Angry ransomware (virus) - Recovery Instructions Included
Angry virus Removal Guide
What is Angry ransomware?
Angry ransomware encrypts users' files and asks them to pay if they want to see them again
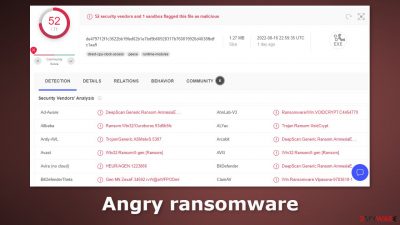
Angry ransomware is a file-locking virus. It is a variant of VoidCrypt ransomware family which has been detected in 2020. The dangerous program uses complicated encryption[1] algorithms to lock users' personal files, like photos, videos, and documents. The main purpose of such intruders is to extract money from desperate victims.
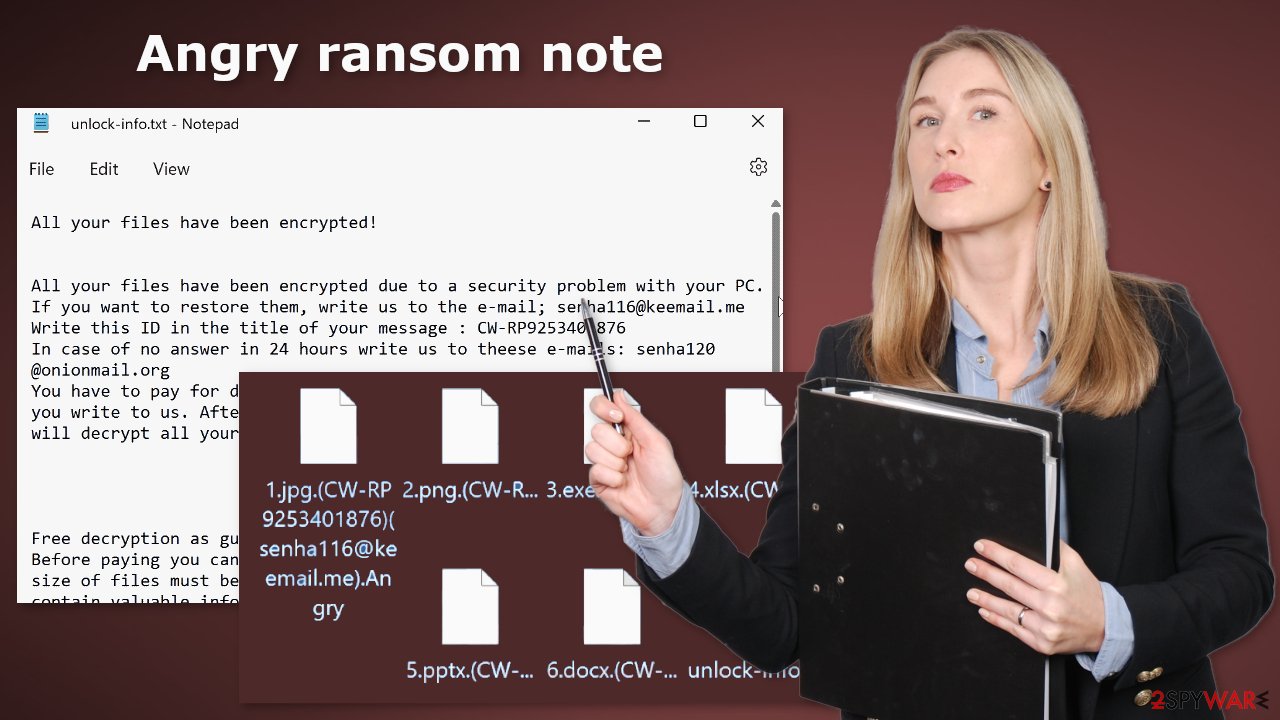
The affected files are appended with the .Angry extension, along with a unique ID and the cyber criminals' email address. So if a file was previously named picture.jpg. After encryption, it would look like this – picture.jpg.(uniqueID)(senha116@keemail.me).Angry. After the encryption process is complete, a ransom note unlock-info.txt gets generated on the machine.
| NAME | Angry |
| TYPE | Ransomware, cryptovirus, data locking malware |
| MALWARE FAMILY | VoidCrypt ransomware |
| DISTRIBUTION | Infected email attachments, torrent sites, malicious ads, drive-by downloads |
| FILE EXTENSION | .Angry |
| RANSOM NOTE | unlock-info.txt |
| FILE RECOVERY | It is almost impossible to recover the files if you do not have backups; in this guide, you will find third-party options for file recovery |
| MALWARE REMOVAL | Scan your machine with anti-malware software to eliminate the malicious files |
| SYSTEM FIX | Windows reinstallation can be avoided with FortectIntego maintenance tool, which can fix damaged files |
The ransom note
The full unlock-info.txt ransom note reads as follows:
All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail; senha116@keemail.me
Write this ID in the title of your message : –
In case of no answer in 24 hours write us to theese e-mails: senha120@onionmail.org
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.Free decryption as guarantee
Before paying you can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Angry ransomware developers want people to pay a ransom to get their data back. They want it to be paid in cryptocurrencies,[2] and more specifically – Bitcoin. Cybercriminals choose this method because it provides anonymity. They also say that the faster victims contact them, the smaller the amount. By doing this, threat actors are trying to pressure users into acting before thinking clearly.
We strongly advise against contacting cybercriminals, let alone paying them because they cannot be trusted. Many previous ransomware victims have come forward and revealed that they never received the promised decryption tools after paying for them. Besides, once you send cryptocurrencies to another wallet, it is impossible to get them back.
Distribution methods
To avoid ransomware attacks in the future, it is important to learn how they are spread. One of the most common ways people get infected is by installing “cracked” software.[3] Users visit Torrent websites, and peer-to-peer file-sharing platforms looking for programs to download for free. However, these platforms are unregulated so it is impossible to know if the files you are downloading do not contain any malicious ones.
It is best to use official web stores and developer websites whenever you are looking for new software. Apps that get listed on web stores have to go through an extensive review process. It might get costly but you may save in the long run by keeping your system running smoothly.
Another channel used by criminals to distribute their malicious programs is email. Usually, the malicious files can be inserted in a malicious link or infected attachment. That is why it is best to never open attachments from unknown senders. Open links and attachments sent only from your friends.
The last thing you should know about is the importance of keeping your operating system and software updated. Hackers can use software vulnerabilities to deliver their malicious programs. Software developers regularly release security patches that are meant to fix any security holes. You should install them as soon as they come out.
Ransomware removal
If the machine is not located at your workplace but in your home, plugging out the ethernet cable is enough to disconnect from the network. You have to do this if other devices use the same network because they can be infected too.
After that, you have to remove the malicious files that are performing the tasks in the background. If you try to recover your data first, it can result in permanent loss. Also, the files can keep getting encrypted again and again until you eliminate the cause. It would be best if you did not try removing it yourself unless you have IT knowledge.
Using anti-malware tools like SpyHunter 5Combo Cleaner or Malwarebytes to scan your system will give you the best chance of removal being complete. This security software should find all the related files and entries and remove them automatically for you. If you cannot open security software, the code might be preventing the program from being able to function. Proceed with accessing Safe Mode, where you will be able to deploy the antivirus safely:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
![Update & Security Update & Security]()
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
![Advanced options Advanced options]()
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
File recovery using third-party software
Third-party programs cannot always decrypt the files, but you should at least try it. Before proceeding, you have to copy the corrupted files and place them in a USB flash drive or another storage. And remember – only do this if you have already removed Angry ransomware.
It is devastating to know, but if you do not have backups, this might be your only chance at recovery because only hackers hold the decryption key, which can unlock your files.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Angry ransomware Angry ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
The operating system can be damaged after an attack
Performance, stability, and usability issues, to the point where a full Windows reinstall is required, are expected after malware infection. These types of infections can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not able to repair it.
This is why FortectIntego was developed. It can fix a lot of the damage caused by an infection like this. Blue Screen errors,[4] freezes, registry errors, damaged DLLs, etc., can make your computer completely unusable. By using this maintenance tool, you could avoid Windows reinstallation.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
Additional instructions are provided for corporate environments on isolating the infected machine and stopping the malicious program from affecting the entire network at the bottom of this post. You will also find information on where you can report your attack. Doing it will give you a better chance of having your perpetrators caught.
Getting rid of Angry virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ What is encryption? Data encryption defined. Ibm. Data Protection.
- ^ Kate Ashford. What Is Cryptocurrency?. Forbes. Investment Blog.
- ^ Georgina Torbet. 5 Security Reasons Not to Download Cracked Software. Makeuseof. Security Blog.
- ^ Chris Hoffman. Everything You Need To Know About the Blue Screen of Death. Howtogeek. Technology Magazine.





















