Tapxchange.com (Removal Guide) - Nov 2015 update
Tapxchange.com Removal Guide
What is Tapxchange.com?
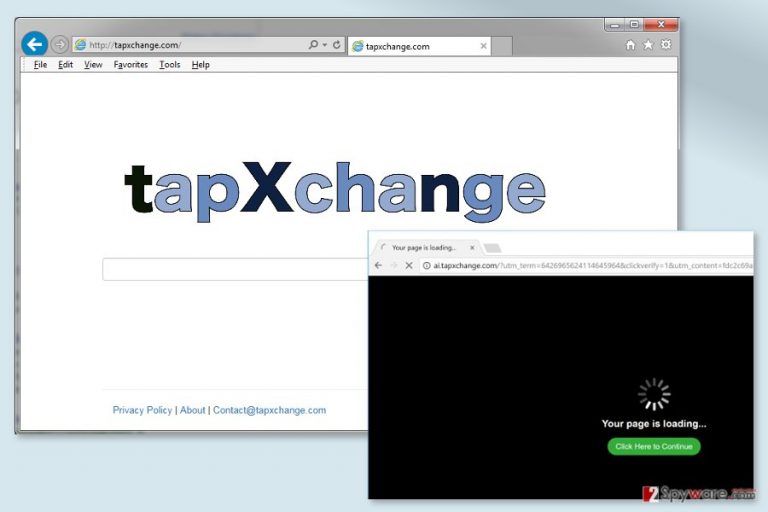
Tapxchange.com virus might take control over Chrome, Firefox, IE and other web browsers
Tapxchange.com is a search engine that belongs to the group of browser hijackers.[1] This potentially unwanted program (PUP) spreads in software bundles and alters targeted browser’s settings in order to cause suspicious activities, such as controlling search results, delivering ads, tracking information,[2] etc.
Due to the sneaky distribution technique, the hijacker might enter the system unnoticed. However, users can easily notice the signs of PUP. Once they open the affected browser, they might find the changed main page and default search engine.
Tapxchange.com looks safe, and it is similar to any other search engine – and an inexperienced PC user would never even think that there is something suspicious about this search engine. The issue is, this website does not provide relevant search outcomes. It provides altered search results, which lead to untrustworthy third-party databases.
It might redirect to websites that may try to convince you to install questionable programs or updates to your PC. Be cautious and reject such offers, because third-party sites sometimes promote infected programs. Of course, we cannot guarantee that every page you may be redirected to is entirely unsafe; but the bigger part of such redirections are unreliable.
Thus, we suggest scanning the computer with FortectIntego or another anti-malware program that can remove Tapxchange.com from the device entirely. Once the hijacker is gone for good, you will be able to set your preferred homepage, search engine, and browse the web safer.
The virus might also redirect people to ai.tapxchange.com and other suspicious websites. Usually, they promote questionable content. However, you might also end up on tech support scam or phishing site.
Apart from these suspicious and annoying activities, this PUP might also collect particular information about users. Browsing-related information is useful for delivering targeted ads and gaining advertising-based revenue from the clicks. In order to achieve this goal he hijacker might collect:
- IP address;
- technical information about computer, OS, and browser;
- search keywords;
- browsing history;
- clicked ads;
- time spent on particular sites or pages;
- etc.
Often developers of such programs share aggregated information with third parties. Who are they and what they are going to do with your profile is unknown. Most likely they will flood your browser with more commercial content. However, the worst scenario is identity theft. Thus, to avoid that you should start Tapxchange.com removal ASAP.
Browser hijacker spreads in an indirect way
Tapxchange.com is frequently being attached to other programs and spread together with them. Such pack of programs is called a software bundle. Bundling is a very popular method nowadays to spread potentially unwanted applications (browser hijackers, adware, plug-ins, add-ons, and browser extensions).[3]
The developers of PUPs use this distribution method because it is very efficient way to inject their products to users' computers' unnoticeably. Thus, the hijacker might easily become a problem for users all over the world, from Sweden[4] to Japan and United States.
The software bundle usually hides agreements to install such attachments by concealing them under “default” and “standard” installation modes. Instead of choosing these options, you should select the other option – either “advanced” or “custom.” By deselecting third-party apps, you can prevent not only Tapxchange.com hijack but the entrance of other PUPs too.

Frequently Asked Questions (FAQ)
Question: I am terrified that some malicious program has infected my computer. My homepage has suddenly changed to Tapxchange.com, and it displays very suspicious results! What is wrong with my computer?
Answer: Please, calm down; there is nothing much to worry about. You have probably installed some freeware on your computer that contained Tapxchange.com PUP. It is not a malicious program because it does not cause harm itself. It only seeks to increase rates of its sponsors' websites' web traffic and redirects people who use Tapxchange.com to these sites every time as they click on a search result generated by this fake search engine. This program can be easily removed from your system.
Question: Tapxchange.com search results has been redirecting me to websites that are not associated with my search keywords. I want to remove this search engine from my browser. What should I do?
Answer: We assume that Tapxchange.com virus has hijacked your system without your knowledge. The only way to remove this website from your browser is to uninstall the Tapxchange.com browser hijacker. We have provided two removal methods below this article so that you can uninstall it either manually or automatically. Good luck and stay safe!
Removal instructions of the Tapxchange.com virus
To remove Tapxchange.com from the machine, you need to choose between automatic and manual elimination options. The instructions how to get rid of the virus manually you can find below. Keep in mind that this method requires patience and attentiveness. Thus, if you are in a rush, we suggest opting for the automatic method.
Automatic Tapxchange.com removal is performed using anti-malware or anti-spyware.[5] In order to delete hijacker and all its components, you need to install your preferred program, update it and scan the system. Once security tool finishes the scan, you will be able to set your preferred homepage, search engine and customize your browser.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Tapxchange.com. Follow these steps
Uninstall from Windows
Manual removal guidelines are presented below. Please follow them carefully in order to get rid of all hijacker-related components.
-
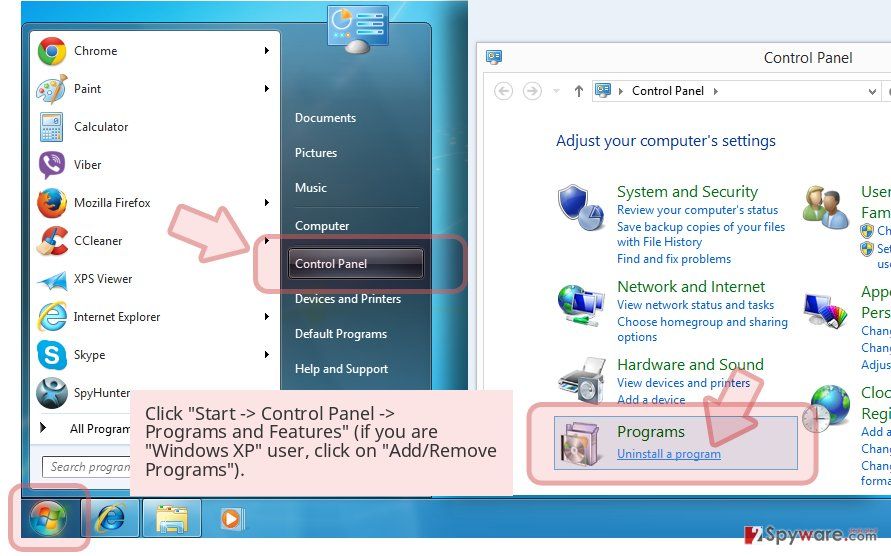
Click Start → Control Panel → Programs and Features (if you are Windows XP user, click on Add/Remove Programs).

-
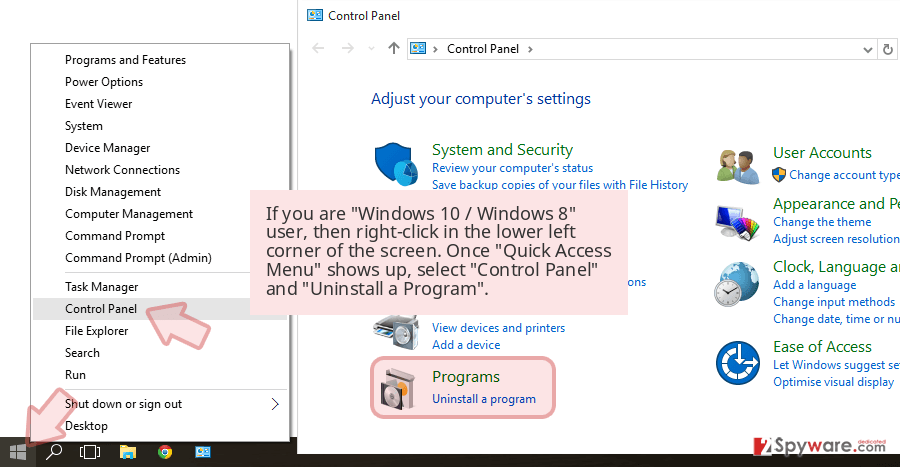
If you are Windows 10 / Windows 8 user, then right-click in the lower left corner of the screen. Once Quick Access Menu shows up, select Control Panel and Uninstall a Program.

-
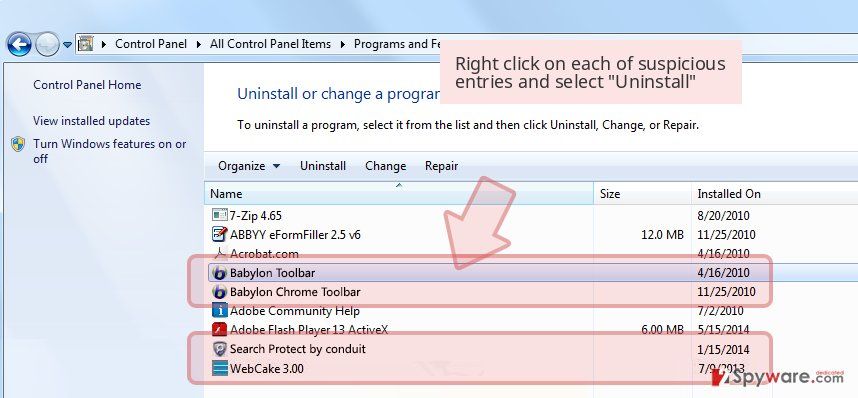
Uninstall Tapxchange.com and related programs
Here, look for Tapxchange.com or any other recently installed suspicious programs. -
Uninstall them and click OK to save these changes.

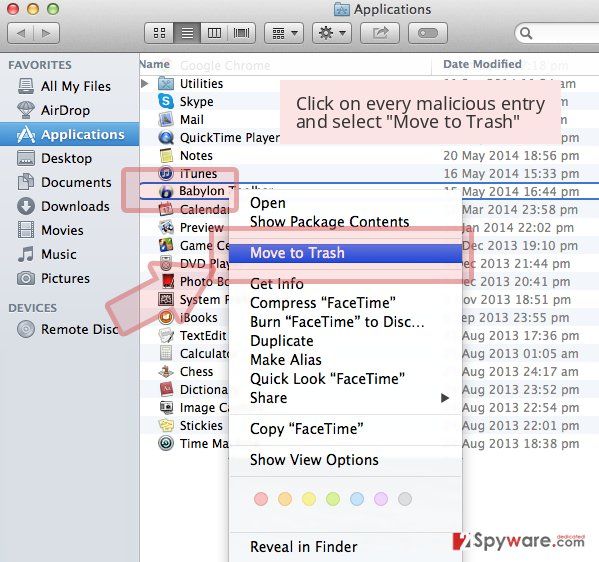
Delete from macOS
-
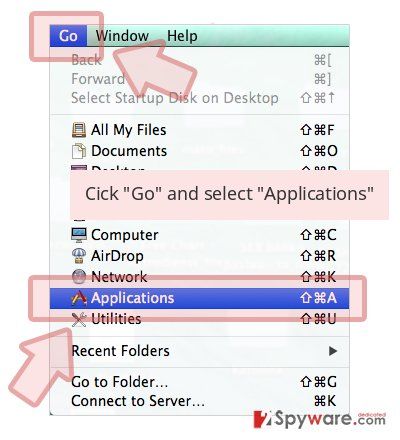
If you are using OS X, click Go button at the top left of the screen and select Applications.

-
Wait until you see Applications folder and look for Tapxchange.com or any other suspicious programs on it. Now right click on every of such entries and select Move to Trash.

Remove from Microsoft Edge
Follow the instructions below to delete the Tapxchange.com virus from the Edge entirely.
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click Remove.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Settings > Privacy, search, and services..
- Under Clear browsing data, pick Choose what to clear.
- Select Cookies and other site data and Cached images and files. (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Remove next to any suspicious startup page.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.
- This will disable extensions and reset startup pages but will not delete bookmarks, saved passwords, or browsing history.

Remove from Mozilla Firefox (FF)
In order to get rid of all suspicious components related to the hijacker, you need to uninstall suspicious browser extensions and reset Mozilla Firefox.
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted extension and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Settings.
- Under Home, set your preferred homepage and new tab settings.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data and Temporary cached files and pages, then click Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
In order to eliminate Tapxchange.com entirely, you need to follow the guidelines below:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all suspicious extensions related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

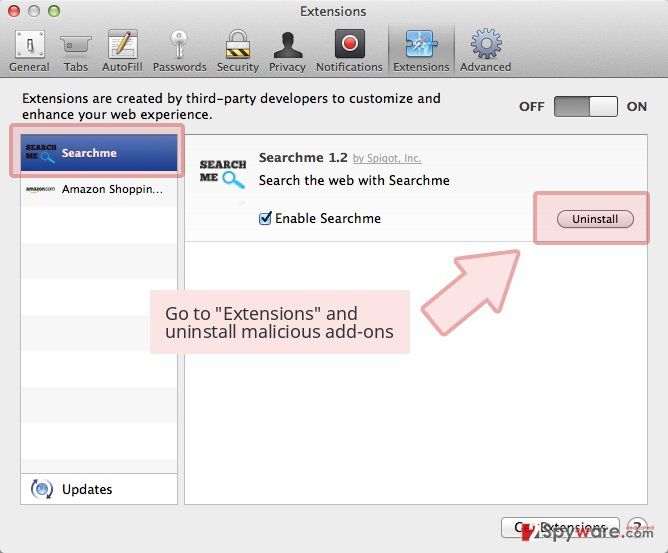
Delete from Safari
-
Remove dangerous extensions
Open Safari web browser and click on Safari in menu at the top left of the screen. Once you do this, select Preferences.
-
Here, select Extensions and look for Tapxchange.com or other suspicious entries. Click on the Uninstall button to get rid each of them.

-
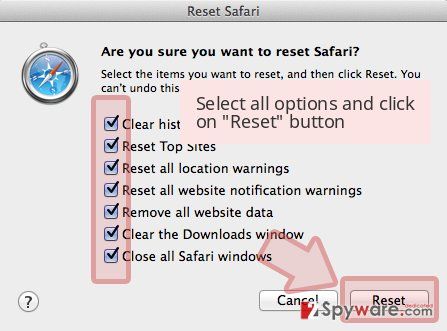
Reset Safari
Open Safari browser and click on Safari in menu section at the top left of the screen. Here, select Reset Safari....
-
Now you will see a detailed dialog window filled with reset options. All of those options are usually checked, but you can specify which of them you want to reset. Click the Reset button to complete Tapxchange.com removal process.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Tapxchange.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting stealing programs
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Browser hijacker (hijackware). TechTarget. Latest technology news and global network of technology-related blogs.
- ^ Trackography. Me and my Shadow. The official website of the data tracking control project.
- ^ Chad Whitley. Risks to Watch For When Downloading & Installing Free Software. Digital Citizen. Tutorials, reviews, news and other articles about productivity, entertainment, security, smarthome, smartphone and health.
- ^ UtanVirus. UtanVirus. The website about computer viruses for Swedish users.
- ^ Anti-spyware. Computer Hope. The website about computers, tutorials and help.