Search.bytefence.com (Removal Instructions) - May 2020 update
Search.bytefence.com Removal Guide
What is Search.bytefence.com?
Search.Bytefence.com – questionable search engine creating various issues for the user
Search.bytefence.com virus is a wrongly used phrase, and users should stop calling this search engine like that. It is a search tool that gets installed into user's browser after the user downloads and installs the ByteFence Anti-Malware software (developed by Byte Technologies LLC). It is part of the software and users always have the right to opt it out when installing the legitimate anti-malware program, however, not many users pay enough attention to the information provided by software installers[1].
Usually, the installer of ByteFence software suggests changing your homepage, new tab page, and default search settings, which means that all of them will point to that customized search engine. No matter if you're using Mozilla Firefox, Google Chrome, or another popular web browser, it is likely that its settings will be altered in order to make you use that certain search engine. Despite that its functionality is normal and it is unlikely to provide you with dangerous search results[2], you might not want to use it, and that is completely okay.
| Name | Search.bytefence.com |
|---|---|
| Type | Browser hijacker |
| Symptoms | The site becomes a default homepage, search engine, new tab and gets set as other particular preferences automatically. This suspicious engine also triggers Secured Search extension or Toolbar installation without asking for any permissions |
| Related | Bytefence Redirect is the main software that gets installed and triggers these additional browsing activities interfering symptoms by adding search engine-based tools |
| Distribution | Freeware installations, generally, cause infiltration of such rogue and questionable tools. The particular program comes with another software that is not always reliable and secure to use |
| Elimination | Search.bytefence.com removal should involve anti-malware tools in the case for any unwanted or possibly dangerous tools or apps |
| Repair | Recover systems' functions and affected files using proper repair tools like FortectIntego |
If you wish to remove Search.bytefence.com, you can easily do it on your own – just make sure that you carefully read the instructions given below the article. We prepared them in order to help you to complete the removal process without hassle.
Although this search engine is not that dangerous to use, there are many browser hijackers[3] that sneak into user's computers when bundled with random free programs, and users should be aware of them. Usually, they meddle with the parameters of Internet Explorer, Google Chrome, or Mozilla Firefox browser, just like the described ByteFence component does. Actually, the search engine that the aforementioned anti-malware tool promotes enters the system without CLEAR permission asked, and we do not think that it is a tolerable activity.
Sure thing, if you find it useful, you can use it, however, we noticed that many users start looking for Search.bytefence.com removal guidelines shortly after installing the related anti-malware software. Therefore, we usually advise users to use other anti-spyware or anti-malware tools designed for computer protection, because these programs do not configure browser's homepage, new tab, and default search settings for their own benefit.
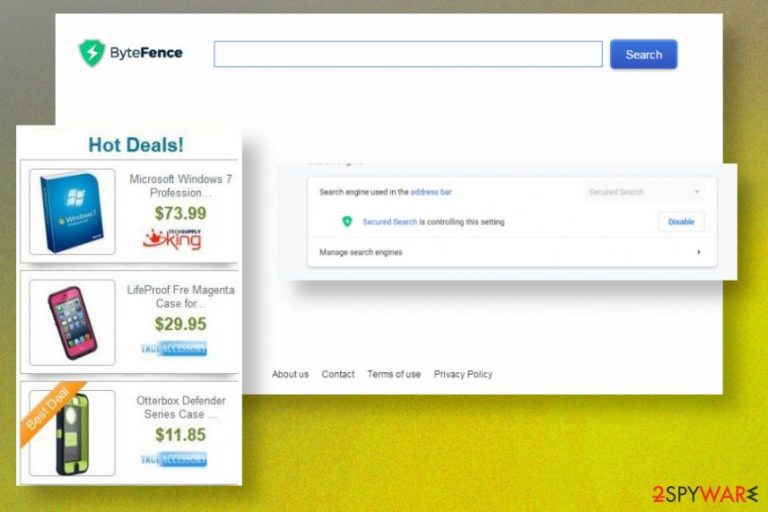
The described search engine might be pushing sponsored search results or even pop-up ByteFence ads to users in order to generate pay-per-click revenue[4]. However, as we said, if you weren't looking for a new search engine, there is hardly any reason to keep Search.bytefence.com in your system.
You can leave the anti-malware on the computer if you want and remove the component that controls your browser's settings only. Instructions on how to do it are provided below the article. But remember that even though this is not a Search.bytefence.com virus, there might be some intruders that cause all the issues with the performance and speed of the machine. so rely on proper AV tools and check the machine. 
Browser extension Secured Search by Bytefence – another suspicious tool
Search.bytefence.com hijacker is a known search engine that interferes with various processes on the machine, especially web browsing activities. However, it was recently reported that the Google Chrome browser receives more annoying application Secured Search extension. This search engine controls various settings on the browser too and even manages other applications, extensions, themes of the browser.
The plugin changes the default search engine, disables the user, and redirects all online searches to various search pages without disabling the particular extension itself. New tab settings also get altered, as for typical browser hijacker infection. Consumers cannot know where the tool came from, in most cases, because changes happen without permission or knowledge.
It is also not that easy to remove Secured Search since the extension is silently added by ByteFence Antivirus desktop application. Users are not aware and cannot easily fix all the issues since the main behavior is more likely controlled by the software.
Search.bytefence.com is the older version of such a hijacker belonging to ByteFence AV software/ PUP, so SecuredSearch is an automatic upgrade for the older hijacker. Both acting the same since the focus is traffic and redirects, injections on search result lists, promotional material. 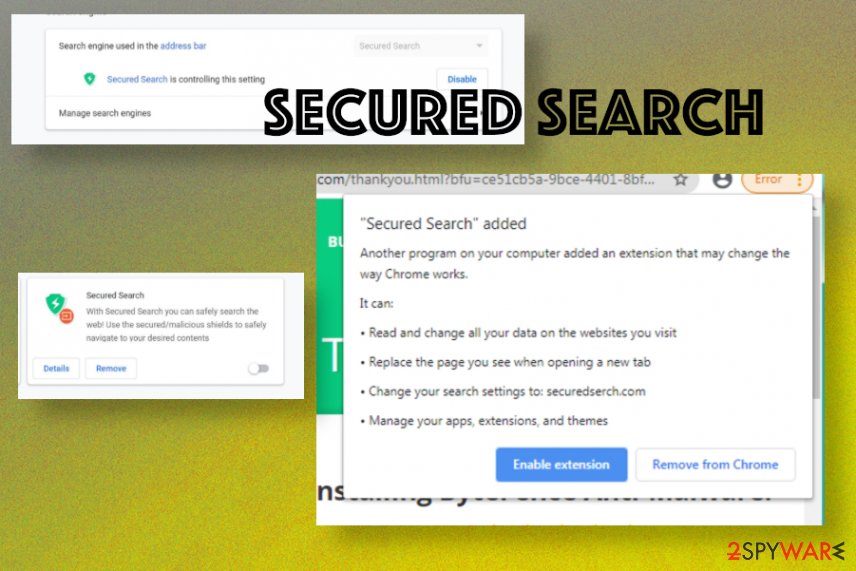
Technically, it is legal to do so, because such information is considered to be personally non-identifiable. However, small details such as your search queries can contain sensitive data, which is going to be collected along with all other terms and phrases you used in your searches. To stop such activity, you will only need to uninstall the described potentially unwanted program[5] (PUP) that sneaked along with the ByteFence software without your knowledge.
The installation of such search tools can be prevented
These browser hijackers usually come alongside the software that promotes them or other PUPs. These programs are connected using a software bundling technique, which allows to group and distributes several pieces of software together. The technique is considered to be legitimate; however, in most cases, installers of such software packs fail to adequately disclose the existence of additional programs, so consequently, users install them unknowingly and then start complaining about suspiciously behaving web browsers.
To prevent this, you should be very attentive when downloading free programs. Although the described search tool is not dangerous, there are other and more critical browser hijackers that are also distributed using the same bundling technique. When installing new programs, you should always choose Advanced or Custom options, and then deselect all programs that you do not want to be installed.
We suggest you avoid suspicious free programs and download managers because they are notorious for distributing bundled programs and they receive revenue each time such bundle is downloaded and installed. Do not choose Default or Standard settings, ever – they are usually filled with permissions to install extra programs and there's no way to reject them.
What is more, you should always download programs from their official websites as this will also diminish the risk of getting your computer infected. However, keep in mind that some free programs are designed specifically to lure people into downloading them so they would download PUPs as well. Therefore, trust your best judgment on what to download and what might seem suspicious.
Try to safely remove Search.bytefence.com from all the web browsers
The described search tool is likely to be controlled by a certain browser extension that was installed during the installation of ByteFence, but the anti-malware software could have modified your browser's shortcuts to making them point to Search.bytefence.com search engine.
Remember – these extensions are not viruses, however, their presence usually is objectionable, so if you no longer want to use the new search engine and get back to your old habits, you should remove Search.bytefence.com right away. You can use anti-spyware software the removal, or you can read these instructions and eliminate the intruder on your own.
If you need additional tips for Search.bytefence.com removal: rely on a proper tool that can securely check the machine for you; get PC optimizer application and to recover any affected data or corrupted files, programs on the machine. You may need to remove toolbars or extensions like Secured Search, so reset the browsers to default as well.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Search.bytefence.com. Follow these steps
Uninstall from Windows
The instructions provided below clearly describe all steps that you need to complete if you wish to remove the described search tool from your system. Do not forget to clean browser shortcuts as shown below. After completing these steps, you should start fixing each of the web browsers individually.
-
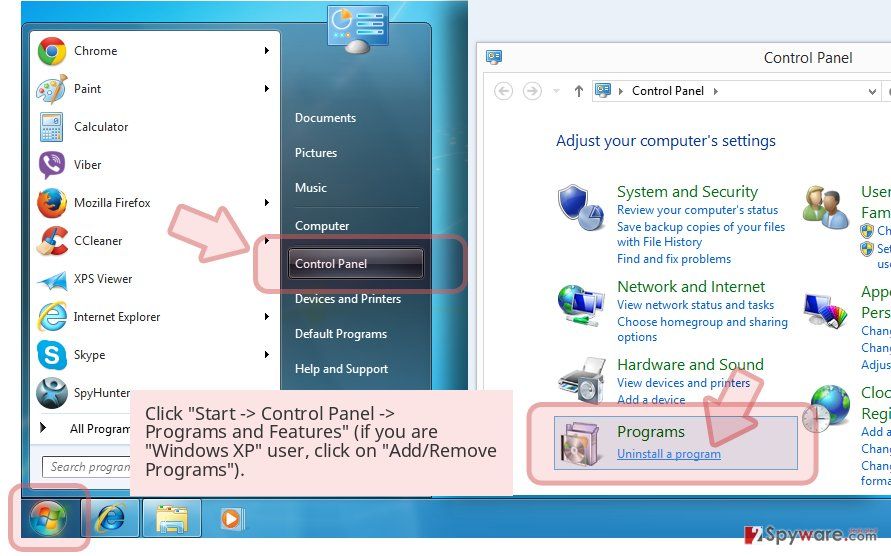
Click Start → Control Panel → Programs and Features (if you are Windows XP user, click on Add/Remove Programs).

-
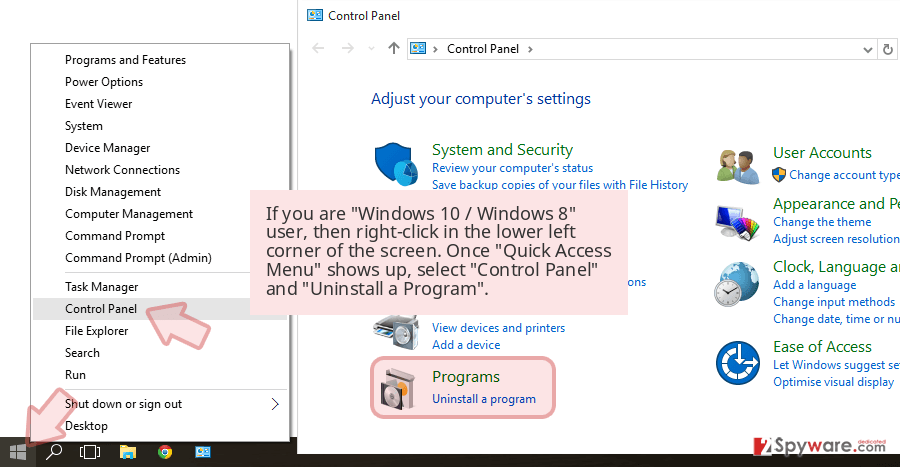
If you are Windows 10 / Windows 8 user, then right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.

-
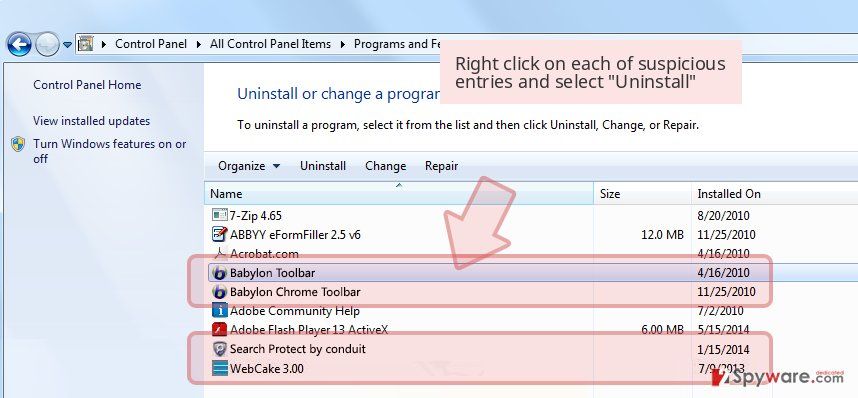
Uninstall Search.bytefence.com and related programs
Here, look for Search.bytefence.com or any other recently installed suspicious programs. -
Uninstall them and click OK to save these changes.

Delete from macOS
-
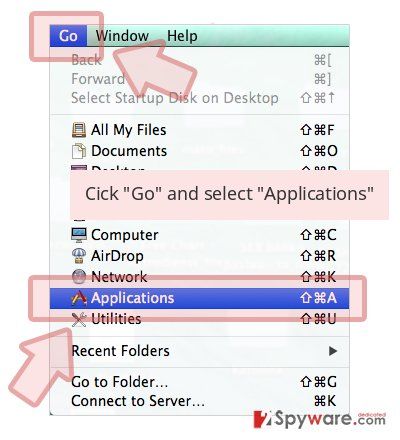
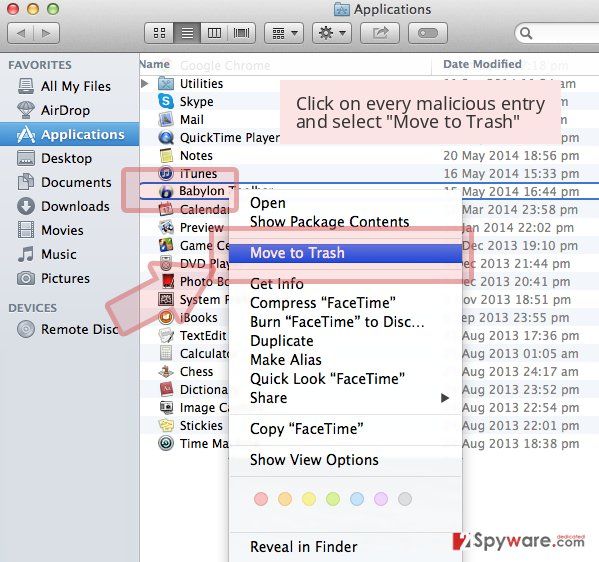
If you are using OS X, click Go button at the top left of the screen and select Applications.

-
Wait until you see Applications folder and look for Search.bytefence.com or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click Remove.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Settings > Privacy, search, and services..
- Under Clear browsing data, pick Choose what to clear.
- Select Cookies and other site data and Cached images and files. (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Remove next to any suspicious startup page.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.
- This will disable extensions and reset startup pages but will not delete bookmarks, saved passwords, or browsing history.

Remove from Mozilla Firefox (FF)
Firefox can start causing redirects to the described search engine as well, and if it does, you should carry out these instructions carefully.
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted extension and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Settings.
- Under Home, set your preferred homepage and new tab settings.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data and Temporary cached files and pages, then click Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
In Chrome, you should find one or couple browser extensions added without your knowledge, so make sure you remove them.
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all suspicious extensions related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
-
Remove dangerous extensions
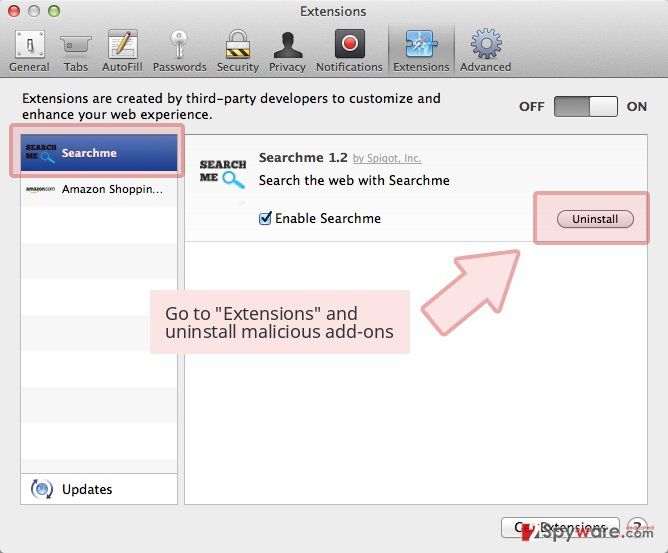
Open Safari web browser and click on Safari in menu at the top left of the screen. Once you do this, select Preferences.
-
Here, select Extensions and look for Search.bytefence.com or other suspicious entries. Click on the Uninstall button to get rid each of them.

-
Reset Safari
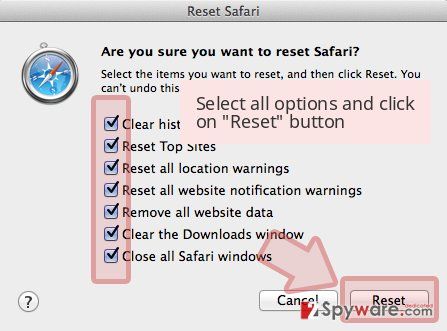
Open Safari browser and click on Safari in menu section at the top left of the screen. Here, select Reset Safari....
-
Now you will see a detailed dialog window filled with reset options. All of those options are usually checked, but you can specify which of them you want to reset. Click the Reset button to complete Search.bytefence.com removal process.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Search.bytefence.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting browser hijacker
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Chris Hoffman. How to Avoid Installing Junk Programs When Downloading Free Software. How-To Geek. For Geeks, By Geeks.
- ^ John Leyden. Search engine results increasingly poisoned with malicious links. The Register. Sci/Tech News for the World.
- ^ Gabriel E. Hall. What are browser hijackers and how to remove them. 2-Spyware. Information About Viruses and Cyber Security News.
- ^ Pay-per-click. Wikipedia. The Free Encyclopedia.
- ^ Classifying Potentially Unwanted Applications. F-Secure Labs. Information Source for New Virus Hoaxes and False Alerts, with Searchable Virus and Hoax Description Database.