-!!!.TXT as a ransom note and encrypts files using the same encryption routine. Two email addresses provided in the ransom note are flotera@2.pl and flotera@protonmail.ch. Flotera also adds .aes extensions to encrypted files and seeks to extort money from the miserable computer users who accidentally allow Flotera ransomware to be installed on the system.
Victims are advised to rely on data backups. Of course, data recovery measures should be taken only after Flotera virus removal. Luckily, virus researcher Michael Gillespie has found a decryption tool[7].
Known distribution methods
Ransomware viruses do not get into computer system out of thin air. Certain circumstances are needed in order for such malicious virus to hijack the PC system. The first reason allowing malicious programs sneak into your system easily is a lack of computer protection. If you do not have an anti-malware or anti-spyware software installed on your PC, nothing can stop the malicious program from infecting your PC.
Furthermore, the ransomware succeeds in infiltrating the system partially due to users' interaction. Malware is mostly distributed via email. As a result, cyber criminals manage to convince victims to open malicious email attachments just by using basic social engineering skills[8].
Finally, the ransomware can slither into the device with the help of exploit kits, but in such case, the victim needs to have some outdated software on the system. Security vulnerabilities in old programs allow exploit kits to execute code, and that is why you should keep all your programs up-to-date.
Remove Vortex virus today and recover your files
If either of previously-mentioned variations occupied your PC and your files are corrupted, do not waste any time and remove Vortex virus. Update the security program and perform the scan. If the virus blocks you from accessing it, take a look at the below instructions. It will help you regain access to the system and complete Vortex ransomware removal. After the malware is fully eradicated, proceed to data recovery.
Getting rid of Vortex virus. Follow these steps
Manual removal using Safe Mode
Run your PC in a Safe Mode with Networking to eliminate the crypto-malware safely. If you have never heard about Safe Mode with Networking and you do not know how to run your PC in it, follow these guidelines.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Vortex using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Vortex. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Vortex from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.You can recover the vast of lost data from a backup. Sadly, many computer users do not see regard as obligatory. They might be the most viable way to detec That is entirely wrong, because only backup can save you from a complete data loss. If you do not have a backup, try one of these techniques.
If your files are encrypted by Vortex, you can use several methods to restore them:
Use data recovery software: Data Recovery Pro
Most computer users find Data Recovery Pro useful, so we definitely recommend trying this tool in case Vortex malware corrupted your files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Vortex ransomware;
- Restore them.
Shadow Explorer
For data recovery, you can try ShadowExplorer tool. It can help you to detect and take advantage of Volume Shadow Copies, which can be used to recreate corrupted files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Vortex Decrypter
Users affected by this malware and seeking for a decryption tool, should visit this link.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Vortex and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Danny Palmer. Ransomware: What would you do?. ZDNet. Technology News, Analysis, Comments and Product Reviews.
- ^ Advanced Encryption Standard. TutorialsPoint. Free Tutorials and Reference Manuals with Examples.
- ^ Get rid of computer threats. Usunwirusa. Security and spyware news in Polish.
- ^ Narzędzie do odzyskiwania klucza szyfrującego ransomware’u Vortex. Cert.pl.
- ^ From Darknet with Love: Meet Spora Ransomware. Emsisoft Blog. All about Cyber Security.
- ^ Graham Cluley. FBI: No, you shouldn’t pay ransomware extortionists. WeLiveSecurity. IT Security Site Covering the Latest News, Research, Cyber Threats and Malware Discoveries, with Insights from ESET Experts.
- ^ Michael Gillespie. Anyone hit by Vortex / Floreta #Ransomware, contact me. I'm able to decrypt files. Twitter. Source for news and communication.
- ^ How to recognize social engineering attacks?. UgetFix. Tutorials on How to Fix Computer Problems.





















